OpenSSH 9.9p1, released on September 5, 2024, now logs warnings whenever an SSH connection relies on key exchange (KEX) algorithms vulnerable to quantum attacks. This affects nearly all current SSH setups, as OpenSSH flags classics like curve25519-sha256, diffie-hellman-group-exchange-sha256, and diffie-hellman-group16-sha512. The move forces sysadmins to confront post-quantum cryptography (PQC) sooner than many expected.
Quantum computers running Shor’s algorithm could shatter elliptic curve Diffie-Hellman (ECDH) and RSA-based key exchanges in hours, not eons. Current systems use 256-bit elliptic curves or 3072-bit Diffie-Hellman groups—secure against classical supercomputers, but toast against a cryptographically relevant quantum machine with 1-10 million stable qubits. No such beast exists yet; today’s leaders like IBM’s Condor top out at 1,121 noisy qubits. But the NSA warns of “harvest now, decrypt later” attacks: adversaries snag encrypted traffic today, crack it post-quantum.
Why OpenSSH Acts Now
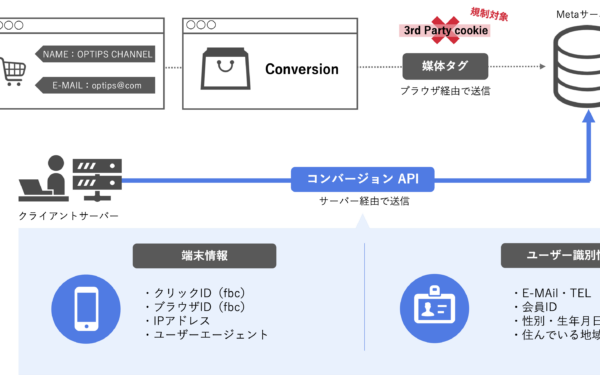
SSH secures 80% of internet servers, per Shodan scans, handling everything from Git pushes to cloud VMs. Long-lived keys mean a quantum break years from now exposes past sessions. NIST finalized PQC standards in August 2024: ML-KEM (ex-Kyber) for key encapsulation, ML-DSA for signatures. OpenSSH integrates ML-KEM-768 hybrids like mlkem768x25519-sha256, blending quantum-safe encapsulation with classical ECDH for safety.
Prior to 9.9p1, OpenSSH offered sntrup761x25519-sha512@openssh.com—a hybrid using NTRU Prime. Now, it defaults to warning on non-PQC KEX if the server supports PQC options. Client-side logs say: “kex curve25519-sha256 uses non-PQC algorithm (quantum risk).” Servers log similarly. Disable with LogLevel QUIET, but that’s kicking the can.
This isn’t hype. Google rolled PQC into Chrome in 2024; Cloudflare tests it live. OpenSSH devs, led by Markus Friedl, push because PQC migration spans years—think firmware updates on routers from 2015. A 2023 survey by the Open Quantum Safe project found 40% of TLS servers still use RSA-2048, prime quantum targets.
Implications for Security Teams
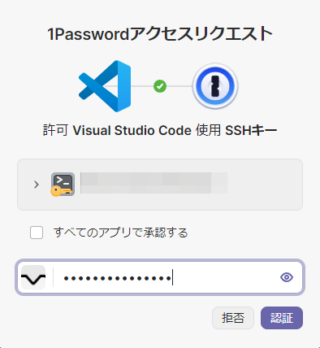
Upgrade pain hits first. Servers need OpenSSH 9.5+ for PQC support; clients 9.9p1 for warnings. Enable via ssh_config:
KexAlgorithms sntrup761x25519-sha512@openssh.com,curve25519-sha256Put PQC first for negotiation preference. Test interoperability—older clients drop connections if PQC-only. Benchmarks show ML-KEM-768 adds 1-2 ms latency on modern CPUs, negligible for SSH but stacks up in high-volume setups.
Skeptical take: Overkill today? Yes, quantum threats loom 5-15 years out, per experts like Chris Peikert. But inertia killed Triple-DES; SSH won’t repeat that. Why it matters: Forces protocol evolution. Without warnings, admins ignore PQC like Y2K patches. Post-quantum SSH protects crown jewels—API keys, session data—in a world where China and Russia hoard qubits.
Broaden out: Expect ripple effects. AWS, Azure push PQC-enabled AMIs. WireGuard integrates Kyber hybrids. Crypto wallets like Ledger eye PQC signatures. Cost? Negligible long-term; Intel’s AVX-512 speeds ML-KEM 10x. Risk? Vendor lock-in if standards shift, but NIST’s track record holds.
Bottom line: Update to OpenSSH 9.9p1. Audit ssh -Q kex output. Prioritize PQC in configs. Quantum won’t wait for perfection—this warning buys time before mandates hit.