Researchers from The Ohio State University cracked Apple Intelligence’s token system, proving attackers can steal authentication credentials and reuse them on different devices. This Serpent attack undermines Apple’s privacy claims for its AI features on macOS 26.0 Tahoe, allowing impersonation of victims for cloud AI requests.
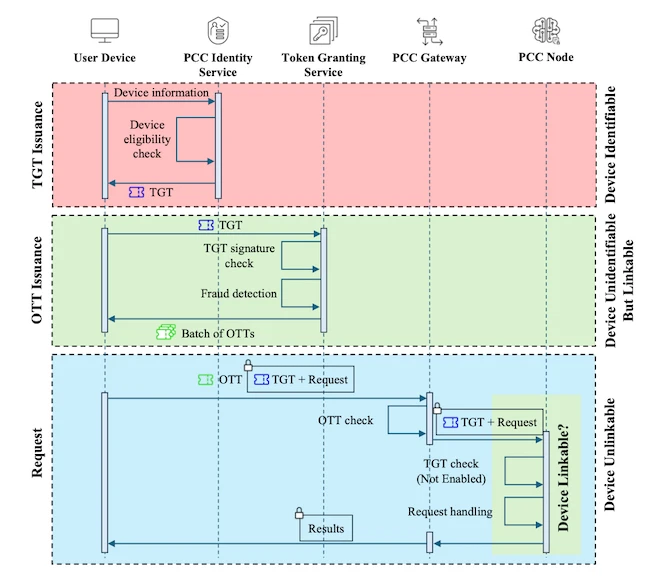
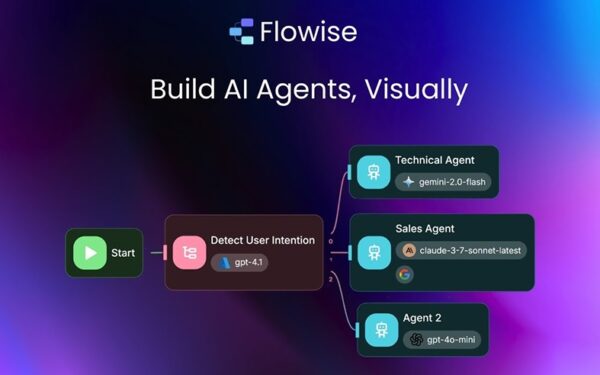
Apple Intelligence offloads heavy AI tasks to Private Cloud Compute (PCC) servers. Devices first hit an identity service to get a Token Granting Token (TGT), valid for days. The TGT fetches batches of One-Time Tokens (OTTs) for specific requests. Traffic routes through Oblivious HTTP (OHTTP) relays to mask IP addresses and metadata from Apple. PCC nodes could validate TGTs but don’t—code exists behind a disabled flag, per Apple’s docs for future abuse controls.
Plaintext Tokens, No Device Binding
TGTs and OTTs store in plaintext inside the macOS login keychain. Any app with user permissions accesses them via SecItemCopyMatching API or the security command-line tool. No encryption protects them at rest.
These are bearer tokens: whoever holds one uses it, no proof of device origin required. Apple detached tokens from hardware for anonymity, but skipped binding or revocation mechanisms. Stolen tokens work until natural expiry—days for TGTs—leaving users exposed post-theft.
This setup echoes OAuth bearer tokens, widely used but risky without extras like short expiry, rotation, or hardware attestation. Apple prioritizes privacy over tight auth, betting on device security. The researchers show that bet fails if malware slips in.
The Serpent Attack in Action
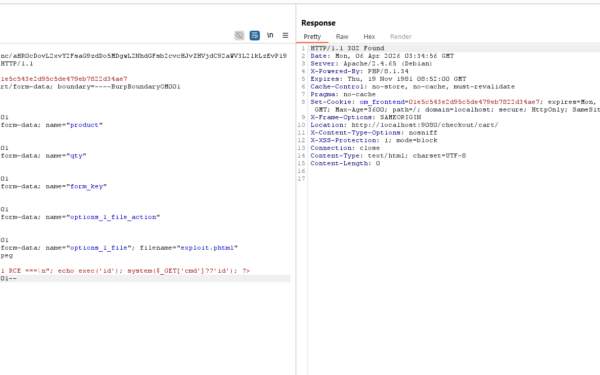
Serpent exploits two phases: extraction and disguise. Malware on the victim’s Mac queries the keychain, triggering a standard “Allow” prompt for app access. Users often approve these—macOS shows them routinely for legit apps like browsers or password managers.
Once approved, malware dumps TGTs and OTTs, exfiltrates to the attacker’s server. Attacker then injects the tokens into their own keychain, overwriting locals. Their device now authenticates as the victim, sending AI requests to PCC servers that accept them blindly.
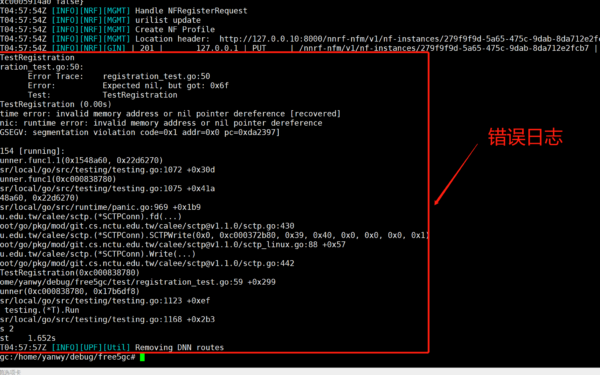
Tests on macOS 26.0 Tahoe confirmed success. The attack sidesteps device checks, OHTTP obscurity, and PCC isolation. No root needed; standard user perms suffice post-prompt.
Why This Breaks Apple’s Model
Apple markets Apple Intelligence as privacy-first: on-device processing where possible, secure cloud for the rest via PCC with verifiable transparency—users can inspect node software. But reusable stolen tokens let attackers rack up victim’s AI quota, probe personal data inferences, or chain to other services if tokens link broader.
Costs matter: AI inference isn’t free. Attackers could burn through user limits or incur charges if billed. Worse, repeated requests reveal usage patterns despite OHTTP—relays hide from Apple but not volume spikes.
Revocation gaps amplify risk. No kill switch exists; users wait out expiry or nuke keychains, disrupting legit access. Compare to Passkeys or Apple’s iCloud Private Relay: those tie to hardware or have revocation. Here, anonymity trumps security.
Fair to Apple: macOS keychain prompts aim to block silent theft, and PCC nodes run custom Apple silicon for trust. But researchers flag the off-by-default TGT check as a missed chance. Enable it, bind tokens loosely to Secure Enclave attestations, add revocation endpoints—problems shrink.
This isn’t theoretical. Serpent demands user error on prompts, common in phishing or trojaned apps. With Apple Intelligence expanding to iOS, watchOS by 2026, attack surface grows. Users: audit keychain apps, deny odd prompts, monitor AI usage. Apple should patch fast—disable plaintext storage, enforce validation, add expiry tweaks.
Bottom line: Apple’s privacy theater cracks under token reuse. It protects against mass surveillance but not targeted theft. Fix the bearer model, or AI hype sours on real breaches.