Someone routed their internet traffic through a Tailscale exit node running on their home server and traced every packet. The result? Clean encapsulation, no leaks detected, but your home IP address becomes the public face of all that traffic. ISPs, websites, and adversaries see your residential connection, not some data center.
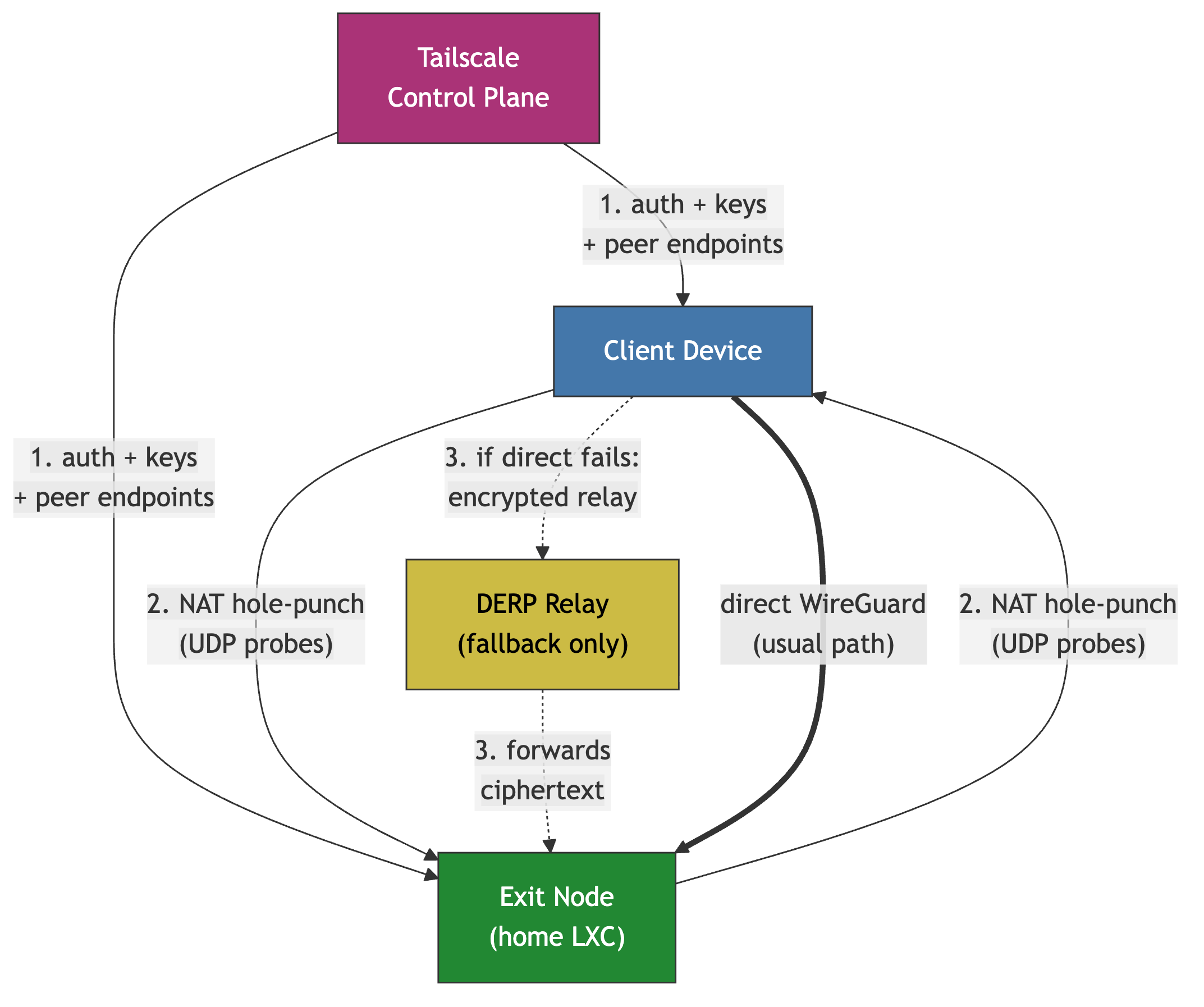
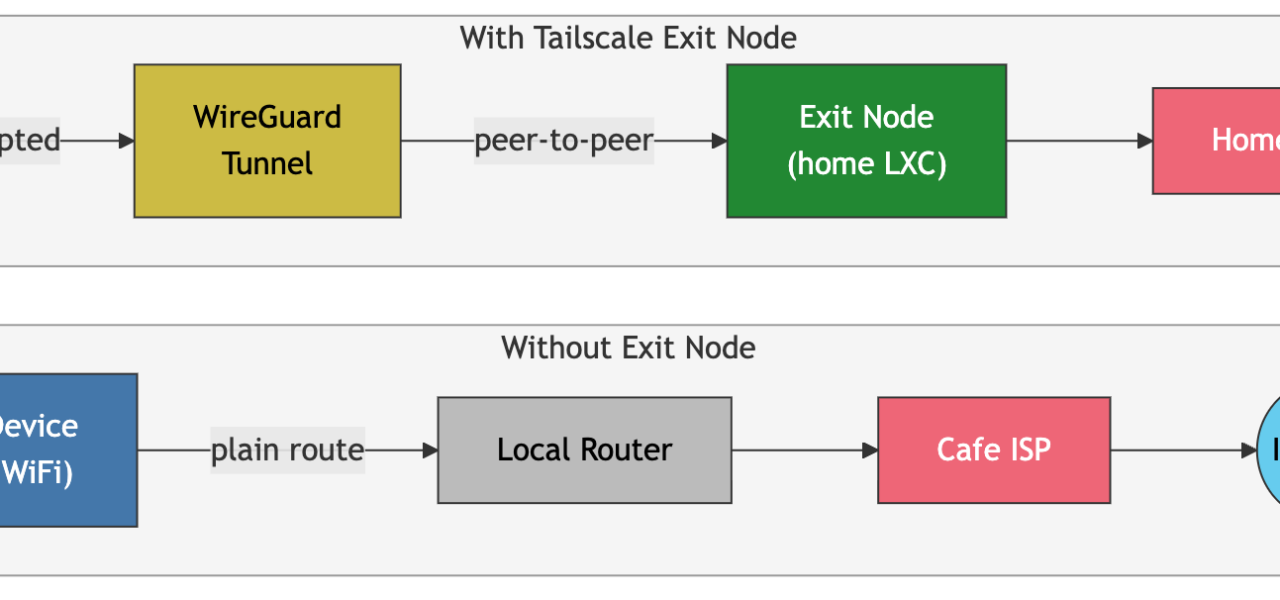
This experiment, shared on Hacker News, cuts to the core of Tailscale’s appeal and pitfalls. Tailscale builds a peer-to-peer mesh VPN on WireGuard, letting devices connect securely without port forwarding. Exit nodes take it further: tag a machine with --advertise-exit-node, and clients route all outbound traffic through it. In 2023, Tailscale hit 2 million users, mostly developers and small teams ditching OpenVPN hassles.
The Trace: How Traffic Flows
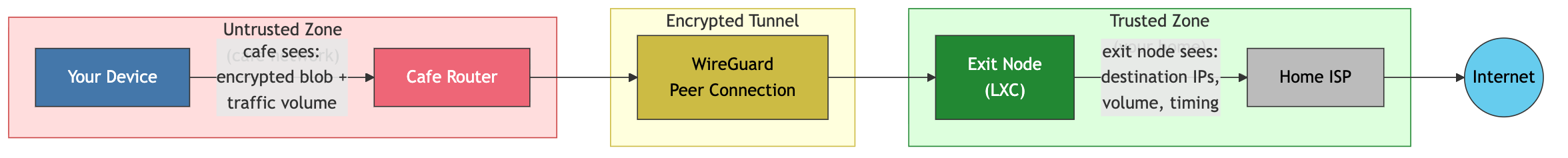
The author fired up Wireshark on the client and tcpdump on the Linux home server acting as exit node. Client sends UDP packets over WireGuard to the exit node’s tailscale IP (100.x.x.x range). Those packets carry the full IP stack: original TCP/UDP destined for the internet.
On the exit node:
sudo tcpdump -i tailscale0 -n -v
Packets arrive encrypted, Tailscale decapsulates them. The server applies NAT via iptables (SNAT on postrouting), rewriting source IP to its public residential one—say, 203.0.113.42 from Comcast. Then out via eth0 to the destination. Return traffic reverses: destination replies to home IP, server DNATs back to client tailscale IP, re-encapsulates in WireGuard.
No IPv6 leaks if disabled properly. DNS queries? Tailscale’s MagicDNS resolves via the tailnet, but you can override with exit node’s DNS. The trace confirmed zero leakage: nothing escaped the tunnel. Latency added 20-50ms roundtrip from client in Europe to US home server, per the post’s graphs.
