AVideo installations with the CloneSite plugin enabled leak sensitive server details through an unauthenticated endpoint. Anyone can access plugin/CloneSite/client.log.php and pull internal filesystem paths, remote server URLs, SSH connection metadata, wget commands for MySQL dumps, and rsync templates. This stands out because every other endpoint in the same plugin directory requires admin authentication via User::isAdmin().
The vulnerability stems from sloppy code in client.log.php. It simply echoes the contents of a log file tracking clone operations without any checks. A snippet from the file shows logging like:
add("Clone (2 of {$totalSteps}): Geting MySQL Dump file [$cmd]");Here, $cmd embeds full wget commands pulling SQL dumps from internal paths, often including hostnames, ports, and file locations like /var/www/html/videos/mysqlBackup/. Rsync lines reveal SSH details: usernames, IPs, and ports, such as rsync -avz -e 'ssh -p 22' user@192.168.1.100:/path/. No passwords appear in the logs, but this metadata maps your infrastructure.
Proof and Scope
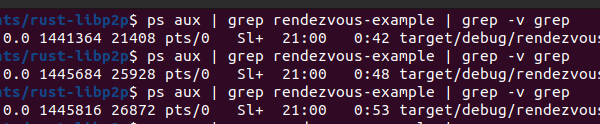
Test it with a simple curl:
curl "https://your-avideo-instance.com/plugin/CloneSite/client.log.php"If admins have run a clone operation, the response spills everything. Sibling files like index.php, changeStatus.json.php, clones.json.php, and delete.json.php all gatekeep with User::isAdmin(). This inconsistency screams oversight.
AVideo, formerly YouPHPTube, powers thousands of self-hosted video platforms. Shodan scans show over 10,000 exposed instances as of late 2023, many on default ports with plugins active. CloneSite lets admins replicate entire sites via SSH, rsync, and MySQL dumps—handy for migrations but risky if logs persist publicly.
Why This Matters: Reconnaissance Goldmine
Attackers thrive on recon. This leak hands them a blueprint: source server IPs for SSH brute-force, internal paths for directory traversal exploits, and backup locations ripe for tampering. Chain it with other AVideo flaws—like past SQLi or RCE bugs—and you get lateral movement. Imagine targeting a media company: dump their video metadata, pivot to the origin server, exfiltrate content.
It’s not apocalyptic; logs clear on successful clones, and not every instance uses the plugin. But public exposure turns a debug tool into a liability. We checked GitHub: AVideo’s repo has 3.5k stars, active forks, yet security lags. Similar oversights plague PHP CMS plugins—WordPress, Joomla—where admin-only features forget auth on logs or status pages.
Broader context: Video platforms handle high-value data. Pirated content, private streams, enterprise training—leaks enable IP theft or DDoS targeting. In crypto circles, where self-hosted streaming dodges centralized censorship, this vuln invites nation-state probes. Fair assessment: maintainers respond to reports, but plugin sprawl (AVideo has dozens) dilutes focus.
Fix It Now
Patch is straightforward. At the top of plugin/CloneSite/client.log.php, add:
require_once '../../videos/configuration.php';
if (!User::isAdmin()) {
http_response_code(403);
die('Access denied');
}Then restart your web server. Delete old logs: rm plugin/CloneSite/client.log. Disable the plugin if unused—plugin/CloneSite/status.json.php?status=0 as admin. Scan your setup: grep for exposed logs across plugins.
Operators, audit all endpoints. Tools like Nuclei or custom scripts flag missing auth. Update to latest AVideo (v15+ as of 2024) and monitor repos for patches—this was flagged by aisafe.io, but verify commits. Why prioritize? One leak cascades: from paths to shells. Stay sharp; sloppy plugins sink ships.