Antrea’s IPsec encryption fails to protect IPv6 pod traffic in dual-stack Kubernetes clusters. Administrators who enable trafficEncryptionMode: ipsec expect node-to-node pod communication to stay encrypted. IPv4 traffic uses ESP encapsulation correctly, but IPv6 packets bypass it entirely, traveling in plaintext inside Geneve or VXLAN tunnels. This CWE-311 vulnerability exposes inter-node pod data to eavesdroppers on the network fabric.
Only dual-stack setups suffer. Single-stack IPv4 or pure IPv6 clusters remain secure under IPsec. Antrea, an Open vSwitch-based CNI plugin for Kubernetes, targets enterprises needing advanced networking like service mesh integration and traffic encryption. With over 10,000 GitHub stars and adoption in production by firms like VMware, this flaw hits users relying on its IPsec for compliance-heavy workloads. Kubernetes dual-stack support has surged since v1.23 (2022), driven by IPv6 mandates in clouds like AWS and Azure. Misconfigurations like this undermine that shift.
Scope and Real-World Risk
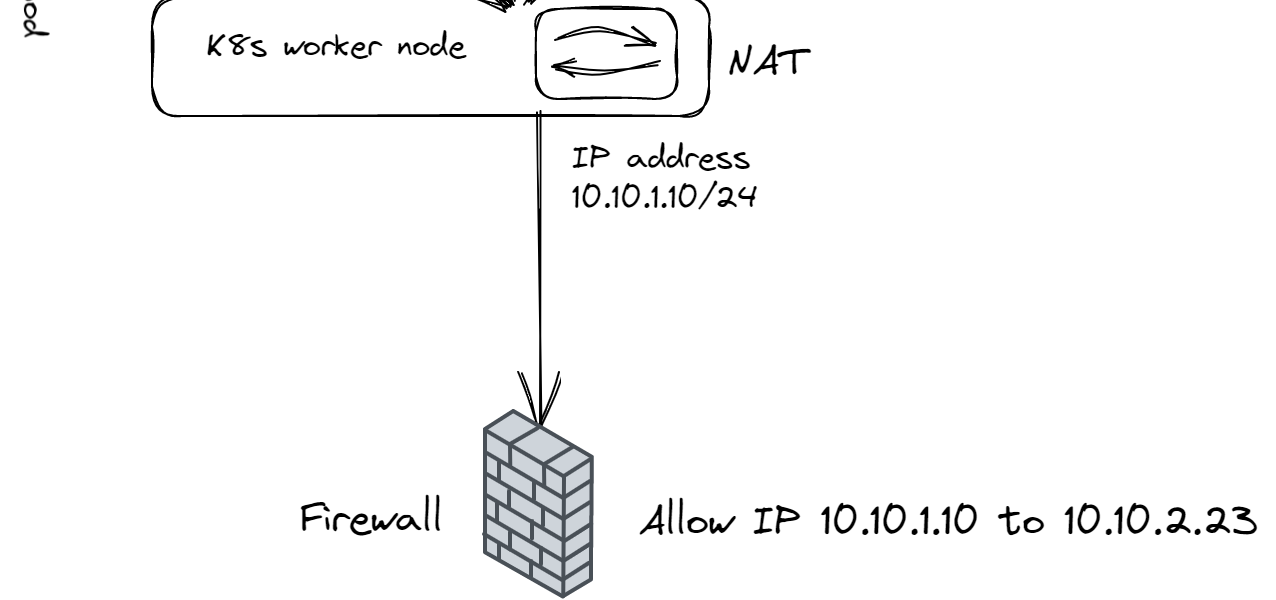
The breach affects pod-to-pod traffic across nodes, not host-to-host or external links. In a typical multi-node cluster, this means sensitive data—API calls, database queries, configs—leaks if pods use IPv6. Attackers with network access (rogue nodes, compromised underlay, insiders) can sniff or tamper. No evidence of active exploits yet, but CVSS scoring (likely 7+ for confidentiality impact) flags it high. Kubernetes Report 2023 shows 40% of clusters run dual-stack, up from 20% in 2022. If your apps prefer IPv6 for performance or policy, exposure multiplies.
Why this matters: Encryption promises fail silently. Admins check IPv4 with Wireshark, miss IPv6 gaps. Compliance standards (SOC2, GDPR) demand consistent protection; audits now scrutinize dual-stack. In finance or crypto ops on K8s—think DeFi nodes or trading bots—this invites regulatory heat and breach costs averaging $4.5M per IBM’s 2024 report.
Patches and Mitigation
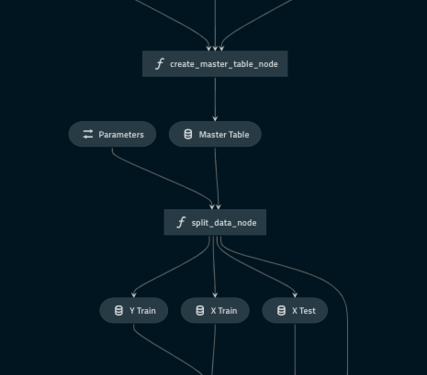
Antrea patched fast via PR #7759. Upgrade to v2.6.0+, v2.5.2, or v2.4.5. Post-upgrade, run
antctl check installation --run ipsecto confirm ESP headers on both IPv4 and IPv6. The tool, enhanced in PR #7757, generates test traffic and verifies encryption—use it routinely.
No config tweak fixes it pre-patch. Switch to WireGuard mode immediately: trafficEncryptionMode: wireguard. Antrea’s WireGuard implementation handles dual-stack IPv6 correctly, with lighter overhead (5-10% CPU vs. IPsec’s 20-30%). Docs warn WireGuard needs UDP 51820 open; test throughput first.
Antrea maintainers deserve credit for transparency—advisory out within days of discovery, no downplaying. Still, it exposes dual-stack testing gaps in CNI projects. Cilium and Calico face similar IPv6 hurdles historically. Vet your stack: enable IPv6 only if needed, monitor with eBPF tools like Tetragon.
Bottom line: Patch now if dual-stack IPsec. This reinforces IPv6’s growing pains in K8s—benefits like 128-bit addressing and native security clash with immature tooling. Secure clusters demand verification beyond defaults.