AVideo’s CloneSite plugin exposes sensitive server logs to anyone without authentication. The endpoint at plugin/CloneSite/client.log.php dumps operation logs containing internal filesystem paths, wget commands pulling MySQL dumps, rsync templates with SSH usernames, IPs, and ports. Every other endpoint in the same directory requires User::isAdmin() checks. Attackers hitting public AVideo instances can grab this data instantly via a simple curl request.
AVideo, an open-source PHP-based video sharing platform similar to YouTube for self-hosting, powers thousands of sites worldwide. The CloneSite plugin lets admins duplicate another AVideo setup remotely—pulling videos, databases, and files via SSH and rsync. It’s convenient for migrations or backups but turns risky when logs leak unauthenticated. If you’ve ever run a clone operation, that log file persists and reveals your infrastructure blueprint.
Vulnerability Breakdown
The file plugin/CloneSite/client.log.php lacks any security gate. It directly echoes log lines like:
add("Clone (2 of {$totalSteps}): Geting MySQL Dump file [$cmd]");Here, $cmd embeds full wget invocations targeting internal paths, such as SQL dump locations, plus rsync strings formatted as rsync -avz -e "ssh -p [port] -l [user]" user@[ip]:/path/. Sibling files enforce admin auth rigorously:
plugin/CloneSite/index.php:User::isAdmin()plugin/CloneSite/changeStatus.json.php:User::isAdmin()plugin/CloneSite/clones.json.php:User::isAdmin()plugin/CloneSite/delete.json.php:User::isAdmin()
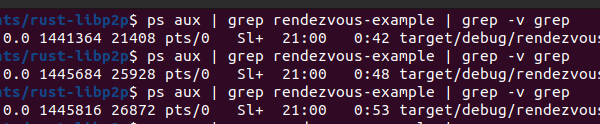
Proof comes easy. Run this against any exposed AVideo with CloneSite active:
curl "https://your-avideo-instance.com/plugin/CloneSite/client.log.php"Expect output spilling paths like /var/www/html/videos/, remote SSH endpoints, and dump files. No login needed. Discovered by aisafe.io, this sits at medium severity—info disclosure, not RCE—but packs real punch for reconnaissance.
Why This Exposes You
Self-hosted video platforms draw attackers scanning for easy wins. AVideo instances often run on cheap VPS with default configs, SSH on non-standard ports, and weak keys. Leaked paths enable targeted exploits: path traversal if other vulns exist, or directory brute-forcing. SSH details? Direct ammo for brute-force or phishing the source server. MySQL dump locations hint at DB creds patterns or unpatched servers.
Scale matters. AVideo claims over 10,000 deployments per their GitHub stats. Shodan shows hundreds of public instances monthly. Cross-reference with this leak, and you map attack surfaces. We’ve seen similar slips in WordPress plugins or Nextcloud apps lead to full compromises—think Equifax paths aiding lateral moves. Here, it fingerprints your clone source, potentially a production server with user videos and payments.
Beyond direct harm, it signals sloppy plugin dev. AVideo’s core audits better, but plugins lag. CloneSite last updated months ago; no CVE yet, but expect one. Implications hit operators hard: disable unused plugins, firewall endpoints, rotate SSH creds post-leak. For clone targets, monitor logs for probes spiking after scans.
Fix It Now
Patch takes two lines. At the top of plugin/CloneSite/client.log.php, insert:
require_once '../../videos/configuration.php';
if (!User::isAdmin()) {
http_response_code(403);
die('Access denied');
}Test it—admin sees logs, randos get 403. Then, delete old logs: rm plugin/CloneSite/client.log. Update AVideo core and plugins via GitHub. Audit siblings: grep for auth skips across plugin/.
Bottom line: Convenience plugins like CloneSite trade security for speed. If you self-host video, weigh the risk—expose once, regret long. Scan your instance today; tools like Nuclei have AVideo templates. Stay sharp, or become the next leak.