AVideo, the open-source video platform forked from YouPHPTube, ships with a CloneSite plugin that clones entire sites via SSH and MySQL dumps. A flaw in this plugin exposes sensitive server details to anyone without login credentials. The endpoint at plugin/CloneSite/client.log.php serves operation logs raw—no authentication required. All other endpoints in the same directory enforce User::isAdmin().
This matters because those logs contain real ammunition for attackers: internal filesystem paths, wget commands pulling MySQL dumps from remote hosts, rsync templates with SSH usernames, IP addresses, and ports. If you’ve ever used CloneSite to duplicate a site, curl this endpoint and you hand over your infrastructure map.
Technical Breakdown
The vulnerable file is a simple PHP script. It reads and echoes the client.log without checks:
add("Clone (2 of {$totalSteps}): Geting MySQL Dump file [$cmd]");Here, $cmd embeds commands like wget to internal paths (e.g., /var/www/html/videos/) and rsync over SSH (e.g., rsync -avz -e "ssh -p 22" user@192.168.1.100:/path/). Sibling files like index.php, changeStatus.json.php, clones.json.php, and delete.json.php all start with if (!User::isAdmin()) { die('Access denied'); }. This one skipped it.
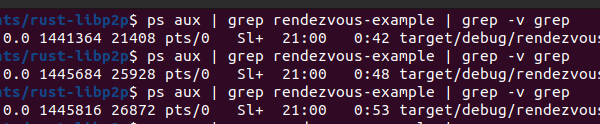
Proof of concept is trivial:
curl "https://your-avideo-instance.com/plugin/CloneSite/client.log.php"If CloneSite ran at least once, you get the logs. AVideo powers thousands of self-hosted instances—Shodan shows over 10,000 exposed ports running it as of late 2023. Many enable plugins like this for migrations or backups. Attackers scan for these, hit the endpoint, and pivot.
Real-World Risks and Fixes
Severity lands at medium for good reason: no RCE or auth bypass, just info disclosure. But it counts. Exposed paths reveal web roots, database locations. SSH metadata spotlights clone source servers—often production environments with videos, user data. Attackers chain this: guess weak SSH keys (common in clones), phish admins with tailored lures, or scan those IPs for other vulns. In crypto-adjacent setups, where AVideo hosts tokenized content or streams, this leaks backend VPS details, aiding DDoS or ransomware prep.
AVideo’s GitHub (wwbn/AVideo) has 3k+ stars, active forks for enterprise tweaks. CloneSite debuted around v5.x for easier scaling. No patch yet in mainline; advisory from aisafe.io flagged it recently. Self-hosters often run unpatched—check your plugin/CloneSite/ dir.
Fix it yourself: prepend this to client.log.php:
require_once '../../videos/configuration.php';
if (!User::isAdmin()) {
http_response_code(403);
die('Access denied');
}Delete old logs too—rm plugin/CloneSite/client.log. Disable the plugin if unused; it’s opt-in but sticky. Broader lesson: PHP apps like AVideo thrive on plugins, but each adds attack surface. Audit endpoints, enforce auth everywhere. Scan your instance with Nuclei or similar—templates exist for AVideo misconfigs. This isn’t hype; it’s a reminder that “free video platform” means you secure the stack.
Update AVideo core regularly, but verify plugins. If cloning sites, use air-gapped tools or Vault for secrets. Attackers love lazy migrations—don’t feed them.