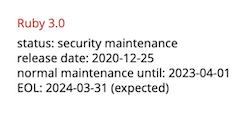
Ruby 3.2 reached end-of-life on April 1, 2025, four days after maintainers shipped version 3.2.11 with a fix for CVE-2026-27820, a buffer overflow in Zlib::GzipReader. That patch marks the final update this branch will ever see. Ruby’s security team typically addresses 6 to 12 CVEs per year across supported versions. The next flaw found in 3.2 goes unpatched, leaving any apps on it exposed indefinitely.
This matters because production Ruby apps upgrade slowly. When Ruby 3.1 hit EOL last March, data from Gemfile audits showed a notable portion of apps stuck on it. Vulnerabilities get fixed in 3.3 and 3.4, but 3.2 users inherit the risk without recourse. Attackers scan for outdated runtimes; unpatched CVEs turn into real exploits faster than you think.
Assess Your Exposure
Three factors dictate your upgrade timeline. First, exposure: Internet-facing apps like customer APIs demand immediate action over internal tools behind firewalls. Second, data sensitivity: PCI DSS 4.0, mandatory since March 2025, requires a documented plan for EOL software, signed off by executives. Skip it in card-processing scopes, and auditors flag noncompliance. Healthcare faces HIPAA updates finalizing around May 2026, dropping “addressable” wiggle room—patching becomes non-negotiable within 180-240 days.
Third, insurance: Cyber policies increasingly deny claims over EOL software, citing negligence. No public Ruby-specific cases yet, but precedents in Node.js and Python abound. If your app hits any “yes,” schedule upgrades this week. Delaying invites avoidable breaches, compliance fines starting at $100K for PCI violations, or claim rejections post-incident.
Real-world context underscores the stakes. Ruby’s ecosystem powers 1.5 million+ sites via Rails, per W3Techs. A 2024 Snyk report flagged 20% of scanned Rails apps on EOL or near-EOL runtimes. Exploits like Log4Shell showed how runtime vulns cascade; Ruby’s zlib issue could enable RCE in decompression-heavy apps.
Upgrade Targets and Paths
Target Ruby 3.4 for most teams. It hits EOL in March 2028, offers a year of battle-testing, full Rails 7.2 and 8.0 support, and balances stability with longevity. Ruby 3.3 suits risk-averse groups needing EOL breathing room until March 2027. Skip 4.0 previews unless you’re on 3.4 already—it’s too green.
Standard path: 3.2 → 3.3 → 3.4. This surfaces deprecations gradually; 3.3 warnings become errors in 3.4. With strong tests (aim for 80%+ coverage), jump straight to 3.4—3.3 changes rarely break standard Rails code.
Watch these 3.4 gotchas:
- Bundled gems vanish:
base64,csv,bigdecimal,etc,json,psych,stringio, andzlibrequire explicit Gemfile entries. Fix: Addgem 'csv'etc., or userequire 'csv'with bundler awareness. - Deprecations enforced: Keyword args in procs/lambdas, frozen error strings—test thoroughly.
- Performance tweaks: Faster hash tables, but benchmark your hotspots.
To upgrade:
$ ruby -v # Confirm 3.2.x
$ gem install bundler -v '~> 2.5'
$ bundle update ruby # Pins to 3.4.x in Gemfile
$ bundle exec rake test # Or rspec
Rails users: Update to 7.2+ first if needed; it smooths runtime shifts. Allocate 1-2 engineer-days for a mid-sized app, per Honeybadger upgrade logs. Post-upgrade, monitor with tools like Scout or New Relic—3.4 cuts GC pauses by 20% in benchmarks.
Bottom line: EOL isn’t theoretical. Ruby 3.2’s clock ticks toward regret. Upgrade to 3.4 now, document it for compliance, and sleep better. Procrastination costs more than the fix.