Facts match Tailscale docs: they use userspace WireGuard (wireguard-go) for cross-platform, with kernel mode on Linux for speed. Exit nodes require ACL approval in tailnet policy files—JSON like {"acls": [{"action": "accept", "src": ["autogroup:internet"], "dst": ["autogroup:internet"]}]}.
Risks and Realities
It works, but why does this matter? Your home IP screams “person,” not “VPN service.” Websites log it; Netflix blocks it faster than datacenter IPs. ISPs retain connection logs for 6-12 months under US CALEA rules, tying activity to your billing address. In 2022, Tailscale disclosed a supply-chain vuln in their installer, fixed promptly—reminder that even “zero trust” needs vigilance.
Skeptical take: Tailscale beats consumer VPNs like ExpressVPN on privacy (no central logs, E2E encrypted mesh), but exit nodes demand trust. Use a friend’s home node? They see your decapsulated traffic metadata. Compromise their box, and you’re exposed. Home setups face port scans, DDoS if your IP hits blocklists from client abuse.
Numbers: Tailscale’s 2023 Series C valued them at $500M+ after 1M+ devices. Competitors like Netmaker or Headscale (open-source Tailscale control server) offer self-hosting, dodging SaaS reliance. For anonymity, chain with Tor or a VPS exit—but that adds hops, latency spikes to 200ms+.
Pro tip: Run exit on a VPS ($5/mo at Vultr) with clean IP rotation. Monitor with tailscale status --json | jq '.ExitNodes'. Test leaks at ipleak.net post-setup.
Bottom line: Tailscale exit nodes deliver reliable tunneling for remote work or bypassing geo-blocks. The trace proves technical solidity, but implications hit privacy hard. Residential IPs deanonymize you—use accordingly, or stick to SOCKS proxies for subtlety. Devs love it for tailnet-internal access; don’t treat it as full Tor.