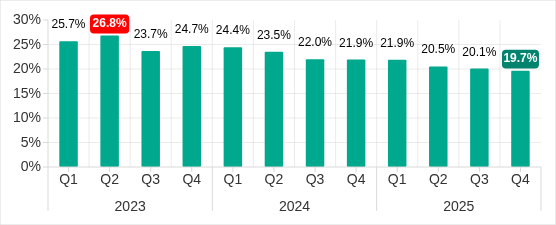
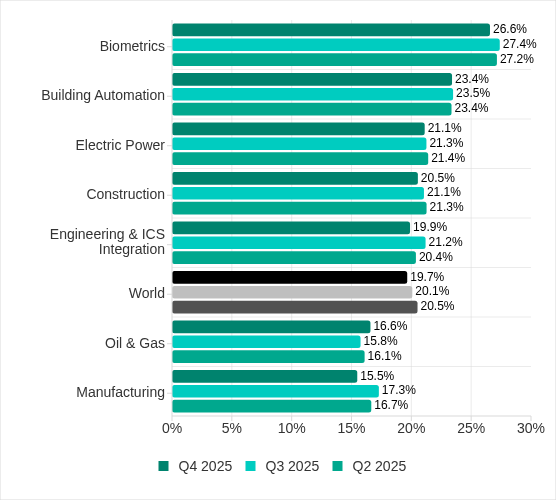
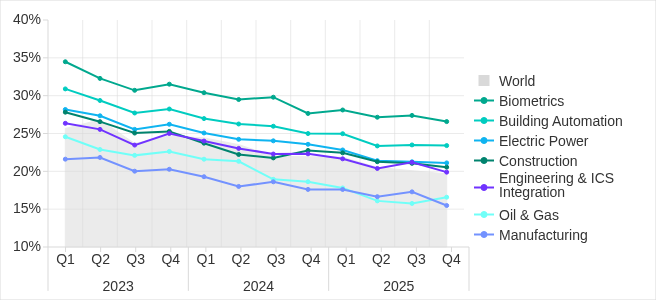
Kaspersky ICS CERT reports a continued decline in blocked malicious objects on industrial control systems (ICS) computers, hitting 19.7% in Q4 2025. This marks a 1.36-fold drop over three years and 1.25-fold since Q4 2023. Good news? Maybe—if it signals tighter defenses. But skepticism warranted: under-detection in legacy OT environments remains rife, and new vectors like email worms prove threats evolve faster than protections.
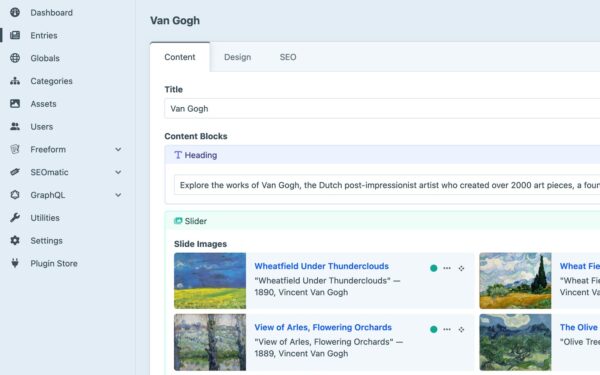
ICS underpin critical infrastructure—power grids, manufacturing, water treatment. A single breach cascades: production halts cost millions per hour (think Stuxux or NotPetya precedents), and physical safety hangs in balance. Declining detections suggest maturing endpoint security, yet 19.7% still exposes 1-in-5 ICS nodes. Attackers pivot to softer targets, exploiting human error over zero-days.
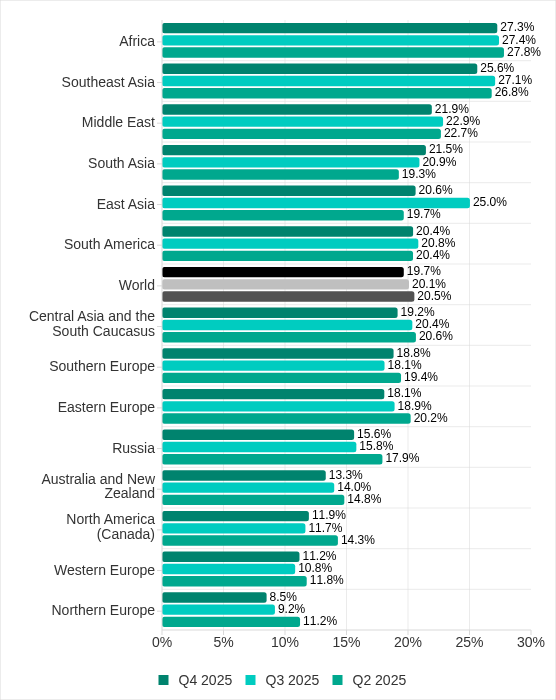
Regional Hotspots and Shifts
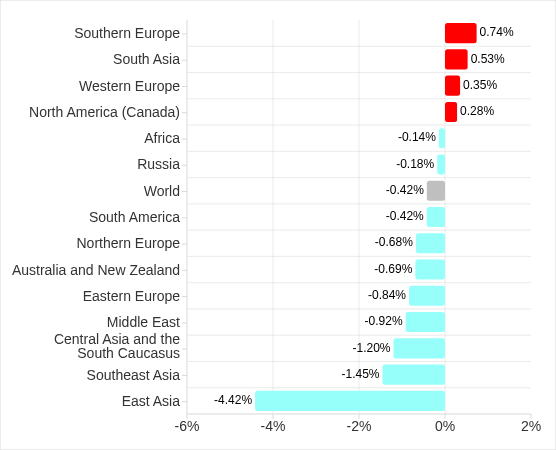
Africa leads with 27.3% blocked detections, dwarfing Northern Europe’s 8.5%. Four regions bucked the downtrend: Southern Europe and South Asia posted sharp rises. East Asia’s Q3 2025 spike—from malicious scripts—faded by Q4, hinting at contained local campaigns.
