Developers running OpenClaw npm package versions up to 2026.3.28 leave their LINE webhook endpoints vulnerable to denial-of-service attacks. Attackers can flood the public webhook path with junk requests, overwhelming server resources before the code verifies the required X-Line-Signature header. The maintainers rate this low severity because impacts stay bounded to temporary availability blips, but any DoS risk counts in production. Update to 2026.3.31 or later to apply the fix from commit 57c47d8c7fbf5a2e70cc4dec2380977968903cad, published March 31, 2026.
What OpenClaw Does and Why Webhooks Matter
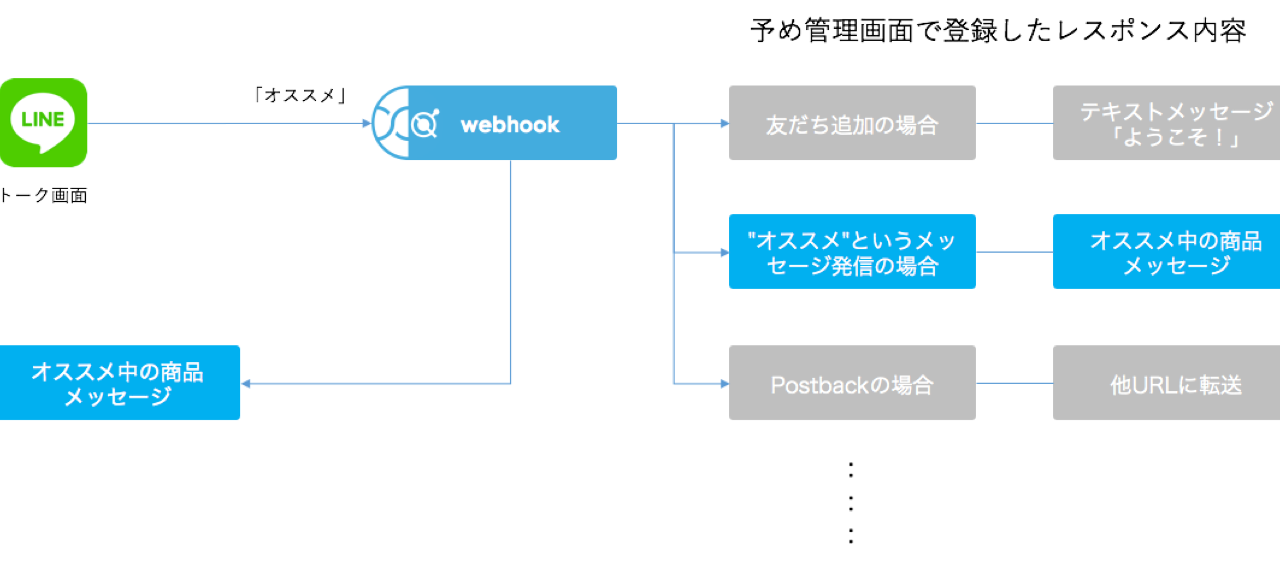
OpenClaw handles LINE Messaging API webhooks, a common setup for bots and services integrating with LINE, Japan’s dominant messaging app boasting over 200 million monthly users. LINE webhooks deliver events like messages or follows to your server via POST requests to a public URL. Each request carries an X-Line-Signature header: an HMAC-SHA256 hash of the body using your channel secret. Validating this signature confirms authenticity before processing.
The flaw sits in OpenClaw’s webhook handler up to v2026.3.28. It lacks a shared pre-authentication concurrency budget. In plain terms, the server spins up handlers for incoming requests without capping how many run simultaneously before checking that signature. A flood of forged requests—easy to generate with tools like ab or custom scripts—consumes CPU, memory, and connections. Invalid signatures eventually drop them, but not before transient overload hits legitimate traffic.
Maintainers triage it as “low” because effects limit to short-lived downtime. No data exfiltration, no code exec—just availability loss. They shipped the fix promptly after @nexrin reported it, aligning with responsible disclosure. Skeptically, low severity underrates real-world pain: LINE-dependent services, like customer support bots or trading alerts, can’t afford even minutes of blackout during peaks.
Attack Mechanics and Real-World Impact
Reproduce it simply. Spin up a vulnerable OpenClaw instance exposing /webhook/line. Bombard it with unsignable POSTs mimicking LINE payloads:
for i in {1..1000}; do
curl -X POST http://target/webhook/line \
-H "X-Line-Signature: fake" \
-d '{"events":[{"type":"message"}]}' &
done
Without limits, your Node.js event loop or worker pool chokes on parsing and verification attempts. Node’s single-threaded nature amplifies this; high concurrency starves the loop. In containerized setups like Kubernetes, it spikes pod CPU to 100%, triggering restarts if limits enforce.
This matters beyond OpenClaw. Webhook DoS plagues APIs everywhere—GitHub, Slack, Stripe all warn about it. LINE’s scale adds teeth: bots process millions of events daily. Finance apps using LINE for 2FA or crypto alerts face amplified risks. A 5-minute outage during market volatility? Lost trades, frustrated users. Security teams overlook pre-auth limits at their peril; it’s table stakes for public endpoints.
Fair assessment: maintainers acted fast, one day from report to patch. But version numbering (2026.3.x) hints at internal versioning, potentially confusing semver expectations. npm shows latest as 2026.3.31; vulnerable range is <=2026.3.28. Scan your deps with npm ls openclaw or tools like Snyk. No evidence of exploits in the wild yet, but public advisories invite copycats.
Fix, Mitigation, and Best Practices
Upgrade immediately: npm update openclaw pulls >=2026.3.31. The commit adds a shared semaphore or rate limiter pre-signature—details in 57c47d8c diff show concurrency gated to, say, 10-20 handlers. Verify locally post-upgrade.
Even patched, layer defenses. Implement global rate limiting with express-rate-limit or NGINX limit_req:
http {
limit_req_zone $binary_remote_addr zone=line:10m rate=10r/s;
server {
location /webhook/line {
limit_req zone=line burst=20;
proxy_pass http://app;
}
}
}
Other musts: TLS termination with valid certs, body size caps (<1MB), and idempotency keys. Monitor with Prometheus metrics on request rates and errors. For crypto services, isolate LINE handlers in separate services to sandbox DoS.
Bottom line: this exposes sloppy endpoint design many copy. It underscores why pre-auth budgets beat post-auth cleanup. Developers, audit your handlers now—LINE’s growth trajectory demands it. Stay updated via npm audit or GitHub advisories.