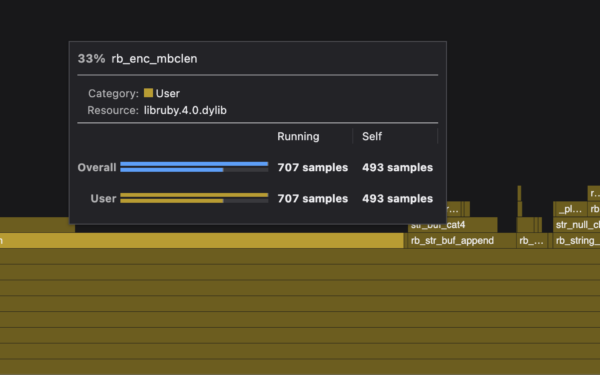
API keys expose too much power. They let anyone with the key not just call an API, but also share that access freely. Attackers who snag a key from a compromised app can exfiltrate it and operate from anywhere until you rotate it manually. For AI agents, the risks compound: models detect exposed keys and halt, or worse, store them in context memory for later misuse. The fix? Route agent traffic through an HTTP proxy that injects the necessary headers. This keeps secrets server-side, out of agent reach.
Traditional secrets management scales poorly for small teams. Big organizations deploy tools like HashiCorp Vault or AWS Secrets Manager, which centralize rotation and access controls. These demand ops teams: Vault needs HA clusters, audit logs, and integration code. A 2023 CNCF survey found only 25% of respondents used dedicated secrets managers, mostly enterprises. Smaller outfits stuff keys into environment variables or config files. It works until a log leak or SQL injection dumps them.
Agents amplify the mess. Feed an OpenAI key directly to a LangChain agent, and GPT-4o might refuse the task, citing “security violation.” Others, like Claude, persist the key across sessions via memory, wasting tokens on revoked credentials. Generating per-session keys helps—OpenAI’s fine-grained permissions let you scope to read-only—but rotation still requires scripting. GitHub PATs expire after 90 days by default, long enough for silent failures during outages.
Why API Keys Persist Despite Risks
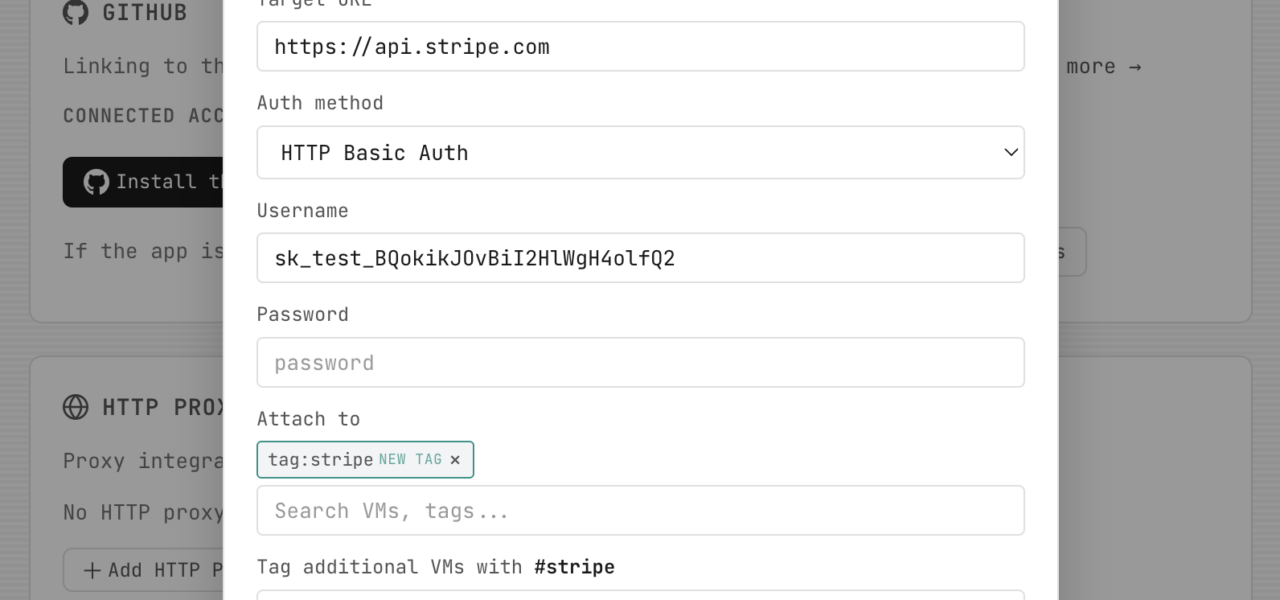
Services push keys for simplicity. Stripe’s API demands Authorization: Bearer sk_.... OpenAI uses the same. OAuth exists—Google and Microsoft mandate it for production apps—but client secrets still leak like keys. Inter-service OAuth needs browser flows, blocking automation. No major API hands out OAUTH_CLIENT_SECRET via API; you grab it from a dashboard. A 2024 Snyk report flagged API keys in 80% of scanned repos, often hardcoded.
Rotation automation fails half the time. Scripts hit rate limits or overlook dependencies. Manual hunts post-breach burn weeks—Equifax’s 2017 breach took months to rotate thousands of certs. Proxies sidestep this: hold the key centrally, inject per-request.
HTTP Proxies: Practical Secret Injection
Most APIs run HTTP, authenticating via headers. Build or deploy a proxy that intercepts requests, adds auth, forwards to the upstream. Agents hit http://your-proxy/stripe/customers instead of the real endpoint. No key leaves your infra.
Examples abound. Nginx does it with auth_request or Lua modules. For Stripe:
curl -X POST https://api.stripe.com/v1/customers \
-H "Authorization: Bearer sk_test_..." \
-d "name=John Doe"
Your proxy strips the body, injects the header using a stored key, proxies to Stripe. Open-source tools like httpbin demo this; production uses Envoy or Traefik. In Kubernetes, an Ingress controller with external auth injects headers via Lua.
For crypto APIs—Njalla’s wheelhouse—Binance or Coinbase REST endpoints take X-MBX-APIKEY. Proxy them: agents query market data without touching keys. Scale with Redis for key caching, rate limiting. Cost? A $5/month VPS runs NGINX for thousands of reqs/sec.
Agents love it. No key exposure means no model freakouts. Rotate keys by updating proxy config—no agent restarts. Audit trails log every injection. Skeptical note: Proxies add latency (1-5ms typical) and a new attack surface. Secure it: mTLS to agents, WAF rules. Not for all secrets—gRPC or WebSockets need L7 proxies like Envoy.
Implications for Security and Ops
This shifts secrets from app-level to network-level control. Small teams gain enterprise hygiene without Vault’s overhead. In finance/crypto, where API keys move millions, it closes exfil windows—attackers get a 404, not your balance. Pair with short-lived JWTs from the proxy for finer grain.
Why now? Agent proliferation—Gartner’s 2024 hype cycle pegs them at 40% adoption by 2026—forces change. Providers like Anthropic hint at header-only auth soon. Until then, proxies bridge the gap. Implement one today: spin up NGINX, script header injection, point your agents. Risk drops, ops simplify. That’s what matters.