Chrome 146 now rolls out Device Bound Session Credentials (DBSC) publicly for Windows users, with macOS support coming soon. This Google-led protocol binds browser session cookies to specific hardware, rendering stolen cookies useless to attackers. Session theft from malware remains a top threat—infostealers like LummaC2 snag cookies from Chrome’s storage, granting passwordless account access that lasts as long as the cookie, often weeks or months.
Malware infects via phishing or drive-by downloads, then scrapes browser files and memory. No software fix stops this on Windows, macOS, or Linux; TPM or Secure Enclave hardware is essential. Past defenses relied on server-side heuristics to flag abuse after theft—think risk-based authentication spotting logins from odd IPs or user agents. Attackers evade these with proxies and cookie laundering.
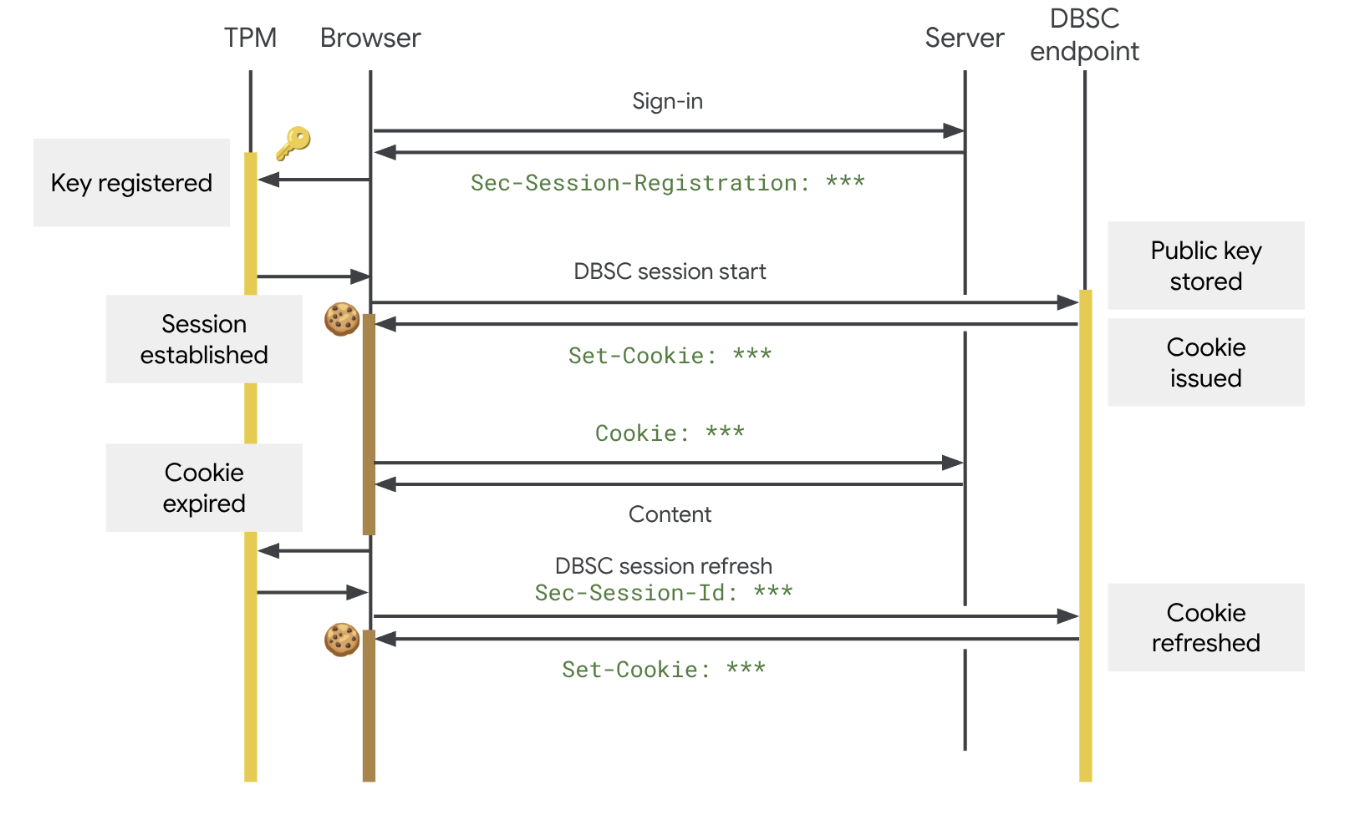
DBSC flips the script to prevention. Chrome generates a non-exportable public-private key pair using Windows TPM 2.0 or macOS Secure Enclave. During login or refresh, the browser proves private key possession to the site’s DBSC endpoints via challenge-response. Servers then issue short-lived cookies (e.g., hours) tied to that proof. Stolen cookies expire fast without the key.
How It Integrates
Sites add two backend endpoints: one for key registration (public key + proof), one for session refresh. Frontends stay unchanged—Chrome handles key ops, cookie rotation, and fallback to plain cookies. Google tested an early version over the past year on its services; protected sessions saw sharp theft drops, though exact figures remain undisclosed.
Adoption starts with Google’s ecosystem—Gmail, YouTube—but open to all via the DBSC spec. Small sites implement with libraries; big ones like Microsoft or banks could follow if Chrome’s 65%+ market share sways them. No client changes needed beyond Chrome updates.
Why It Matters, Limitations Exposed
This kills a multi-billion-dollar cybercrime pipeline. Stealer logs from breaches like 2023’s 2.5 billion credential dumps trade on dark web markets for $1-10 per account. DBSC neuters high-value targets like finance apps. Users on clean devices gain seamless protection; enterprises cut breach response costs.
Skeptical lens: Hardware binding isn’t new—Apple’s Passkeys and FIDO2 use similar attestation. But DBSC targets cookies specifically, sidestepping multi-device woes (one key per device). Cross-browser? Nope, Chrome-only for now; Firefox and Safari lag. Sites must opt-in, so legacy sessions remain vulnerable.
Privacy trade-off: Sites learn device fingerprints via attestation certs, potentially worsening tracking. Revocation? Users can reset keys in Chrome settings, forcing re-auth. Edge cases like TPM failures or VM escapes could bypass, but real-world malware rarely cracks hardware enclaves.
Bottom line: DBSC raises the bar against infostealers, forcing attackers to live compromises over cookie grabs. Expect 20-50% theft reduction where adopted, based on Google’s pilots and similar token-binding trials. Roll it out on high-risk sites now—Windows users, update Chrome and push your services to integrate. Without broad adoption, it’s a half-measure in the theft arms race.