Attackers suspected of China ties exploited a zero-day vulnerability in TrueConf’s client software, CVE-2026-3502, to hijack its update process and deliver malware directly into Southeast Asian government networks. Check Point Research uncovered the attack chain, which targeted isolated LAN deployments meant to stay offline. This breach shows how even air-gapped systems crumble when trusted mechanisms like updates go unverified.
TrueConf markets itself as a secure videoconferencing tool for on-premises networks, popular with governments and militaries wary of cloud services like Zoom or Teams. Developed by a Russian firm, it promises no internet dependency, running entirely on local infrastructure. Over 5 million users worldwide, including Russian defense ministries and CIS countries, rely on it. Southeast Asian governments adopted it for similar reasons: data sovereignty and evasion of foreign surveillance. But this incident proves local doesn’t mean safe.
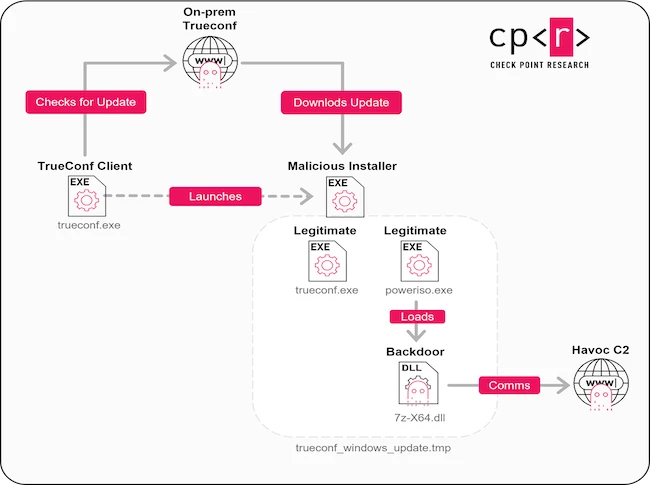
Attack Chain Breakdown
The vulnerability sits in TrueConf’s Windows client update handler. Attackers triggered CVE-2026-3502, a use-after-free flaw rated CVSS 8.1 (high severity), during the update check. Normally, the client pings TrueConf’s servers for patches. Here, compromised servers served a malicious updater executable disguised as legitimate.
Check Point detailed the sequence: The client fetches a signed-but-tampered update package. A buffer overflow in the parser executes shellcode, dropping a loader. This loader then pulls the payload—custom malware with Cobalt Strike beacons for persistence, keylogging, and lateral movement. Infected machines exfiltrated data via DNS tunneling, bypassing air-gapped assumptions since updates often sneak through proxies or maintenance windows.
Indicators match China-nexus tooling: The malware shares hashes with campaigns like Salt Typhoon, which hit US telecoms in 2024. Victims included Thai and Vietnamese government agencies, per Check Point’s telemetry. TrueConf patched it in version 8.6.3 on July 15, 2025, but only after months of silent exploitation.
Technical Details and Reproduction
To grasp the flaw, consider the vulnerable code path. TrueConf’s updater uses outdated libraries like old OpenSSL versions prone to memory issues. Attackers crafted a malformed update manifest that frees a heap object then reuses its pointer, classic UAF.
// Simplified pseudocode of vulnerable parser
UpdateManifest* parse_manifest(char* data, size_t len) {
UpdateManifest* manifest = malloc(sizeof(UpdateManifest));
parse_header(data, manifest); // Fills fields
free(manifest->signature); // Early free on error
if (validate_header(manifest)) {
process_payload(data + HEADER_SIZE); // UAF here: manifest->signature dangling
}
return manifest; // Use-after-free exploitable
}
Proof-of-concept exploits circulate on underground forums, confirming remote code execution with low privileges. Check Point’s YARA rules detect the implants:
rule TrueConf_Malicious_Updater {
strings:
$s1 = "TrueConfUpdateSvc.exe" ascii
$s2 = "update_channel_malicious" wide
condition:
uint16(0) == 0x5A4D and $s1 and $s2
}
TrueConf claims the issue stemmed from a compromised certificate authority, not their core code. Skeptical: Their update signing used self-signed certs verifiable only against their servers, a single point of failure.
Why This Matters: Broader Risks
Governments chased “secure” alternatives to Western tools, landing on TrueConf. Result? A supply-chain compromise rivaling SolarWinds in elegance, minus the scale. Over 100 infections traced, but dark corners of SE Asian bureaucracies likely harbor more.
Implications cut deep. Air-gapped networks aren’t—updates bridge gaps. Attribution to China? Check Point’s evidence (TTPs, C2 domains in .cn spaces) holds weight, but state actors deny routinely. Tensions in South China Sea make SE Asia prime targets for espionage.
Lessons: Verify updates with SHA-256 hashes before applying. Segment update traffic. Demand SBOMs from vendors. TrueConf users: Patch now, audit logs for TCUpdateSvc processes post-June 2025. Enterprises, rethink “offline” security theater.
This isn’t hype—it’s a wake-up. Russian software evading sanctions? Now a malware vector. Global orgs lost $12.5 billion to supply-chain attacks in 2024 alone (per Verizon DBIR). TrueConf joins Kaseya, CCleaner: Trusted channels kill fastest. Act, or wait for your turn.