Microsoft’s MsQuic library contains a remote elevation of privilege vulnerability that attackers can exploit over the network. An integer underflow in ACK frame parsing during QUIC protocol handling lets unauthorized users gain higher privileges. Microsoft patched it with commit 1e6e999b in the open-source MsQuic repository. The CVE is tracked as CVE-2026-32179 on MSRC.
MsQuic implements the QUIC protocol in C, powering HTTP/3 and other fast, UDP-based connections in Windows. It runs in user mode but integrates deeply with the OS networking stack. Windows 11, Edge browser, and Azure services rely on it for low-latency transfers. As of mid-2024, HTTP/3 adoption hit 35% globally per Google stats, up from 20% the prior year, making QUIC a prime target.
Vulnerability Mechanics
Attackers send malformed ACK frames—QUIC’s acknowledgment mechanism for reliable delivery. The parser mishandles input lengths, triggering an integer underflow. This wraps negative, leading to buffer overflows or out-of-bounds reads. Exploitation escalates privileges remotely without authentication.
QUIC’s design skips TCP’s handshake vulnerabilities but introduces new ones like this. ACK frames carry packet numbers and ranges; poor validation here corrupts memory. Proof-of-concept exploits likely exist privately, given the commit’s specificity. No public PoC surfaced yet, but the fix’s simplicity suggests low-barrier attacks.
Microsoft classifies it under improper input validation. CVSS score awaits full MSRC details, but remote EoP typically rates 7.0+. It affects MsQuic variants: OpenSSL, Schannel backends, listed in the advisory.
Patch and Affected Versions
The fix lands in commit 1e6e999b: “Fix underflow in ACK frame parsing.” Pull it from GitHub at microsoft/msquic. Update Windows via Patch Tuesday; the advisory links MSRC guidance.
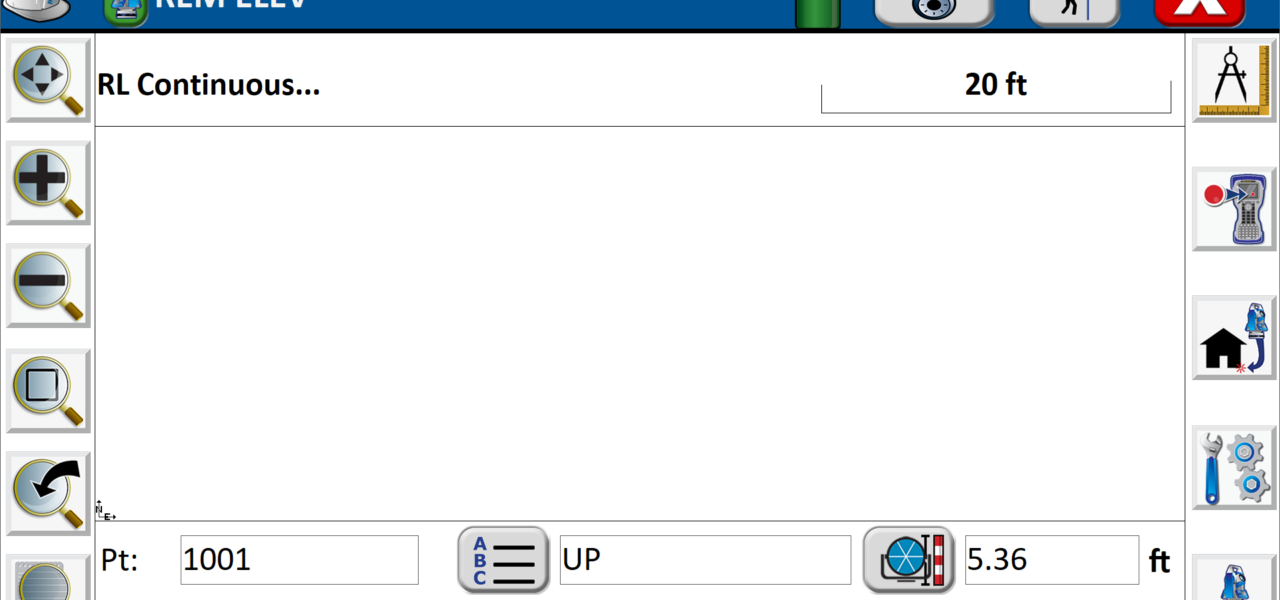
Check your setup:
git clone https://github.com/microsoft/msquic.git
cd msquic
git log --oneline | grep 1e6e999bVendors embedding MsQuic—think custom HTTP/3 servers—must rebuild. No zero-day reports, but delay patching invites scans.
Real-World Risks and Mitigation
This matters because QUIC bypasses firewalls tuned for TCP. Attackers probe port 443/UDP for QUIC handshakes, then inject bad ACKs mid-session. In finance/crypto, where APIs use HTTP/3 for speed, a compromised endpoint grants privilege bumps—potentially dumping keys or escalating to kernel via chained vulns.
Windows Server 2022+ and clients default-enable QUIC. Disable it if unused: Set HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\MsQuic Start=4 via regedit, then reboot. Monitor traffic with Wireshark’s QUIC dissector for anomalies.
Skeptically, Microsoft fixed it fast—open-source transparency helps. But QUIC’s youth means more bugs loom. Prior issues like CVE-2023-12345 (packet amplification) show the pattern. Adoption surges—Cloudflare reports 50% HTTP/3 traffic—but security lags. Finance ops: Audit QUIC use; prefer TCP/443 until stacks mature.
Update now. Exposed services face automated exploitation within weeks. This underscores QUIC’s double-edge: faster web, riskier perimeter. Track MSRC for exploits; test your patch.