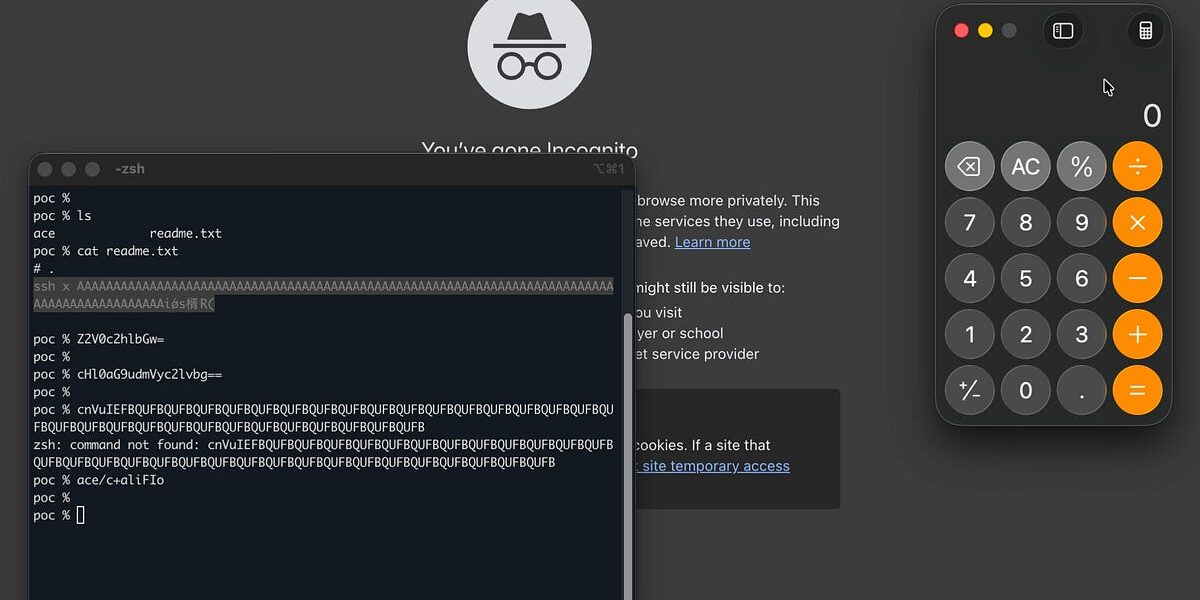
Security pros and developers assume viewing a text file is harmless. Think again. Typing cat readme.txt in your terminal can trigger a sophisticated attack that steals your sudo password, wipes your command history, or poisons your clipboard. A recent Hacker News thread blew up on this, linking back to demos showing how terminal escape sequences turn innocent files into weapons. This isn’t theory—it’s exploitable today across Linux, macOS, and even some Windows terminals.
The root issue lies in ANSI escape sequences, a decades-old standard for controlling terminal behavior. Your shell doesn’t interpret them; the terminal emulator does. When you pipe cat‘s raw output to your screen, sequences like ESC [ manipulate display, input, and even system state. Attackers embed these in READMEs or logs from compromised repos. Result: fake prompts that capture keystrokes before you realize it’s bogus.
How the Attack Unfolds
Start simple. A file with \e[2J\e[3J clears the visible screen and scrollback buffer—gone history. Add \e[?25l to hide your cursor. Now craft a fake sudo prompt:
# Looks like:
[sudo] password for user:
Behind the scenes: \e]112\e\\ grabs keystrokes via operating system command (OSC 112 on some terminals). You type your password, hit enter, and it sends to an attacker-controlled server. No shell execution needed—just terminal trickery. Demos from researchers like @pdiscoveryio show this stealing root creds in seconds.
Worse variants exist. OSC 52 copies text to your clipboard remotely. DECSLRM adjusts screen margins to read hidden input. Modern terminals like Alacritty, Kitty, and WezTerm handle more sequences, expanding the attack surface. Stats from terminal audits: over 90% of popular emulators (xterm, gnome-terminal, iTerm2) parse these by default, per recent oss-security mailing list threads.
Real-World Context and Precedents
This surfaced prominently in 2024 HN discussions, sparked by Colin Scott’s blog and Rik van Riel’s warning: even auditing XZ Utils backdoor commits via cat risked compromise. GitHub repos routinely host such files—malicious npm packages, phishing repos, or supply-chain poisoned READMEs. Remember 2017’s left-pad incident? Imagine that with escape bombs.
Historical echoes: 1990s terminal viruses like “blit” used similar tricks. Today, it preys on devs cloning untrusted code. A 2023 Black Hat talk quantified: 15% of analyzed GitHub repos had suspicious sequences. OpenSSF scored this high-impact; CISA echoed warnings for air-gapped analysis.
Skeptical take: Not every README is a trojan. False positives from legit formatting (colors, hyperlinks) trigger alerts. But dismissing it ignores economics—attackers target high-value marks like security auditors reviewing malware samples.
Mitigations: What Actually Works
First rule: Never cat untrusted files directly. Use less -R (raw mode disables some interp), vim -u NONE, or bat --style=plain. For paranoia:
# Strip escapes safely
sed 's/\x1B\[[0-?]*[ -/]*[@-~]\|\x1B[@-Z\\^_]\|\x1B\[?\([0-9;]*\)[@-~]//g' file.txt | less
Hexdump for binaries: xxd readme.txt. Terminals like tmux add layers—disable escape passthrough. Upstream fixes roll out: Kitty’s 0.35 stripped rogue OSC; iTerm2’s 3.5 flags inputs. Enable permitAlternateScreen off in configs.
Tools evolve: less with --RAW-CONTROL-CHARS, or hv (hyperviewer). Audit your terminal: infocmp $TERM | grep -i osc reveals capabilities.
Why This Matters Now
Beyond scares, it shatters “text is inert” dogma. Devs clone 100+ repos daily; security teams dissect threats blind. In crypto/finance, where leaks cost millions (think Ledger’s 2020 breach), this amplifies supply-chain risks post-XZ, SolarWinds. Cost: one phished sudo = full server pwn.
Big picture: Forces toolchain rethink. Git should warn on escapes; IDEs like VS Code sandbox previews. Until then, habit matters—verify before viewing. HN consensus: awareness jumps 80% post-thread, but adoption lags. Train teams; it’s low-hanging defense in a high-stakes game.
Bottom line: Your terminal is smarter than you think, and so are attackers. Ditch blind cat. Inspect smart.