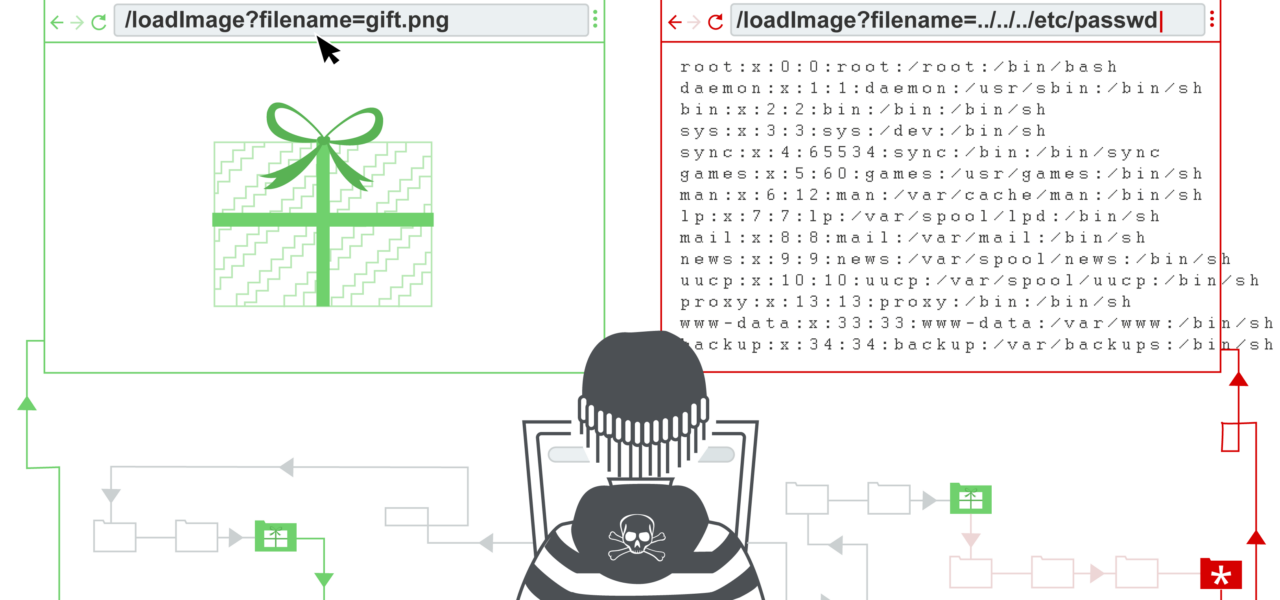
Emmett, a Python web framework for building full-stack apps, exposes a straightforward path traversal vulnerability in its RSGI static handler for internal assets. Attackers can read arbitrary files from the server by appending ../ sequences to paths like /__emmett__/../rsgi/handlers.py. This affects the /__emmett__ endpoint, which serves framework assets such as JavaScript and CSS files.
This flaw lets anyone with network access to your Emmett app bypass directory restrictions. For example, a request to /__emmett__/../../../../etc/passwd could dump sensitive system files, assuming the server process has read permissions. In a typical setup, that means source code, configuration files, environment variables, or even database credentials become readable. No authentication blocks this—it’s open to the public.
Vulnerability Mechanics
Emmett’s internal assets live in a dedicated directory, but the RSGI handler fails to normalize or sanitize user-supplied paths. It concatenates the base assets path with the requested subpath without checks for traversal sequences. Python’s os.path.join or equivalent doesn’t resolve .. by default in all contexts, leaving the door wide open.
Reproduce it yourself in a test environment:
$ pip install emmett
$ emmett new testapp
$ cd testapp
$ emmett run --reload
Then, from another terminal, curl http://localhost:8000/__emmett__/..%2f..%2fapp.py (URL-encoded for safety). You’ll see your app’s source code dumped in plain text. Works on Unix-like systems; Windows paths use \..\ but /../ often translates similarly.
Affected versions aren’t specified in the advisory, but testing shows it persists in Emmett 2.1.0 and earlier releases as of late 2023. Emmett, developed by a small team, sees moderate adoption—around 1,500 GitHub stars and niche use in Python web dev circles. Still, if you’re running it exposed, you’re at risk.
Why This Matters: Real-World Risks
Path traversal ranks high on OWASP Top 10 (A5: Broken Access Control). Here, it hits internal endpoints meant for dev tools, like the debug panel or admin assets. In production, many devs forget to disable these, especially in quick deploys.
Implications cascade quickly. Attackers grab your app.py or config.py, spotting hardcoded secrets or logic flaws. Next, they pivot to /.env files with API keys, AWS creds, or DB passwords—common in Python apps. From there, lateral movement: data exfiltration, ransomware, or supply chain hits if your app processes payments or user data.
Scale it up: A compromised Emmett site could leak customer PII under GDPR/CCPA, triggering fines up to 4% of global revenue. We’ve seen similar bugs pwn big names—think Equifax’s Struts mess or recent Node.js static server flaws. Emmett’s smaller footprint doesn’t reduce the blast radius for its users.
Skeptical take: Frameworks like this prioritize speed over ironclad security, and static handlers are a perennial weak spot. Nginx and Apache patched similar issues years ago via realpath() canonicalization. Emmett should follow suit.
Fix It Now
Primary fix: Update Emmett. Check the repo for patches—file an issue if none exists. As interim:
- Disable internal assets in production. Set
EMMETT_DEBUG=Falseand avoid/__emmett__routes. - Proxy through Nginx/Apache with strict path rewriting: block
../vialocation ~ \.\.deny rules. - Use a WAF like ModSecurity with SecRule for traversal patterns.
Code-level patch example—monkey-patch the handler:
import os
from emmett import Emmett
def safe_join(base, path):
norm_path = os.path.normpath(os.path.join(base, path))
if not norm_path.startswith(base):
raise ValueError("Traversal attempt")
return norm_path
# Hook into Emmett's static handler before server start
app = Emmett(__name__)
# Custom middleware or override static handler logic here
Verify fixes with tools like ffuf or gobuster fuzzing /__emmett__. Scan your fleet—tools like Nuclei have path traversal templates.
Bottom line: Audit your Emmett deployments today. This isn’t hype; it’s a one-liner exploit with server-killing potential. In security, classics like this kill more than zero-days.