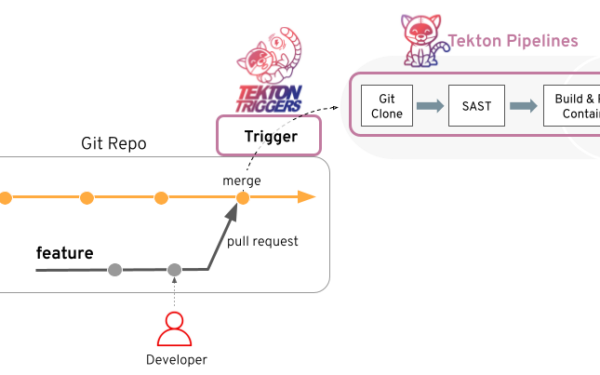
Tekton Pipelines, a popular Kubernetes-native CI/CD framework, ships with a path traversal vulnerability in its VolumeMount validation. Attackers with Task or TaskRun creation permissions can bypass restrictions on internal /tekton/ paths using .. components. A path like /tekton/home/../results slips through checks but resolves to the forbidden /tekton/results at runtime. This affects all versions up to v1.11.0. Patch your clusters now with v1.11.1.
Tekton enforces these restrictions to protect its internal state—think task results, step scripts, and entrypoint coordination—from user interference. Without them, pipelines could fail unpredictably or leak data. The flaw lives in pkg/apis/pipeline/v1/container_validation.go and the v1beta1 equivalent. The code checks:
if strings.HasPrefix(vm.MountPath, "/tekton/") && !strings.HasPrefix(vm.MountPath, "/tekton/home") {
// reject
}This naive prefix match ignores path normalization. Go’s filepath.Clean would collapse /tekton/home/../results to /tekton/results, triggering rejection. But Tekton skips it, so the container runtime (like containerd or CRI-O) resolves the traversal post-validation. Classic mistake, but one that bites hard in shared environments.
Why This Matters
Tekton powers automated pipelines across thousands of Kubernetes clusters, from GitLab to enterprise GitOps setups. It’s CNCF-graduated, trusted for critical workflows like building container images or deploying apps. An authenticated user—say, a compromised service account or rogue developer—gains outsized control:
- Fake results: Overmount
/tekton/resultsto inject bogus outputs. Downstream Tasks trust these, propagating lies through your pipeline graph. - Tamper with scripts: Overlay step scripts under
/tekton/binor similar, injecting malicious code that runs as the pipeline’s service account. - Disrupt coordination: Mess with entrypoint state in
/tekton, halting or hijacking multi-step Tasks.
In multi-tenant clusters, this escalates from prank to sabotage. Imagine a developer account mounting a volume over results in a prod pipeline—sudden failed deploys, tainted artifacts pushed to registries. No RCE needed; just RBAC perms on Task/TaskRun. CVSS? Not scored yet, but expect high (7+): authenticated, low complexity, pipeline integrity impact.
Real-world context: Tekton sees heavy use in ArgoCD, Flux, and custom CI. A 2023 CNCF survey pegged it in 40%+ of surveyed K8s users for pipelines. Unpatched? You’re betting cluster isolation on flawed validation.
Mitigation and Reality Check
Upgrade to v1.11.1. It adds filepath.Clean before checks—simple, effective fix reported by @kodareef5.
Workarounds if patching lags:
# Kyverno policy example: Block '..' in mounts
apiVersion: kyverno.io/v1
kind: ClusterPolicy
spec:
rules:
- name: block-dotdot-mounts
match:
any:
- resources:
kinds:
- Task
- TaskRun
validate:
message: "VolumeMount paths cannot contain '..'"
pattern:
spec:
=steps:
- =volumeMounts:
X(mountPath=*..*)
x-kubernetes-preserve-unknown-fields: true
Or OPA/Gatekeeper equivalents. Tighten RBAC: Deny Task/TaskRun creates to untrusted namespaces. Audit your service accounts—many Tekton installs use cluster-wide perms.
Skeptical take: This isn’t zero-day wizardry; it’s a 20-year-old path traversal goof in a high-trust component. Tekton maintainers acted fast, but why no fuzzing or propper path handling from day one? Still, credit where due—disclosure was clean, patch out in days. Scan your manifests; if you’re on <= v1.11.0, you’re exposed. In K8s land, pipelines are the new attack surface—treat them like endpoints.
Bottom line: Patch today. Then audit every VolumeMount in your Tasks. Tekton stays solid post-fix, but this reminds us: Even battle-tested tools leak if you skip basics.