Security researchers have developed a tool that uses symbolic execution and the Z3 theorem prover to automatically generate “magic” packets from BPF bytecode. This slashes reverse-engineering time for Linux malware from hours to seconds. Manual analysis of complex filters—often hundreds of instructions long—previously bottlenecked incident response. The approach treats bytecode as constraints, solving them backward to produce exact trigger packets.
Classic Berkeley Packet Filter (BPF) programs run in the Linux kernel to filter network traffic efficiently. Introduced in 1992 for tools like tcpdump, they use a simple virtual machine with just two registers: one accumulator and one index. Malware authors embed these filters in socket filters, making backdoors dormant until a precise packet arrives. This hides activity from user-space monitoring tools, as BPF executes deep in kernel space at wire speed.
BPFDoor: A Real-World Example
BPFDoor exemplifies the threat. Discovered in 2021, this Linux backdoor targets SSH servers and uses BPF socket filters to listen passively. Attributed to China-based Red Menshen (aka Earth Bluecrow), it activates only on specific packets with crafted headers, such as unusual TCP options or payload patterns. The actors have deployed it against telecoms, critical infrastructure, and government targets worldwide.
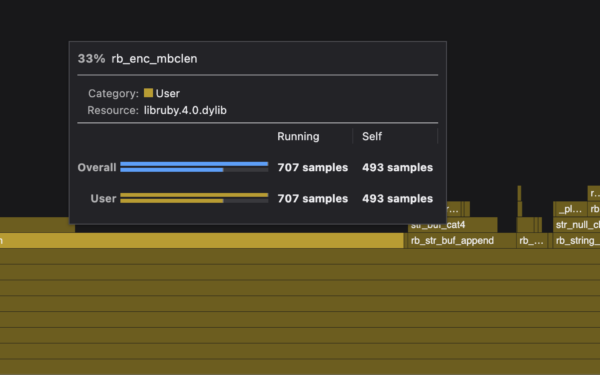
BPFDoor’s filter spans over 100 instructions in some variants, with nested jumps and bit manipulations checking packet fields like IP IDs, sequence numbers, and data offsets. Analysts previously disassembled this bytecode manually using tools like bpf_asm or Ghidra, then scripted packet crafters like Scapy. For a 20-instruction filter, this took minutes; for 100+, hours or days, especially under pressure during active intrusions.
Symbolic Execution Solves the Constraints
The new tool models BPF execution symbolically. Instead of concrete values, it tracks symbolic variables for packet bytes. Each instruction becomes a constraint: loads map buffer offsets to symbols, jumps become conditional branches, arithmetic ops create equations.
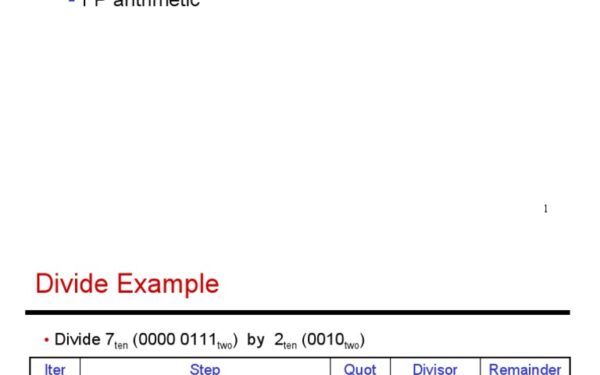
Z3, Microsoft’s SMT solver, then finds inputs satisfying the path to the “accept” state. Here’s the core workflow in pseudocode:
def generate_packet(bpf_bytecode):
state = SymbolicState() # Accumulator 'a', index 'x', pc=0, packet=SymBuffer(65535)
path_constraints = []
while state.pc < len(bytecode):
instr = parse_instr(bytecode[state.pc])
exec_symbolic(instr, state)
path_constraints.append(state.constraint)
if is_jump(instr):
# Fork paths symbolically
pass
solver = z3.Solver()
solver.add(And(path_constraints)) # Reach accept
solver.add(state.a == 0) # BPF accept condition
if solver.check() == sat:
model = solver.model()
return concrete_packet(model)
return NoneThey implemented this in Python, lifting BPF to an intermediate representation before feeding Z3. Tests on BPFDoor samples generated valid packets in under 10 seconds on a standard laptop, versus 2-4 hours manually. It handled loops and conditionals by path explosion mitigation—pruning infeasible branches early.
Context from similar tools: Projects like SymbexBAP or angr have applied symbolic execution to binaries, but BPF’s simplicity (no heap, fixed stack) makes it ideal. LLMs help decompile bytecode to pseudo-code first, but crafting packets remains manual— this closes that gap.
Implications and Limits
This matters because BPF backdoors persist. BPFDoor variants evaded detection into 2024, with over 50 samples analyzed by firms like Sandfly and Elastic. Faster triggering means quicker code execution analysis: dump memory, hook syscalls, trace C2. In red-team scenarios, it accelerates testing kernel filters.
Skeptical caveats: Not all filters are solvable. Obfuscated jumps, timeouts, or non-deterministic elements (like timestamps) stump Z3. Path explosion scales poorly beyond 200 instructions—real-world malware hits this. Kernel versions matter; classic BPF differs slightly across distros (e.g., RHEL vs. Ubuntu). No public repo yet, so reproducibility unverified.
Broader impact: As eBPF proliferates for security (Cilium, Falco), attackers may shift there—its Turing-complete verifier complicates analysis. Defenders should scan for suspicious sock_fprog() calls via eBPF tracing or auditd. Tools like this democratize analysis, but proliferation risks dual-use by attackers generating stealthier implants.
Bottom line: Automating packet generation removes a painful RE step, letting analysts focus on payloads and persistence. In a world of nation-state malware, seconds count—expect forks and integrations into frameworks like Wireshark or Volatility soon.