Proofpoint researchers let a cargo theft threat actor roam free in a decoy network for over 30 days starting late February 2026. This honeypot exercise exposed the group’s post-exploitation playbook: redundant remote access tools, a novel code-signing evasion trick, and deliberate reconnaissance on financial systems. The actor targets U.S. trucking and logistics firms via compromised load boards—online platforms like DAT or Truckstop.com that match shippers with carriers. These attacks fuel physical cargo theft, which cost the industry over $500 million annually according to FBI data from recent years.
Why does this matter? Most breach reports stop at initial access. Here, researchers watched the full dwell time, revealing how thieves maintain stealthy control to steal high-value loads like electronics or pharmaceuticals. Logistics companies often overlook endpoint persistence, leaving them vulnerable to weeks-long intrusions.
Initial Infection Chain
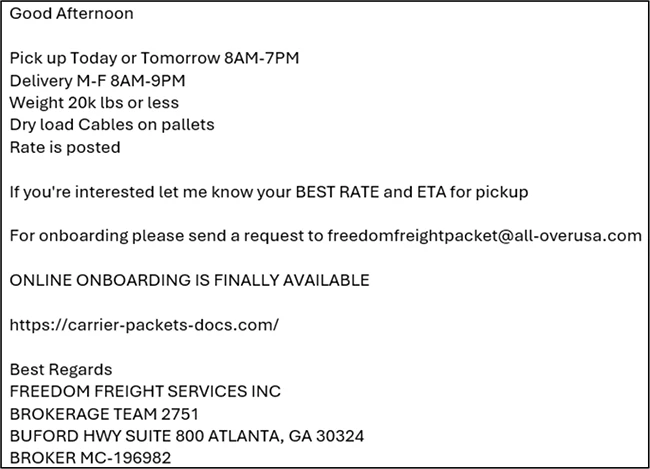
On February 27, 2026, the actor compromised a load board and posted fake high-paying loads. Interested carriers received emails with a malicious Visual Basic Script (VBS) attachment. Executing it triggered a PowerShell downloader, which fetched and ran another script. This installed ScreenConnect—a legitimate remote access tool abused as a RAT—and displayed a fake broker-carrier agreement PDF to distract the user.
The chain relied on social engineering: carriers chase lucrative gigs amid tight margins. Proofpoint detonated the payload safely in their decoy, confirming the actor’s focus on transportation. Previous incidents linked this group to similar load board phishing, but this marked the first deep dive into their lateral movement.
Layered Persistence and Evasion Tactics
Once inside, the actor stacked tools for redundancy. Over 30 days, they deployed four ScreenConnect instances, plus Pulseway and SimpleHelp RMM agents. Multiple overlapping remote management tools ensure access survives if one gets blocked—SmartPlay at work, not sophistication.
The standout move came late March: using an active ScreenConnect session, the actor ran a PowerShell script to upload the ScreenConnect installer to an unknown external signing service. This service slapped on a valid but fake code-signing certificate, hosted the binary on attacker-controlled AWS S3, and returned it. Post-install, scripts swapped out originals signed with now-revoked ConnectWise certs.
This “certificate laundering” dodged Windows trust warnings and endpoint detection. Revoked certs trigger alerts; fresh ones don’t. Researchers noted no prior sightings of this signing service, suggesting an evolution in commodity malware ops. Skeptical take: it’s clever reuse of legit infrastructure, not zero-day wizardry. Attackers exploit vendor revocations—like ConnectWise’s 2024 mess—affecting thousands.
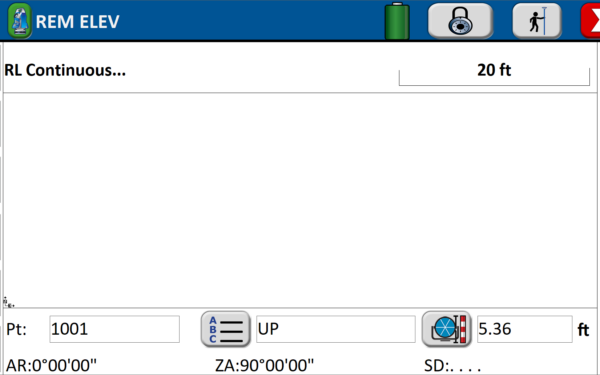
Installation timeline:
Feb 27: Initial ScreenConnect (3 instances)
Mar ~10: Pulseway RMM, SimpleHelp RMM
Late Mar: Fourth ScreenConnect via signing service
Reconnaissance and Intent
Three days post-access, an operator manually navigated the victim’s browser to PayPal—likely hunting payment credentials. By day eight, they escalated: enumerated local users, dumped browser data with tools like LaZagne, and scanned for remote desktop configs.
Later, they probed network shares, Active Directory if present, and financial apps. No ransomware or data exfil observed; focus stayed on trucking ops—load schedules, carrier logs, dispatch systems. Goal: spot valuable cargo routes for physical heists.
Cargo theft rings like this coordinate digital recon with street crews. A single compromised endpoint yields real-time load intel, enabling “virtual hijackings” where thieves pose as legit drivers or ambush trucks.
Implications for Logistics Security
Logistics firms face asymmetric risks: load boards are phishing goldmines, with 10,000+ U.S. carriers active daily. Dwell time over 30 days shows detection gaps—RMM tools blend into noisy environments.
Defenses: Patch RMM agents promptly, block unsigned binaries, monitor PowerShell abuse, and segment load board traffic. Behavioral analytics flag redundant access tools. Firms should audit cert trust and rotate creds post-breach.
This isn’t nation-state opsec; it’s profit-driven crooks scaling with cloud infra. Proofpoint pulled the plug after full observation, but real victims lose millions per incident. Prioritize endpoint visibility—thieves already own the network.