A malicious miner can split Zebra nodes from the Zcash network. They craft a block with a V5 transaction that shares a txid with a valid one in the mempool but carries invalid authorization data—bad signatures or proofs. Vulnerable Zebra nodes skip verification, accept the block, and fork away from zcashd and fixed Zebra nodes. This hits all Zebra versions from Network Upgrade 5 (activated September 2022) up to but not including 4.3.0. Upgrade now to 4.3.0 or later. No workarounds exist.
How the Bug Works
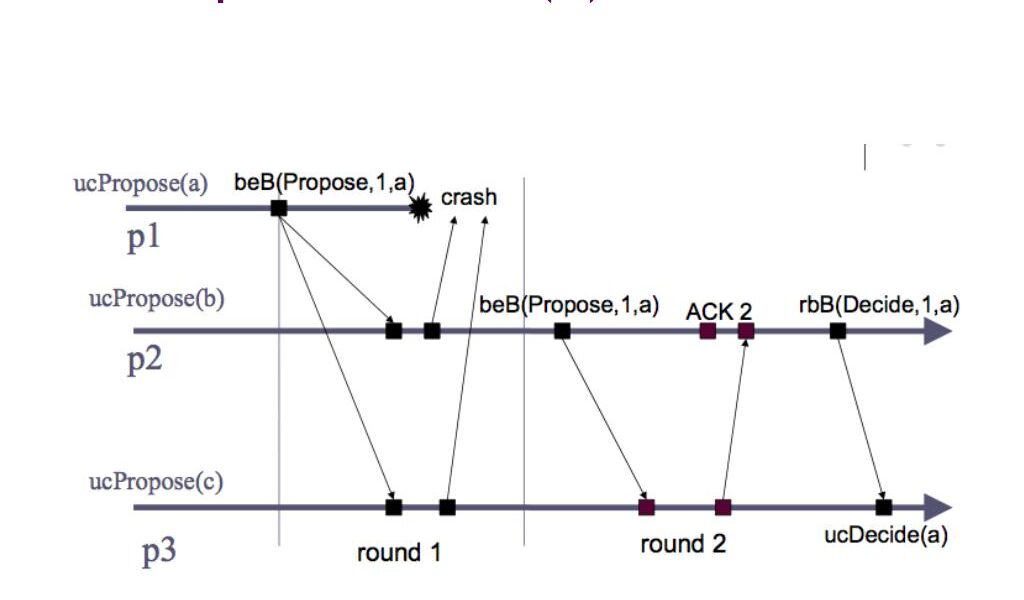
Zebra’s find_verified_unmined_tx in transaction.rs caches verified mempool transactions by ZIP-244 txid. For V5 Orchard transactions, txid excludes the Authorization Data Root, which holds signatures and spend proofs. A node sees a valid V5 tx broadcast, verifies it, and caches it.
The attacker mines a block swapping in a tampered version: same txid, broken auth data. Zebra matches the txid, assumes verification done, skips check_v5_auth(), and commits the invalid tx. Non-vulnerable nodes reject it outright.
Result: fork. Vulnerable Zebras chain off alone. Zcashd and safe Zebras stay on the valid chain. Attack needs miner control—submit the poisoned block. No invalid spends get confirmed network-wide, but isolated nodes face disruption.
Why This Matters for Zcash
Zcash runs on proof-of-work with ~5-10 MH/s hash rate lately, down from peaks over 100 MH/s in 2018. Zebra, the Rust node, powers about 20-30% of nodes per recent scans, though exact splits vary. A miner with even 5-10% hash power could orphan the vulnerable chain repeatedly, isolating Zebras.
Implications cut deep. Affected nodes desync, halt syncing new blocks. Users on them risk double-spends: miner confirms a spend on the fork, then broadcasts valid chain elsewhere. Exchanges or wallets using Zebra? Frozen funds until resync. Network partition weakens Zcash’s already thin liquidity—market cap hovers $300-500M, daily volume $20-50M.
Skeptical take: Zcash adoption lags Bitcoin/Ethereum. NU5 brought Orchard for better privacy/efficiency over Sapling, but bugs like this erode trust. Zebra devs fixed fast—4.3.0 drops September 2024-ish? Still, why miss auth root in txid cache? ZIP-244 standardizes txids sans auth for consistency, but verification must check full tx integrity. Sloppy shortcut.
Broader crypto lesson: Alternative impls like Zebra aim for diversity against zcashd monoculture, but introduce risks. Bitcoin’s knot/Bitcoin Core split showed forks hurt. Zcash Electric Coin Co. pushes Zebra; operators weigh Rust safety vs. zcashd maturity.
Monitor: No exploits reported yet. Zcash chain at height 2.4M+, NU5 block 1,945,000. Zebra 4.3.0 patches by validating full tx against mempool, including auth. Testnet repro exists in their repo.
Action: Run zebrad --version. If below 4.3.0 and V5-enabled, shut down, pull latest release, restart. Verify chain tip matches explorers like zcash.network. Zcashd 5.9.0+ unaffected—consider switching if Zebra’s your default.
$ git clone https://github.com/ZcashFoundation/zebra
$ cd zebra
$ git checkout v4.3.0
$ cargo build --release
# Or use binaries from GitHub releases
Stay vigilant. Consensus bugs kill chains slower than exploits but surer. Zcash survives if nodes upgrade fast.