Adobe’s Creative Cloud applications quietly edit your system’s hosts file to verify legitimate installations. This anti-piracy tactic blocks specific domains and serves as a marker for the full CC suite, distinguishing it from standalone pirated copies like Photoshop. Users on Hacker News spotted this after noticing 15-20 new entries appended to the file, such as 127.0.0.1 na1r.services.adobe.com and 127.0.0.1 lm.licenseservice.adobe.com.
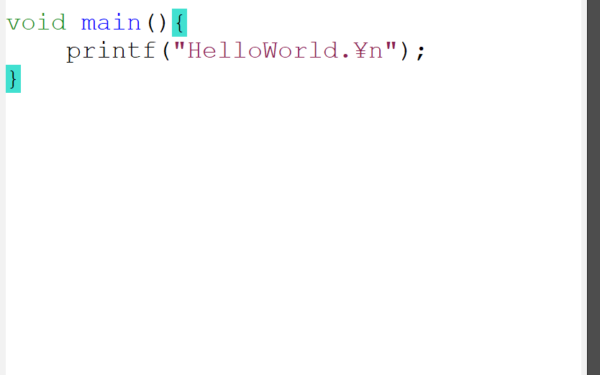
The hosts file—located at C:\Windows\System32\drivers\etc\hosts on Windows, or /etc/hosts on macOS and Linux—overrides DNS resolution. Legitimate software uses it sparingly, but pirates exploit it heavily. Crackers add lines like 0.0.0.0 activate.adobe.com to block Adobe’s activation servers, faking a licensed state. Adobe counters by scanning for these blocks and now writes its own entries. These point Adobe licensing domains to localhost (127.0.0.1), preventing pirated tools from mimicking servers. Only the CC desktop app adds this full set, so isolated pirated apps fail the check.
How the Detection Works
Adobe apps require admin privileges to append these lines—often granted during install without explicit ongoing consent. On Windows, they open the file in append mode and add entries silently. If you uninstall CC, the entries linger unless manually removed. Restarting the app re-adds them if missing.
This matters because it ties licensing to system persistence. Pirated standalone Photoshop lacks the CC app’s “genuine check” service, which manages these entries. Adobe’s “Genuine Software Integrity Service” (AGS) runs in the background, phoning home weekly. If hosts blocks its domains or lacks Adobe’s markers, it flags the install as fake, disabling features or prompting payment.
Numbers tell the story: Adobe claims 90% of Photoshop users run pirated versions in some markets. This hosts hack plugs that leak—standalone cracks bypass activation but fail runtime checks. Since 2022 updates, reports spiked on forums like Reddit’s r/CrackSupport and HN, with users sharing before/after hosts diffs showing Adobe’s fingerprints.
Security and Privacy Risks
Software editing the hosts file screams red flags. Malware like DNS hijackers (e.g., 2017 WannaCry variants) use it to redirect traffic. Adobe’s changes could conflict with your VPN, ad-blockers, or custom entries—say, blocking a dev domain you need. Worse, it escalates privileges: CC apps request UAC elevation repeatedly, a vector for exploits if Adobe’s code has vulns.
Privacy hits too. AGS collects install IDs, hardware fingerprints, and usage data, sending to Adobe servers. EU regulators fined Adobe €1.5 million in 2023 over similar tracking without consent. Hosts mods ensure this telemetry flows, even if you firewall Adobe.
Skeptically, Adobe’s not wrong—piracy costs them $2.5 billion yearly, per their estimates. Fair play demands enforcement. But this low-level tamper feels like overkill. Alternatives exist: hardware-bound DRM like Denuvo or cloud-only validation. Hosts editing erodes OS integrity, especially on shared machines.
What Users Should Know
Legit subscribers: Monitor your hosts file. Use tools like
sudo cat /etc/hosts | grep adobe on Unix or Notepad++ on Windows. Backup before installs. If conflicts arise, comment out lines with #.
Pirates: Expect failure. Tools like AMTEmu or Zii patch activation but miss hosts persistence. Full CC emulation requires reverse-engineering AGS—rarely stable beyond months.
Everyone: Distrust software demanding hosts writes. It signals desperate DRM. Switch to open alternatives like GIMP, Krita, or Affinity suite—$70 one-time, no subscriptions. Or self-host with DaVinci Resolve free tier.
This exposes Big Software’s arms race: users vs. enforcers. Adobe wins short-term, but trust erodes long-term. In 2024, with AI tools like Midjourney disrupting Photoshop’s moat, expect harsher measures. Watch your system files—they’re the new battleground.