Why the variance? Africa’s high rate ties to opportunistic malware in under-resourced sectors. Europe and Asia surges flag targeted ops, possibly state-backed or ransomware precursors. Operators must geo-tailor defenses: air-gapping falters when supply chains import infections. Cross-border ops demand shared intel—Kaspersky data underscores why ICS CERTs multiply globally.
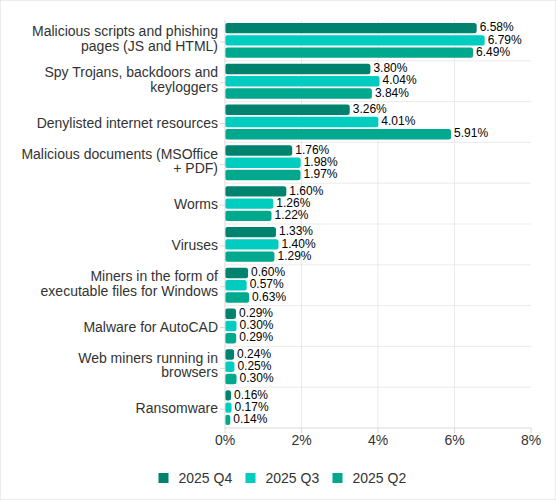
Email Worms Surge: Backdoor.MSIL.XWorm Takes Center Stage
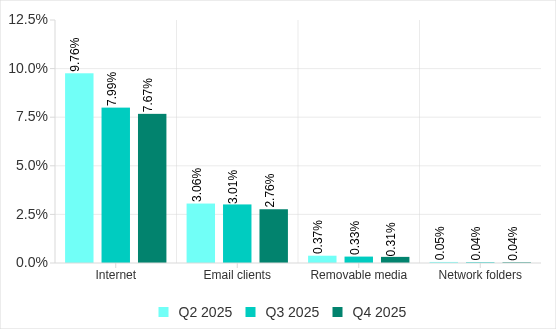
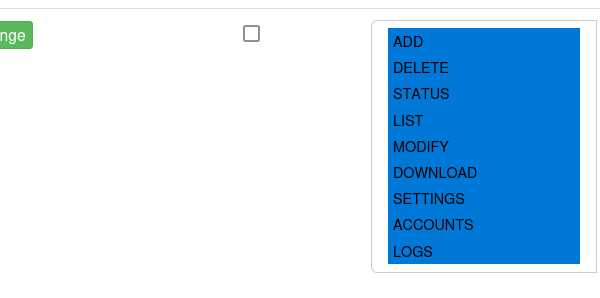
Q4’s standout: worms in email attachments spiked worldwide on ICS computers. Culprit? Backdoor.MSIL.XWorm, absent in Q3, now pervasive. This .NET trojan persists post-infection, enables remote control—prime for lateral movement in OT networks.
Hackers weaponized phishing via “Curriculum-vitae-catalina” lures, mimicking job applicant resumes. Emails hit HR, recruiters, hiring staff with subjects like “Resume” or “Attached Resume.” Payload: Curriculum Vitae-Catalina.exe, disguised as a CV. Execute it, and XWorm roots. Obfuscation techniques from 2024 phishing waves amplified spread.
Two waves: October hammered Russia, Western Europe, South America, North America (Canada). November rippled elsewhere. December lull suggests burnout or takedowns. Peaks aligned with regions’ historical email threat baselines—ICS boxes scanning attachments proves connectivity, shattering air-gap myths.
Context: ICS traditionally shun email clients, yet 2025 stats reveal convergence. Engineers check “resumes” on shared workstations? Vendor laptops bridge IT-OT gaps? XWorm’s ICS foothold warns of insider vectors—phish one HR drone, pivot to SCADA. Detection rates soared where email blocks historically high, validating behavioral AV over signatures.
Broader Implications for ICS Operators
Decline masks complacency risks. Self-propagating worms like XWorm echo WannaCry’s 2017 OT ravages—$4B+ damages. ICS CERT urges: segment networks, enforce least-privilege on email gateways, train beyond IT (OT staff click too). Prioritize EDR with OT telemetry; legacy PLCs blind standard tools.
Policy angle: Regulations lag—EU NIS2, US CISA mandates push disclosure, but enforcement spotty. Firms in high-detect regions (Africa, Latin America) face ransomware squeeze; low ones (Nordics) lure stealth ops. Global tally: thousands ICS blocks quarterly, yet unreported incidents dwarf this.
Bottom line: 19.7% signals progress, but XWorm proves phishing erodes it. Harden email perimeters, audit OT-IT junctions, and share IOCs. In 2026, expect AI-phish hybrids—adapt or pay. Kaspersky’s granular stats arm defenders; ignore at peril.