OpenSTAManager versions up to and including 2.10.1 suffer from a critical authenticated SQL injection vulnerability in the Aggiornamenti module. Attackers with read-write access to this module can send a JSON array of arbitrary SQL statements via POST request, which the application executes directly against the MySQL database. No validation, sanitization, or allowlist blocks dangerous commands like DROP TABLE, INSERT, or even SELECT INTO OUTFILE for data exfiltration.
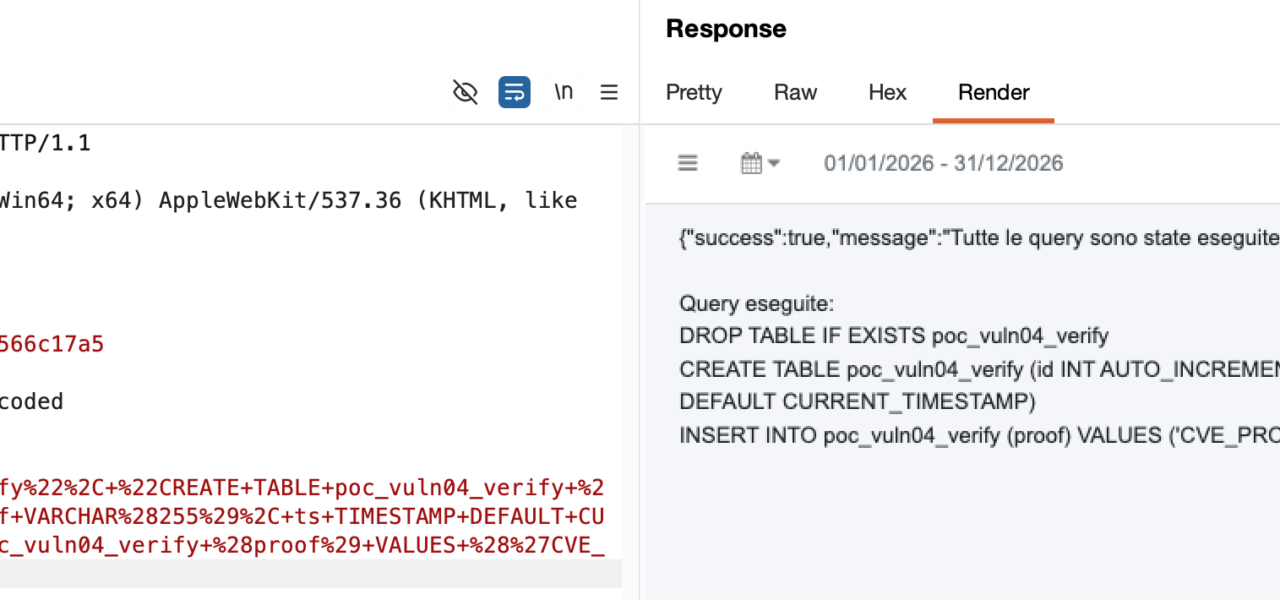
The flaw resides in modules/aggiornamenti/actions.php, lines 40-82. Developers grab user-supplied queries from POST, decode it as JSON into an array, disable foreign key checks with SET FOREIGN_KEY_CHECKS=0, then loop through each string and fire it off via $dbo->query($query). Errors leak database details back to the attacker in the JSON response. Foreign key checks re-enable afterward, but damage is already done.
case 'risolvi-conflitti-database':
$queries_json = post('queries'); // Line 41: User input
// ...
$queries = json_decode($queries_json, true); // Line 50
// ...
$dbo->query('SET FOREIGN_KEY_CHECKS=0'); // Line 69
foreach ($queries as $query) {
try {
$dbo->query($query); // Line 76: Arbitrary SQL
} catch (Exception $e) {
$errors[] = $query . ' - ' . $e->getMessage(); // Line 79: Leakage
}
}
$dbo->query('SET FOREIGN_KEY_CHECKS=1'); // Line 82
Exploitation Path
Trigger it with a POST to /editor.php?id_module=aggiornamenti and op=risolvi-conflitti-database, including queries as a JSON array like ["SELECT 1; DROP TABLE users;"]. The root editor.php checks module permission (rw required), then includes the module’s actions.php. No further auth blocks this. Default admin accounts have full access.
The feature aims to resolve DB schema conflicts during updates. Fair intent, but zero restrictions turn it into a backdoor. Any teacher, staffer, or compromised low-priv user with rw on Aggiornamenti owns the DB. MySQL supports it all: schema changes, data dumps, file writes if server perms allow.
Real-World Impact
OpenSTAManager is an open-source ERP for Italian schools, handling student records, grades, attendance, payments, and PII like tax codes and addresses. Thousands of Italian institutes run it—GitHub repo shows steady stars and forks. A breach dumps 10,000+ student profiles per school, enables grade tampering, or ransomware via mass deletes.
Why this matters: Education sector lags on security. Schools rarely patch promptly; budgets tight. Authenticated-only lowers bar—no phishing needed if insiders exist. Attackers chain this to pivot: exfil data, install webshells via SQL, escalate to server root. Post-GDPR, fines hit hard—€20M or 4% revenue for lax PII handling.
Check your setup: Scan logs for risolvi-conflitti-database POSTs. Revoke Aggiornamenti rw except trusted admins. Latest version (2.10.2+) likely patches—devcode-it repo commits post-2.10.1 add validation. If stuck, proxy queries through PDO prepared statements or whitelist ops like ALTER TABLE only.
Skeptical note: Devs built this for convenience, not malice, but skipping basics like query parsing invites abuse. Test your updates module rigorously—JSON SQL exec is a red flag in any app. Schools, audit now: run SELECT * FROM users WHERE 1=1 via PoC to confirm, then lock it down.