Google has open-sourced JSIR, a high-level intermediate representation (IR) for JavaScript built on the MLIR framework. Launched via an RFC on April 6, 2026, JSIR preserves every detail from the JavaScript AST, enabling perfect round-trip fidelity between source code, AST, and IR. It models control flow using MLIR regions and supports dataflow analysis out of the box. Already battle-tested in Google’s production environment for code analysis and transformations, the repo sits at github.com/google/jsir.
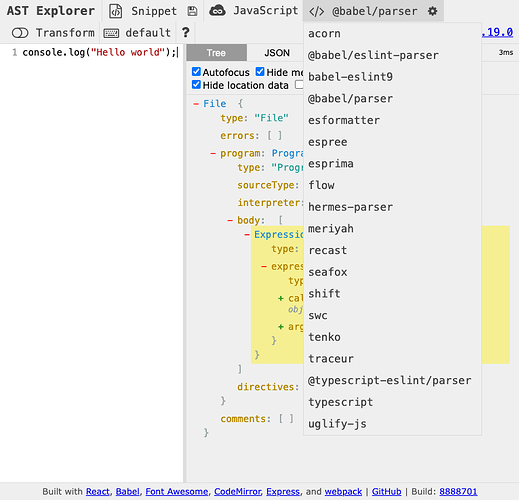
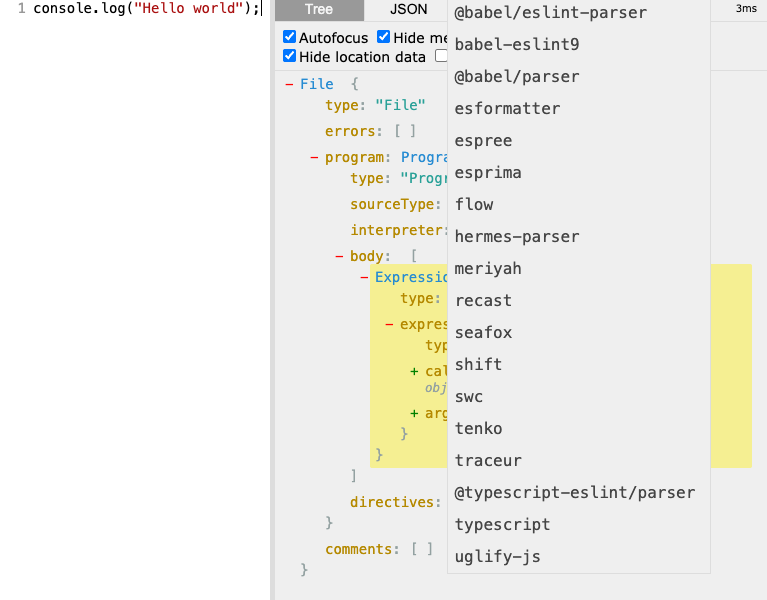
This matters because JavaScript tooling has long been bottlenecked by ASTs. Tools like Babel, ESLint, and Webpack parse to ESTree-compliant ASTs for traversal, transpilation, optimization, and bundling. AST Explorer lists over 70 parsers, but none expose an IR. Complex tasks—think control flow graphs (CFGs) or precise dataflow—force devs to hack around AST limitations, often losing fidelity or round-trip capability.
Why Build JSIR Now?
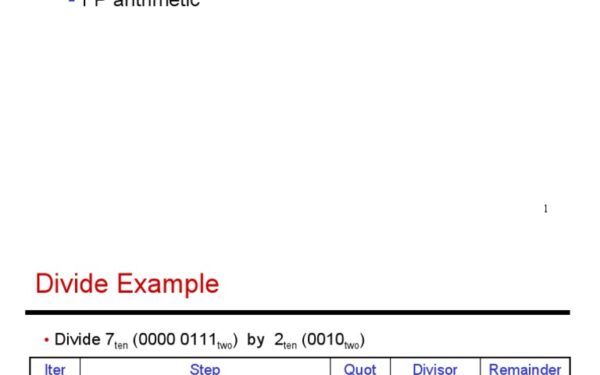
The compiler world shifts toward language-specific high-level IRs before dropping to LLVM. Rust and Swift analyze on their HIRs; projects like Clang IR, Mojo, and Carbon follow suit. JavaScript, powering 98% of websites (per W3Techs 2025 data), demands the same. ASTs excel at syntax trees but falter on semantics: no native CFG, weak dataflow support. JSIR fixes this by layering JS dialect on MLIR, Google’s extensible IR stack used in LLVM 19+.
Round-trip is key for source-to-source tools. Babel downgrades ES2025 to ES5; Closure Compiler shrinks code by 20-30% via dead-code elimination. Both regenerate JS from ASTs, risking mismatches. JSIR guarantees fidelity, opening doors to aggressive optimizations without breakage. Skeptically, will the JS community adopt? ASTs are entrenched—ESTree is a spec—but no IR exists, and MLIR’s modularity could lure V8/SpiderMonkey devs.
Google’s Real-World Wins and Security Angle
JSIR powers Google’s decompilation of Hermes bytecode—a Facebook VM used in React Native—to readable JS. It also drives deobfuscation, blending IR transforms with Gemini LLM. Their ICSE 2026 paper (SEIP track, April 15 presentation) details lifting obfuscated code to JSIR, analyzing flows, then reprinting clean JS. Hermes decomp yields 95% readability; deobf reverses tools like javascript-obfuscator, exposing malware payloads.
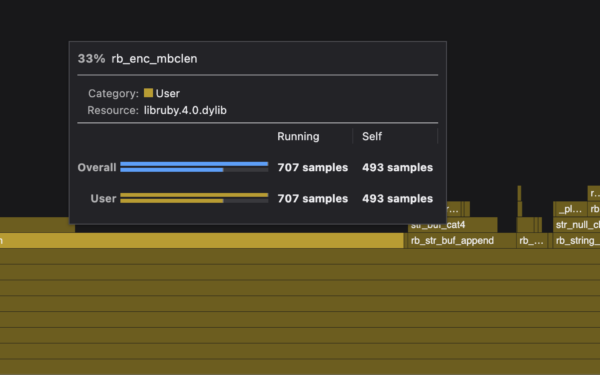
Security pros: JavaScript malware surged 40% in 2025 (per Sonatype), hiding in npm’s 2M+ packages. Deobfuscators struggle with dynamic eval or proxies; JSIR’s dataflow tracks variables across async/await, generators. Pair with LLMs? Promising, but LLMs hallucinate—IR grounds them. Implications extend: browsers could use JSIR for JIT warmup; Node.js for bundle analysis. Open-sourcing stabilizes it as public IR, unlike proprietary Google internals.
Design goals emphasize stability: public dialect spec, MLIR ops for JS builtins (e.g., js.call, js.await). Regions nest if/try/catch perfectly. Dataflow via MLIR’s SSA form catches dead stores, escapes. Expandable—future dialects for TypeScript or WebAssembly?
Caveats: Early days, 2026 RFC means nascent ecosystem. MLIR learning curve daunts JS devs used to Babel plugins. But Google’s skin in the game (internal deployment) signals commitment. If JSIR sticks, it standardizes advanced analysis, slashing reinvented wheels in security, perf, and devtools. Watch the repo stars; traction there predicts adoption.