Fleet, the open-source osquery-based device management platform, ships with a critical second-order SQL injection flaw in its Apple MDM profile delivery pipeline. An attacker controlling an enrolled device can leverage this to dump or rewrite the entire Fleet database—including admin credentials, API tokens, and device enrollment secrets. This hits anyone running Fleet v4 with Apple MDM enabled, potentially handing over full control of managed device fleets.
The bug surfaces when a device checks in via MDM’s Authenticate command. Attackers craft a malicious UDID, which Fleet stores safely using parameterized queries during initial ingestion. But an async worker later pulls that UDID and splices it raw into SQL queries for profile delivery. This opens doors to blind boolean-based, UNION-based SQLi across four parallel subqueries. Worse, Fleet’s MySQL driver sets multiStatements=true, letting attackers chain queries for arbitrary database writes.
Exploitation Path and Real-World Risk
Exploitation demands a valid SCEP-issued enrollment certificate for mTLS authentication—meaning the attacker must control an already-enrolled device. No zero-days needed there; bring your own compromised Mac or iOS device. Once in, inject payloads target queries building MDM profiles. Stack queries to create admin users, tweak global configs, push rogue profiles or scripts to all devices, or wipe data clean.
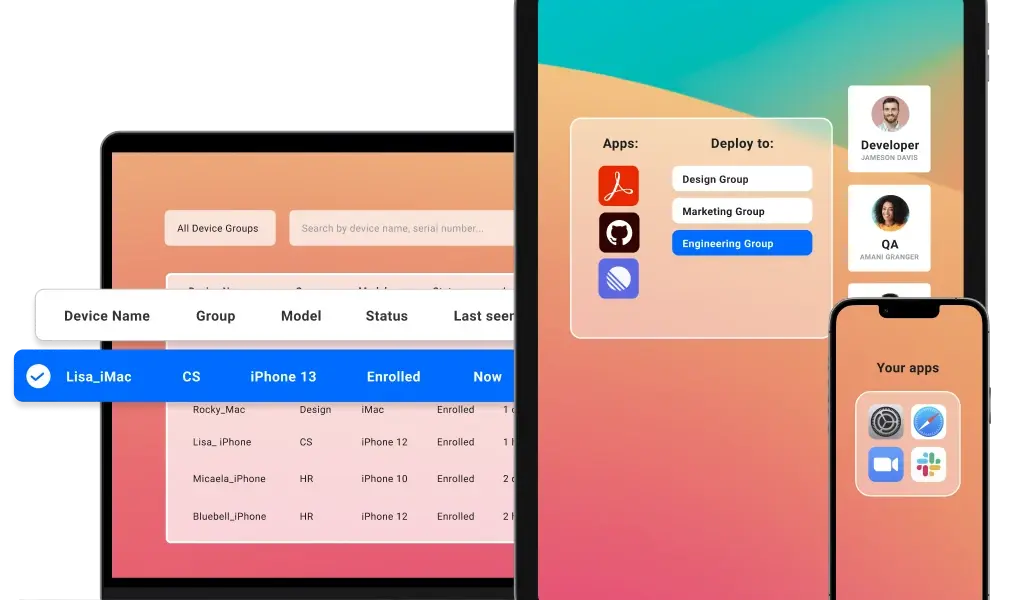
Fleet powers endpoint management for thousands of orgs, from startups to enterprises tracking thousands of devices via osquery. Apple MDM integration lets them enforce policies on Macs and iPads. A breach here cascades: stolen API tokens grant host queries and script execution across the fleet. New admins bypass RBAC. In regulated sectors like finance or healthcare, this equals compliance nightmares and data spills.
Quantify the blast radius: Fleet’s GitHub repo clocks over 5,000 stars and active forks. Osquery Slack hums with users. If your instance handles 100+ devices, one rogue endpoint flips the script. No public exploits yet, but secfox-ai’s responsible disclosure—credited in the advisory—flags it as trivial for skilled attackers. CVSS? Expect high 9.x given remote DB RCE with auth.
Fixes, Workarounds, and What Fleet Gets Right
Upgrade immediately. Fleet patched this in recent v4 releases; check their changelog and scan your go.mod for vulnerable commits. No upgrade? Disable Apple MDM server-side—it’s a config toggle that neuters the vector without broader fallout.
Fleet’s team moved fast post-disclosure, emailing security@fleetdm.com and Slack channels for triage. They enable multiStatements for legit async ops but overlooked input sanitization in workers—a classic second-order trap. Skeptical take: Async queues amplify these bugs; always re-validate inputs downstream. Fair play: Open-source velocity shines here, with fixes merging days after report.
Broader lesson for MDM ops: SCEP certs gate entry but don’t stop payload abuse. Audit your stack—does your MDM (Jamf, Intune, etc.) parameterize everything? Fleet’s MySQL reliance (via go-sql-driver) exposes multiStatements risks; Postgres users dodge this bullet. Run queries like:
$ mysql -u root -p fleet -e "SHOW VARIABLES LIKE 'multiStatements';"
$ go list -m github.com/go-sql-driver/mysql@latest
Why this matters: Device fleets underpin zero-trust. One SQLi unravels it all—creds, secrets, controls. Orgs skimping on open-source hygiene pay dearly. Fleet users, patch now. Watchers, probe your async pipelines. In security, “valid cert” auth feels safe until it doesn’t.
Reported by @secfox-ai; kudos for not dumping it public first. Fleet invites queries at security@fleetdm.com or #fleet on osquery Slack.