Russian military intelligence, specifically GRU unit APT28 (aka Forest Blizzard or Fancy Bear), hijacked DNS settings on over 18,000 outdated routers to steal Microsoft Office authentication tokens. This campaign, peaking in December 2023—not 2025 as some reports misstate—snared users across 200+ organizations and 5,000 consumer devices. No malware required; just exploited known flaws in end-of-life gear like MikroTik and TP-Link SOHO routers.
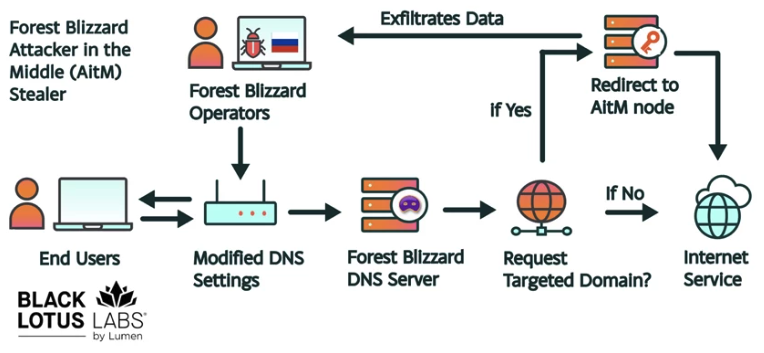
Black Lotus Labs at Lumen Technologies uncovered this after spotting anomalous DNS traffic. Attackers tweaked router DNS to route queries through their controlled VPS servers. When victims hit login.services.microsoft.com or similar OAuth endpoints for Office 365, the hackers intercepted the tokens. These tokens grant access post-multi-factor authentication (MFA), bypassing passwords and 2FA entirely.
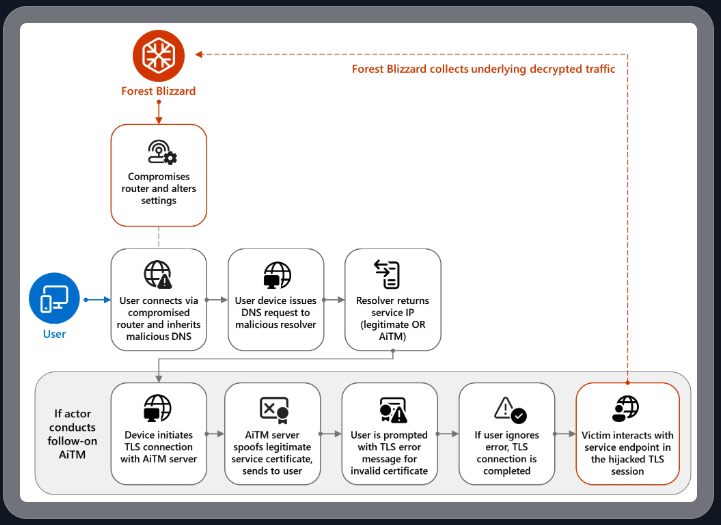
How the Hijack Works
Victims connect to Microsoft domains unaware their router redirects DNS requests. The malicious server resolves to attacker-controlled IPs hosting phishing-like pages that harvest OAuth tokens in plaintext HTTP. Microsoft detailed this in a September 2024 blog: tokens flow unencrypted during the auth flow if DNS poisoning tricks browsers.
No zero-days here—pure opportunism on unpatched CVEs. MikroTik’s RouterOS had flaws like CVE-2018-14847 (arbitrary file reads) fixed years ago, yet thousands run vulnerable versions. TP-Link similarly lags. Attackers scanned internet-exposed routers, exploited remotely, and pushed DNS changes network-wide. All downstream devices inherit the poison.
Forest Blizzard ran this from mid-2023 into 2024, per Lumen’s report. They controlled just a few VPS IPs but scaled via router propagation. UK’s NCSC echoed warnings on Russian router compromises, noting DNS as a cheap persistence vector.
Targets and Attribution
Primary hits: government ministries (foreign affairs, law enforcement), third-party email providers. Lumen pegged over 18,000 routers at peak, mostly unsupported SOHO kit in Europe and beyond. Microsoft confirmed 200 orgs, 5k endpoints compromised—tokens swiped without alerts.
Attribution sticks to GRU’s 291st/744th signals regiments. Fancy Bear’s resume includes 2016 DNC hacks, SolarWinds periphery, and Ukraine ops. This fits their pattern: low-noise, high-volume intel grabs via infrastructure compromise. Skeptical note: while evidence (TTPs, timing, targets) aligns, state attribution always carries some fog-of-war risk amid copycats.
Why This Matters—and What to Do
OAuth tokens are gold for spies. One token equals weeks of Office access: emails, docs, SharePoint. Revocation lags; attackers exfiltrate quietly. This exposes a blind spot in enterprise security: edge routers often neglected, treated as “set-it-and-forget-it” appliances.
Implications ripple wide. SOHO routers front small offices, remote workers, even agencies. A hijacked home gateway poisons your corp VPN. Scale matters—18k networks dwarf targeted phishing. Cost to GRU? Minimal VPS fees versus priceless intel on NATO-aligned govs.
Consumers and orgs: audit your router now. Check DNS settings against ISP defaults. Run nslookup login.microsoftonline.com from affected nets; rogue IPs scream compromise. Update firmware religiously—MikroTik to 7.13+, TP-Link equivalents. Segment networks; use DoH/DoT (DNS over HTTPS/TLS) to encrypt queries upstream.
Broader lesson: nation-states feast on EOL hardware. 40% of scanned routers in Shodan run ancient firmware, per ongoing intel. Enterprises, ditch SOHO for enterprise-grade (Ubiquiti EdgeRouter, pfSense). Finance/crypto firms: token theft hits Azure AD too—rotate creds, monitor for anomalous logins.
Mitigation timeline: Microsoft auto-rotated some tokens post-detection. But manual sweeps needed. Lumen urges ISP-level blocks on known C2 domains. Until router makers enforce updates (or killswitch EOL), expect copycats. Russia won’t stop; neither should defenses.