A developer racked up a €54,000 bill in just 13 hours after leaving a Firebase API key unrestricted in client-side code. Attackers exploited it to hammer Google’s Gemini AI APIs with massive requests. This incident, discussed on Hacker News, exposes the high stakes of basic misconfigurations in cloud services.
The key facts stand out: the spike hit between October 10 and 11, 2024. Usage logs showed over 100 million tokens processed through Gemini 1.5 Pro and Flash models. At current pricing—€0.35 per million input tokens for Pro and €1.05 per million output tokens—this equates to relentless querying. One attacker alone burned through €20,000 in two hours by scripting parallel requests from multiple IPs.
How the Breach Unfolded
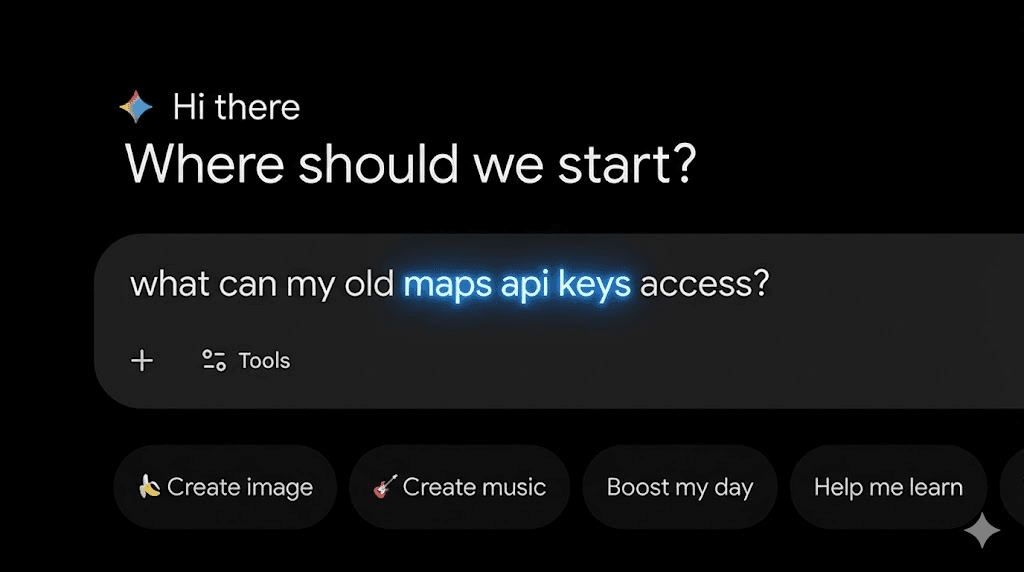
Firebase projects often embed API keys in web apps for easy client-side access to services like authentication or databases. Google recommends restricting these keys in the Cloud Console to specific referrers (e.g., your domain) and APIs. Here, the key faced zero restrictions. It appeared in a public GitHub repo or directly in browser JavaScript, making it trivial to extract.
Attackers scraped the key, then built scripts to call Gemini endpoints. Gemini’s APIs lack built-in rate limits per key in free tiers, and even paid ones cap at project level. They rotated user agents, proxies, and IPs to evade basic detection. Logs revealed prompts like “Write a story about…” repeated endlessly, maximizing token output for cost.
Firebase’s design assumes keys are public but controlled. Documentation warns: “API keys alone do not secure your app.” Without referrer checks or API scoping, anyone with the key gains full project access. This case proves the point—client-side keys need ironclad restrictions.
Costs and Real-World Damage
Break down the numbers: €54,000 over 13 hours averages €4,150 per hour. Gemini Pro input costs €0.525/million tokens (USD $0.0005/1K chars converted), but output dominates at €2.625/million. Attackers optimized for verbose responses, pushing costs sky-high. Google’s billing hit the developer’s card instantly, no grace period.
The developer contacted Google support. They waived €40,000 as goodwill but held firm on €14,000, citing terms of service. No fraud dispute succeeded—usage was legitimate API calls, just unwanted. This mirrors past incidents: a 2023 Twilio breach cost $1.5M from API abuse; OpenAI users hit $100K+ bills from key leaks.
Why this matters: AI APIs charge by usage, not subscriptions. A single leaked key turns your project into an open bar tab. Enterprises face bigger risks—imagine scaling to production workloads. In crypto, similar flaws in wallet SDKs or oracle feeds have drained millions.
Lessons and Fixes
First, restrict keys immediately. In Google Cloud Console, under APIs & Services > Credentials, set HTTP referrers (e.g., *.yourdomain.com/*) and application restrictions to Gemini APIs only. Test thoroughly—over-restriction breaks your app.
Second, monitor billing alerts. Set budgets with hard caps at €100/day initially. Use Cloud Logging to track anomalous spikes; scripts can alert on token volume jumps.
Third, shift sensitive calls server-side. Proxy Gemini requests through Cloud Functions or Run, authenticating with service accounts. Costs rise slightly from compute, but you control access.
Skeptically, Google could do more: per-key rate limits, anomaly detection beyond project quotas, or instant billing holds. But users bear responsibility—Firebase docs spell this out. This €54K wake-up call reinforces: cheap cloud tools demand rigorous security hygiene. One slip, and you’re paying for the internet’s AI binge.
Beyond one dev’s pain, it signals rising abuse vectors. As Gemini and rivals like Claude compete on price, attackers farm credits via leaks. Devs building AI apps: audit your keys now. Tools like gcloud alpha services api-keys list help inventory exposures.
$ gcloud alpha services api-keys list --project=YOUR_PROJECT_ID
In Njalla’s view, this isn’t hype—it’s arithmetic. Unrestricted access + pricey tokens = bankruptcy bait. Secure your stack, or someone else foots the bill on your dime.