A high-severity vulnerability in the npm package openclaw lets low-privileged users delete any session by impersonating an admin. Developers using versions up to 2026.3.24 face risks of unauthorized session deletions, potentially disrupting services or enabling denial-of-service attacks in gateway plugin setups.
The bug hits the Gateway Plugin Subagent’s fallback deleteSession function. When no request-scoped client exists, it previously dispatched sessions.delete with a synthetic operator.admin runtime scope. This mints fake admin privileges, bypassing proper authorization checks. Attackers with minimal access could wipe out sessions across the system.
Vulnerability Breakdown
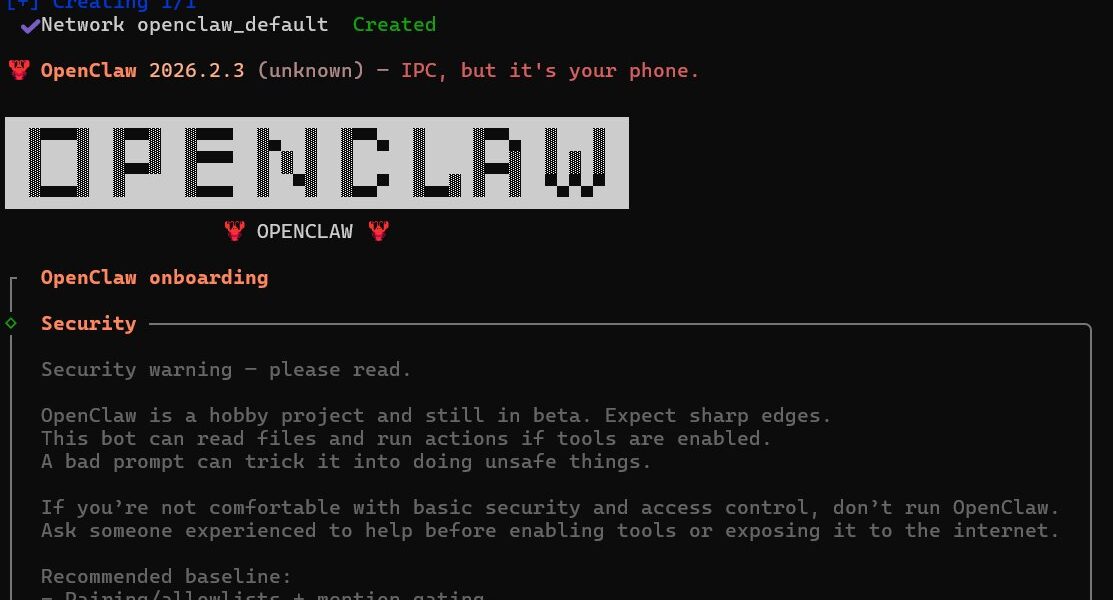
OpenClaw handles gateway plugins and subagents, likely in backend systems managing sessions for APIs or services. The flawed logic appears in the subagent fallback: instead of tying deletions to the caller’s actual scope, it elevates to admin level by default. Commit b5d785f1a59a56c3471f2cef328f7c9a6c15f3e7 fixes this by binding deletions strictly to the caller’s scope.
Security researchers verified the issue on tag v2026.3.24, the latest published npm version at the time. The patch landed on the main branch and rolls out in 2026.3.25. No exploits in the wild yet, but the setup screams supply-chain risk—npm pulls in thousands of deps daily.
Why does this matter? Sessions often hold user state, auth tokens, or transaction data. Deleting them arbitrarily lets attackers log out users en masse, corrupt workflows, or chain into bigger breaches. In multi-tenant environments, one compromised low-priv account turns into system-wide chaos. Think fintech gateways or crypto exchanges: a single bad dep, and downtime costs thousands per minute.
Impact and Real-World Risks
Affected versions: all openclaw <= 2026.3.24. If your project pulls this transitive dep, you’re exposed. npm’s ecosystem logs over 1.5 billion package installs weekly; vulns like this slip through because maintainers juggle open-source upkeep with day jobs.
Attack vector requires access to invoke the subagent fallback—perhaps via a plugin endpoint or misconfigured proxy. No auth? Synthetic admin kicks in. Post-exploit, deleted sessions mean forced reauths, data loss, or service outages. Severity tags as [HIGH] for good reason: CVSS could hit 7.5+ if remote and unauthenticated.
Skeptical take: OpenClaw’s niche use in gateway subagents limits blast radius compared to mega-packages like lodash. But ignore it, and you invite quiet pivots. We’ve seen similar RBAC fails in Express middleware or Socket.io handlers lead to outages at scale. In crypto circles, where Njalla operates, session tampering equals wallet drains or trade halts.
Broader context: npm advisories spike 30% yearly, per Snyk data. Synthetic privileges echo past bugs like SolarWinds or Log4Shell—over-trusting internals. Fair point: the fix is surgical, one commit. But it exposes how fallback logic often hides sharp edges.
Fix, Mitigation, and Next Steps
Update immediately to openclaw@2026.3.25 or later. Run
npm audit fixthen
npm update openclaw. Lock deps with package-lock.json and scan CI/CD pipelines.
Mitigate now: Scope down subagent calls to authenticated contexts only. Audit logs for deleteSession invocations. Proxy gateways? Enforce RBAC at the edge with tools like Kong or Traefik.
Long-term: Ditch synthetic scopes entirely. Use proper JWT claims or OPA for policy. Run npm ls openclaw to check exposure. Tools like Socket or Dependabot automate this.
This vuln underscores npm’s double-edge: speed vs. scrutiny. Patch fast, but question every fallback. In security, trust no one—not even your own code.