Coordinated vulnerability disclosure became an EU obligation this year under the Cyber Resilience Act (CRA) and NIS2 Directive. Vendors must now report actively exploited vulnerabilities and severe incidents within strict timelines—24 hours for significant incidents under CRA, with full details in 72 hours. This targets products with digital elements sold in the EU, holding manufacturers accountable for security from design to end-of-life. But the global system’s fragility hit home last December when MITRE’s CVE contract with CISA nearly lapsed, halting new CVE assignments for days and exposing over-reliance on a single U.S.-funded chokepoint.
That funding scare wasn’t abstract. The CVE program, run by MITRE since 1999, issues unique IDs for publicly disclosed vulnerabilities—over 200,000 active ones today. CISA pumps in $4.5 million annually, but the lapse idled the National Vulnerability Database (NVD), delaying severity scores and patches. Enterprises worldwide froze updates, as seen in vendor advisories piling up without CVEs. ENISA’s Nuno Rodrigues Carvalho calls this a wake-up: global cybersecurity assumes CVE continuity, yet it’s one contract away from blackout. Why it matters: without stable IDs, vulnerability management crumbles, leaving networks exposed to exploits like Log4Shell, which took months to fully catalog.
EU Steps Up, But Enforcement Lags
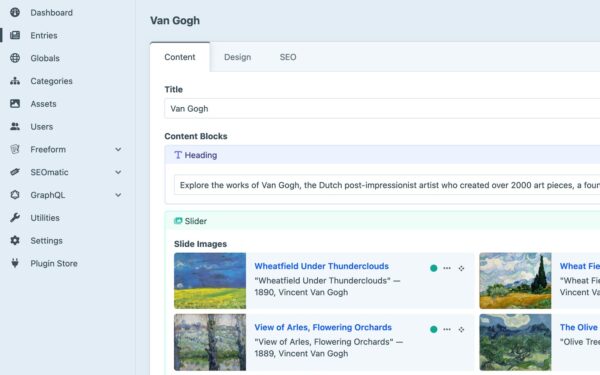
The EU isn’t waiting for U.S. fixes. CRA mandates vulnerability handling throughout product lifecycles, fining non-compliant vendors up to €15 million or 2.5% of global turnover—harmonized penalties across 27 states. NIS2 expands this to critical sectors, requiring incident reporting in 24 hours and vulnerability disclosures. ENISA coordinates via its Vulnerability Services, scaling to process EU-specific data while syncing with CVE. They’ve launched EUVDB, a database ingesting 100,000+ vulns yearly, feeding CSIRTs in member states.
Vendors have gamed systems for years: downplaying CVSS scores (e.g., rating critical flaws as medium) or delaying disclosures by 90+ days, per MITRE stats. EU levers? CRA empowers national authorities to audit and sanction. Early signs: Germany’s BSI already probes IoT makers under precursor rules. Skeptical take: regs are teeth on paper, but cultural inertia persists. Vendors prioritize sales over patches—Apple sat on zero-days for months in 2023. Enforcement needs teeth; without aggressive fines, it’s theater.
Distributed Model or Bust
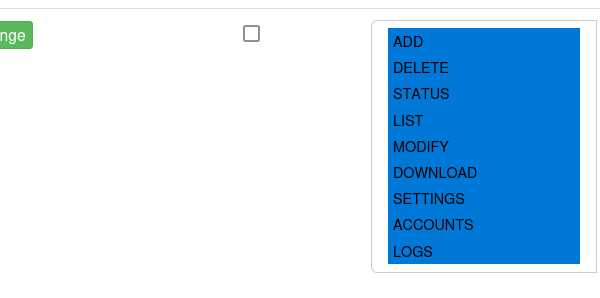
Carvalho pushes a distributed CVE model—no single failure point. ENISA’s play: interoperable services that enrich global data with EU context, like sector-specific risks. They’re building tools for CSIRTs to harmonize feeds from NVD, EUVDB, and others, tackling “conflicting enrichment” where scores vary wildly (e.g., one source rates a flaw 9.8/10, another 5.0).
Implications run deep. Stable disclosure cuts exploit windows—studies show 60% of breaches stem from unpatched vulns known for 12+ months (Verizon DBIR 2024). EU self-reliance reduces U.S. dependency amid geopolitical tensions; think export controls on cyber tools. For firms: comply or face market bans. Crypto users take note—wallets, exchanges count as “digital elements.” Globally, this pressures MITRE/CISA toward sustainability; alternatives like GitHub Advisories (10,000+ vulns) gain traction.
Cultural shift? Slow. Practitioners juggle 50+ feeds daily; automation lags. ENISA trains 1,000+ experts yearly via ECCVMT, but vendors resist till hit by regs. Bottom line: EU mandates fix symptoms, but distributed infrastructure is the cure. Watch 2025—first CRA audits will test if accountability sticks or fizzles.