Turning a standard Linux machine into a router flips its role from endpoint to gateway. Your box now bridges networks, forwarding traffic between interfaces like WAN and LAN. This demands kernel tweaks, firewall rules, and careful hardware choices. Miss these, and your network grinds to a halt or opens wide to attacks. Done right, you gain full control over routing, QoS, and VPNs—far beyond consumer routers.
The core shift starts in the kernel. By default, Linux drops packets not destined for itself. Flip net.ipv4.ip_forward=1 in /etc/sysctl.conf and apply with sysctl -p. This enables packet forwarding. For IPv6, set net.ipv6.conf.all.forwarding=1. Without it, no inter-network traffic flows. Real-world impact: a home setup with 1Gbps fiber needs this for LAN access to the internet.
Networking Stack Overhaul
Multiple network interfaces become essential. Assign one as WAN (e.g., eth0 to ISP modem) and others as LAN (e.g., eth1 to switch). Use ip link to manage them. Static IPs or DHCP on WAN, then NAT for LAN clients via nftables or legacy iptables.
Basic NAT setup with nftables:
nft add table nat
nft add chain nat postrouting { type nat hook postrouting priority 100 \; }
nft add rule nat postrouting oifname "eth0" masquerade
This masquerades LAN traffic out the WAN interface. Routing tables via ip route handle defaults: ip route add default via <ISP_GW> dev eth0. DHCP server like dnsmasq or isc-dhcp-server assigns LAN IPs. Implications? You control DNS, blocking ads at the router level—saves bandwidth and boosts privacy.
Common pitfalls include MTU mismatches. ISP MTU at 1500? Path MTU discovery fails under VPNs, fragmenting packets. Clamp MSS with iptables -t mangle -A FORWARD -p tcp --tcp-flags SYN,RST SYN -j TCPMSS --clamp-mss-to-pmtu. Conntrack table overflows at high loads; tune net.netfilter.nf_conntrack_max=262144 on a 4-core box handling 500+ devices.
Security Locks Down Everything
Now internet-facing, your Linux router demands a fortress. Default firewalls like ufw or firewalld work for basics, but pros use nftables zones. Block inbound except SSH (port 22) from LAN only, expose no services. Fail2ban scans logs to ban brute-forcers.
Real risks: Exposed services lead to breaches. In 2023, router hacks spiked 30% per Shadowserver scans, often unpatched firmware. Linux mitigates with timely kernels—Arch or Debian rolling beats vendor stagnation. Enable rpfilter for anti-spoofing: net.ipv4.conf.all.rp_filter=1. Why it matters: Your router guards all home traffic; one vuln compromises IoT, cameras, everything.
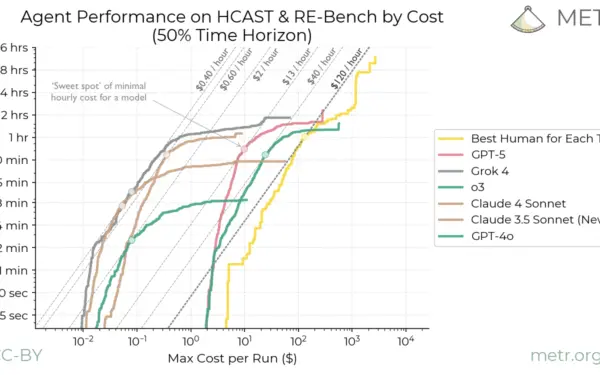
Performance Realities
CPU horsepower dictates throughput. A 2015 i5 routes 1Gbps NAT easily; modern Ryzen 5 hits 10Gbps with multi-queue NICs (RSS, XPS). Benchmarks from Netperf show kernel bypass like DPDK pushes 40Gbps, but stock kernel caps at wire speed on decent hardware. Power draw? Idle router sips 10-20W vs. consumer 5W, but adds features like WireGuard VPN at 500Mbps+.
Compare to Ubiquiti EdgeRouter: similar Linux base, but locked. DIY saves $200-500, scales with RAM/SSD for logging. Drawback: single point of failure. RAID1 boot drive and UPS mitigate, but no redundancy without clustering (e.g., VRRP).
QoS via tc (traffic control) prioritizes VoIP over torrents. cake scheduler handles bufferbloat better than fq_codel alone, keeping latency under 10ms at 95% utilization per Waveform buffersnooze tests.
Why build one? Consumer routers throttle at 500Mbps, lack IPv6, push telemetry. Linux router integrates Pi-hole, Tailscale, even Tor exit. Skeptical take: novices botch firewalls, exposing networks. Stats from Shodan show 1M+ open ports on Linux hosts. Test thoroughly with nmap and iperf.
Bottom line: Transforming Linux into a router unlocks granular control but trades simplicity for maintenance. For tinkerers with 100Mbps+ needs, it pays off in privacy and features. Casual users? Stick to pfSense appliances. Measure your setup’s throughput pre/post—expect 90% efficiency if tuned right.