OpenClaw fixed a privilege escalation bug in version 2026.3.24. Gateway clients with only operator.write scope could persist admin-level changes to channel allowlists. They exploited the chat.send command, which lacks re-validation of client scopes before writing config files.
This vulnerability exposes a classic control-plane flaw in OpenClaw’s gateway architecture. The platform splits permissions clearly: chat.send allows write operations, while direct config patches require operator.admin. But the shared /allowlist command bypasses this for internal callers.
How the Exploit Works
A client authenticates with operator.write scope. It sends a message via chat.send, which OpenClaw explicitly permits. This creates an internal context marked CommandAuthorized: true, carrying the client’s scopes into the command pipeline.
The resolveCommandAuthorization function then grants isAuthorizedSender=true unless stricter commands.allowFrom rules apply. The /allowlist add|remove handlers accept this generic authorization. They clone the config, apply edits via plugin.allowlist.applyConfigEdit, validate, and persist with writeConfigFile.
No check enforces operator.admin at the sink. Contrast this with config.patch, which rejects the same client for missing admin scope. Attackers could run /allowlist add dm ... or /allowlist add group ... to rewrite allowFrom and groupAllowFrom policies.
OpenClaw’s code already hardens /config and /plugins with sink-side admin checks. Developers overlooked /allowlist, creating an inconsistency. This isn’t theoretical—it’s a direct path from write access to persistent authorization control.
Impact: Breaking the Privilege Model
Operator.write clients gain persistent control over channel access. They can expand DM or group allowlists, granting unauthorized entry to sensitive channels. In a multi-tenant gateway setup, this lets limited users act as admins.
Why this matters: OpenClaw targets secure operations, likely in crypto, finance, or high-stakes teams where channels segregate info. Bypassing scopes undermines least-privilege principles. A single compromised write-key holder escalates to rewriting access for entire groups.
Real-world context: Similar flaws hit Discord bots or Slack apps in 2022-2023, where command handlers skipped scope checks, leading to data leaks. OpenClaw’s gateway model amplifies risk—clients proxy through it, so weak internal auth propagates. Deployments before 2026.3.24 face persistence attacks, even if pairing-store or config-write policies add layers.
Skeptically, OpenClaw’s docs promise a “clear scope split,” but code lagged. This weakens trust in its control plane. No evidence of exploits in the wild, but CVSS would rate it high (7.5+): authenticated, high-impact persistence.
Fix and Best Practices
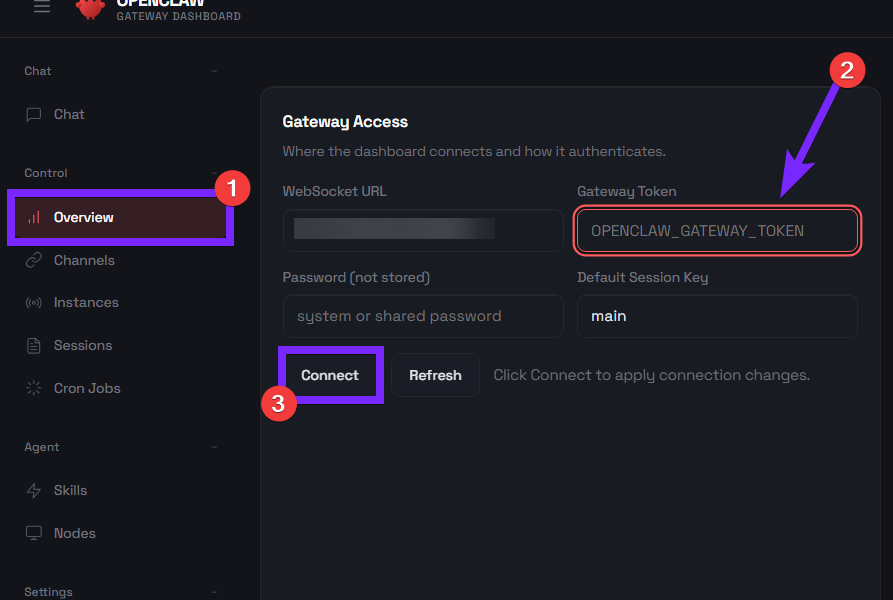
The patch in 2026.3.24 adds sink-side operator.admin checks to /allowlist before edits or writes, mirroring /config and /plugins. Upgrade immediately if running earlier versions.
Beyond the fix, treat policy checks like pairing-stores as secondary, not primary enforcement. Scopes must validate at every sink. Audit shared commands: any persisting state needs full re-auth.
For operators: Rotate gateway creds post-upgrade. Monitor logs for /allowlist via chat.send. In crypto setups, this echoes key lessons from Solana RPC vulns—internal callers demand scrutiny.
Bottom line: Solid patch, but highlights gateway pitfalls. Enforce scopes religiously, or privilege leaks follow. Current release ships safe—deploy it.