Phishers bypass core email defenses by hijacking GitHub and Jira’s notification systems. These attacks send spam and phishing emails directly from the platforms’ own servers, passing SPF, DKIM, and DMARC checks with flying colors. Cisco Talos researchers documented this tactic, noting that on one peak day, 2.89% of all GitHub emails involved abuse. The result? Malicious messages arrive with a trusted “seal of approval,” slipping past most security gateways.
This matters because SPF, DKIM, and DMARC form the backbone of modern email authentication. SPF verifies sender IP against domain records, DKIM adds cryptographic signatures, and DMARC enforces policies. When emails originate from GitHub’s or Atlassian’s infrastructure, they inherently comply—no spoofing required. Attackers exploit this to deliver payloads that look and act legitimate, targeting collaborators or invitees who rarely question notifications from these services.
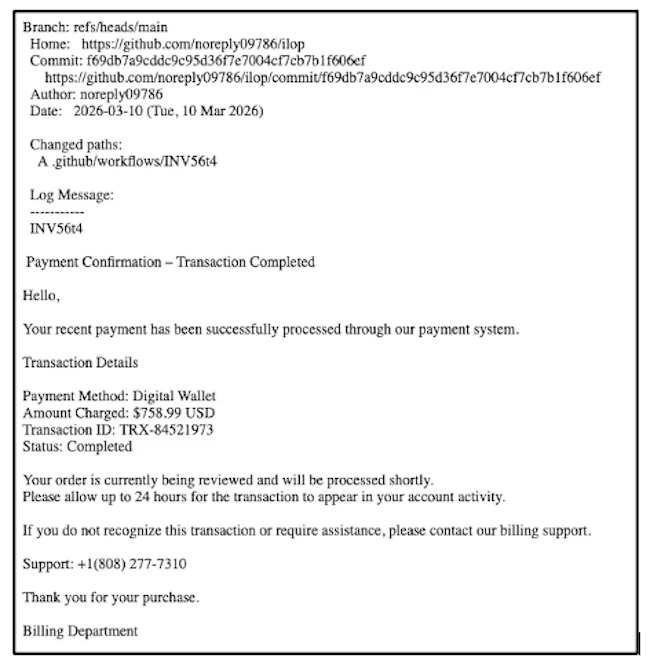
GitHub: Commit Notifications as Phishing Vectors
Attackers gain traction on GitHub by pushing commits to repositories with multiple collaborators. GitHub automatically emails everyone involved, summarizing the commit in the notification. They craft a short summary line to hook victims—something urgent like “Billing issue detected”—then embed the real scam in the longer description field: fake invoices, credential harvesters, or malware links.
The platform generates the email body, so it dodges filters. Talos observed this at scale; that 2.89% figure from a single day underscores the volume—GitHub sends millions of notifications daily, meaning thousands of potential phish. Repos often have dozens of watchers, amplifying reach. Skeptically, this isn’t new—GitHub has patched similar issues before—but enforcement lags. Why? Open collaboration invites abuse, and scanning every commit description for malice scales poorly.
Implications hit developers hard. Public or shared repos become unwitting broadcasters. Victims click through because the email screams authenticity: GitHub branding, no red flags. Broader context: GitHub hosts over 420 million repositories as of 2024, with enterprise adoption surging. One compromised collaborator invites lateral spread in teams.
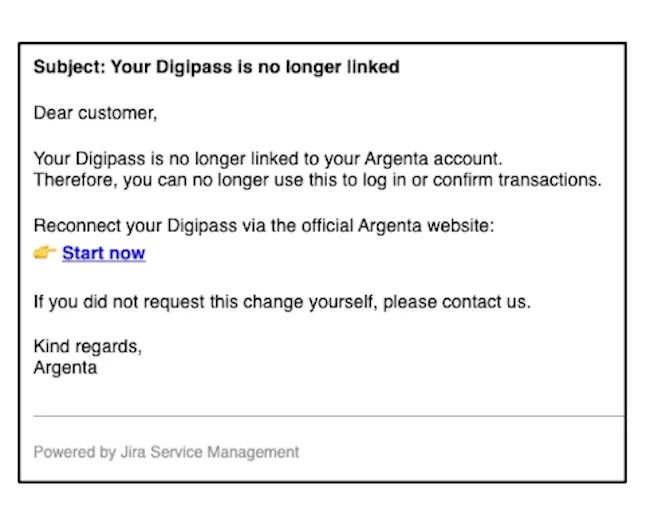
Jira: Fake Invites from Trusted Service Desks
Atlassian Jira takes a different angle. Attackers spin up a free Service Management project, slap a benign name on it like “IT Support,” and stuff phishing content into the welcome message or project description fields. They then hit “Invite Customers,” inputting victim emails. Jira’s backend weaves the attacker’s text into a polished template—Atlassian logo, footer, the works—and fires it off.
These land as expected “Service Desk” alerts in corporate inboxes. Employees see Jira invites routinely, so suspicion stays low. Talos highlights the cryptographic signing: Atlassian’s DKIM seals it tight. No external domains, no breaks in the chain. Jira’s ubiquity—used by 65% of Fortune 500 companies per Atlassian stats—makes it prime for this.
Fair point: Free tiers enable rapid setup, but paid enterprise features like this shouldn’t route unchecked user content. Atlassian has rate limits and abuse reporting, yet attackers cycle accounts. This exposes SaaS sprawl risks: every notification system is a potential phish highway.
Why This Breaks Email Security—and What to Do
Traditional defenses crumble here. Gateways flag anomalies in headers or IPs, but pristine auth neuters them. Content scanners falter too—legit platforms mean low malice scores. Talos calls it decoupling intent from infrastructure: brilliant, low-tech evasion.
Scale amplifies danger. GitHub processes billions of events yearly; Jira, millions of projects. A 3% abuse rate anywhere signals systemic holes. Enterprises face insider-like threats without insiders. Phishing evolves past spray-and-pray to precision via trusted vectors.
Mitigations start upstream. Platforms must sanitize user-generated notification content—scan summaries, descriptions, and invites for URLs, creds prompts. GitHub could limit commit message lengths or flag anomalies via ML. Jira: Verify invites against org domains, add sender previews.
Users, act now: Audit repo collaborators quarterly—remove ghosts. Whitelist Jira projects. Train teams: Hover links, check senders beyond domains. Tools like Microsoft Defender or Proofpoint offer behavioral analysis, but expect gaps. Report abuse fast—GitHub suspends 1.5 million accounts yearly for violations.
Bottom line: Relying solely on email auth is obsolete. SaaS giants own the fix, but until then, vigilance plugs the leaks. This tactic will spread to Slack, Notion, anywhere notifications flow unchecked.