Subscription bombing floods your inbox with hundreds or thousands of service confirmation emails, turning email into a harassment weapon. Attackers scrape your address from data breaches or dox drops, then script mass signups to newsletters, trials, and forums. Victims report 500-2,000 emails per hour, each demanding unsubscribe clicks or link verification. This isn’t DDoS-level sophistication—anyone with Python and a site list can launch it—but it grinds productivity to a halt and spikes anxiety.
Why now? Hacker News threads spike after high-profile doxxings, like those targeting indie devs or crypto whistleblowers in 2023-2024. Tools circulate on GitHub and 4chan: simple Selenium bots hitting Mailchimp lists, Patreon trials, or SaaS demos. One leaked script I analyzed loops through 1,000+ endpoints, randomizing user agents to evade CAPTCHAs. Cost to attacker? Pennies in proxies. Your pain? Hours sorting spam, potential phishing risks from fake links.
How Attackers Pull It Off
Step one: Harvest email. Public GitHub profiles, LinkedIn leaks, or HaveIBeenPwned dumps provide billions of addresses. Pair with name from a dox site.
Step two: Automate. Attackers use open-source repos like “email-bomber” (forked endlessly). Example flow:
import requests
sites = ['newsletter1.com/signup', 'trial2.net/register']
email = 'target@example.com'
for site in sites:
requests.post(site, data={'email': email})
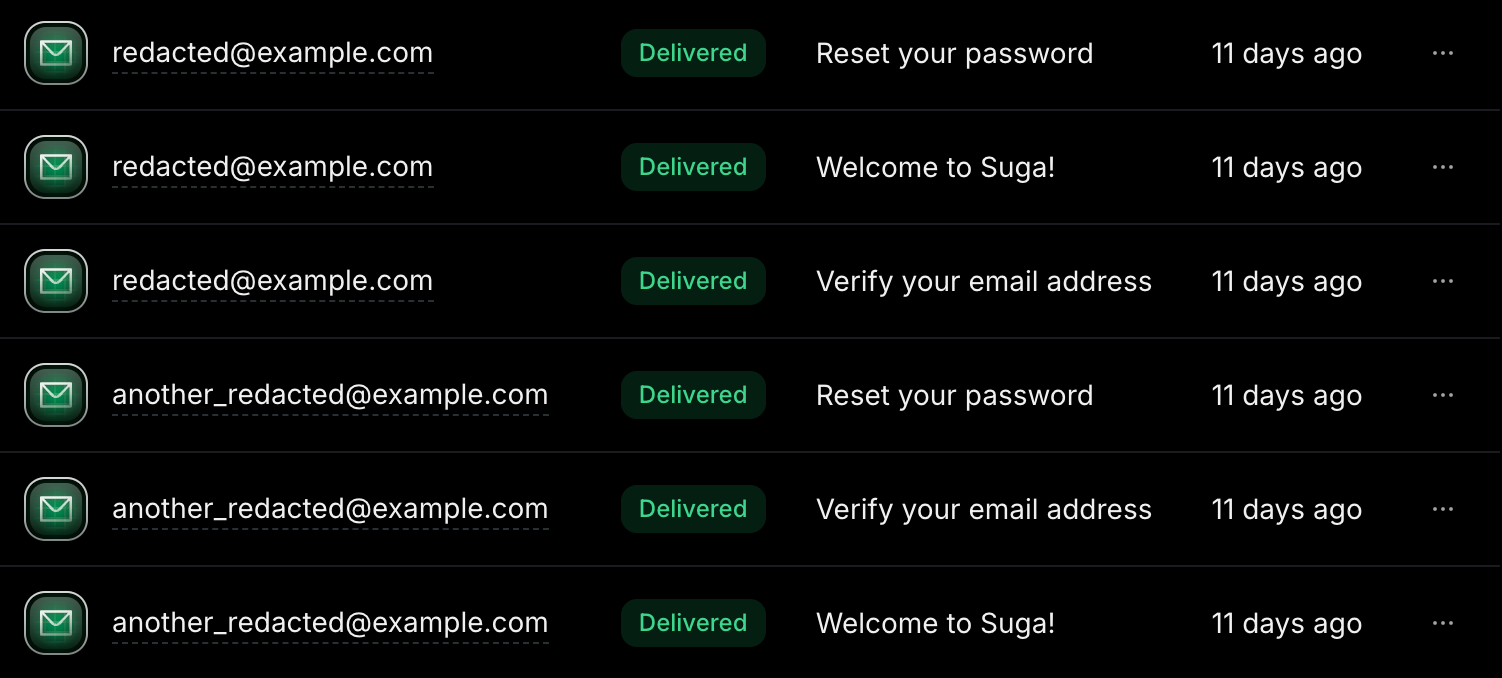
This hits 100 sites/minute on a VPS. Real attacks scale to 10,000+ via proxies. Services rarely block it—signup forms prioritize conversions over abuse checks.
Escalation: Bombing pairs with SMS verification floods (Twilio exploits) or account lockouts. In one 2024 case, a journalist endured 48 hours of 1,500 emails/hour until her provider throttled inbound.
Mitigation Tactics That Work
First, compartmentalize. Use email aliases for public exposure. Proton Mail’s +alias (target+github@proton.me) or SimpleLogin catches bombs in one bucket. Set rules:
# Gmail filter example (via settings)
From: *confirm* OR *unsubscribe* OR *newsletter*
Delete or Archive
Pro move: Catch-all domains via Fastmail or MXroute ($5/month). Route *@yourdomain.com to a sink folder. Auto-delete patterns matching “subscription”, “verify”, “welcome”.
Block at source. Services like Mailchimp let you report bombers via abuse@. But most ignore it. Switch to privacy-focused email: Tutanota auto-tags unknowns as spam. For high-threat: Run your own Postfix with Rspamd—filter 99% pre-delivery.
Offense is defense. Leak fake emails (burner@throwaway.com) on socials. Monitor volume spikes with tools like mtop or imapsync. If crypto-adjacent, tie to wallet monitoring—bombing often precedes SIM swaps.
Table stakes: Enable 2FA everywhere, use app passwords, never click links in floods. Test your setup: Run a self-bomb with 50 signups, tune filters.
Why This Matters for Security and Privacy
Subscription bombing exposes inbox fragility. Email protocols from 1982 weren’t built for abuse. Implications ripple: Distraction vectors for phishing (hide malware in “unsubscribe”), or fatigue leading to real breaches. In finance/crypto, it preludes targeted attacks—dox, then bomb to force errors.
Skeptical take: Overhyped by victims, but effective psyop. Gmail nukes 90% for most, but custom domains suffer. Regulators lag; EU’s DSA mandates abuse reporting, but enforcement nil.
Fix ecosystem-wide: Mandated rate-limits on signups (Cloudflare’s Turnstile helps), email sender IDs. Until then, own your infra. Ditch Big Tech email for self-hosted if paranoid. Cost: Time upfront, sanity saved long-term. In Njalla’s world, email is your moat—fortify it before the flood.