Financial cybercriminals in 2025 ditched complex banking Trojans for simpler infostealers that harvest credentials en masse. This pivot cut PC malware’s share but exploded stolen data sales on the dark web, fueling account takeovers and fraud worth billions. Kaspersky’s analysis of its Security Network (KSN) data from user devices, plus dark web scans, shows attackers now aggregate old leaks with fresh steals, skipping heavy R&D on new malware. Why it matters: Banks and crypto exchanges face endless reuse attacks; users lose control when one password breach cascades across services.
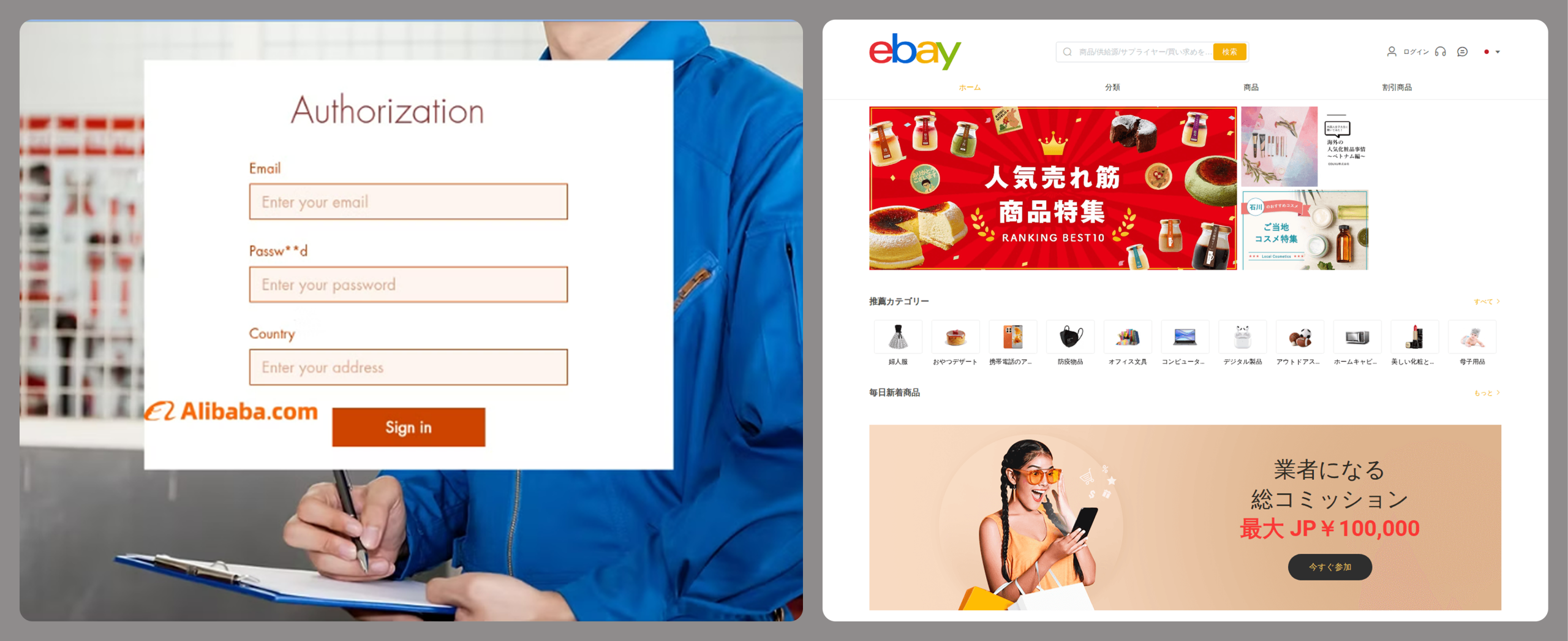
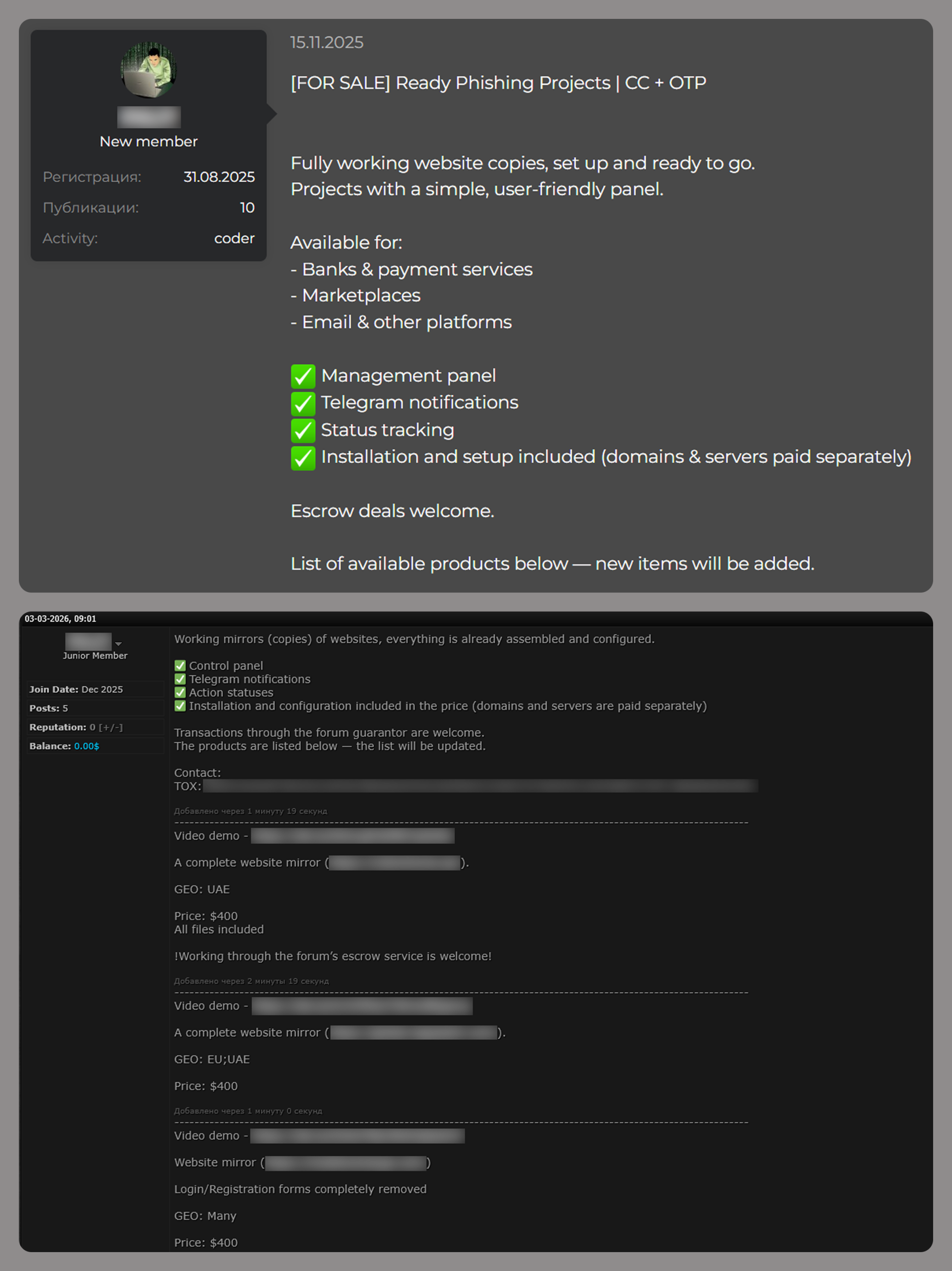
Phishing evolved too, ditching blunt bank lures for targeted scams on e-commerce and digital hubs. Global stats peg web services at 16.15% of attacks, online stores at 14.17%, and games at 14.58%—up from social networks and pure banking sites in 2024. Attackers mimic brands like Amazon or Steam, timing hits around sales or game drops to exploit impulse buys. Regional tweaks make it stickier: Latin America sees payment app fakes; Europe targets crypto wallets. Skeptical note: KSN data skews to protected users, undercounting raw phishing volume, but trends hold—social engineering now outsmarts antivirus alone.
Banking Malware: PC Fades, Mobile Surges
Traditional PC banking malware dropped in prevalence, with families like Dridex and TrickBot limping on without innovation. Attackers favor infostealers for low-effort credential grabs over keystroke-logging Trojans that banks block routinely. Mobile malware, however, grew unchecked—Android Trojans like Ermac spiked, per Kaspersky’s separate report. In 2025, over 1.5 million mobile banking detections hit KSN, up 20% year-over-year in high-risk regions like Russia and India.
Implications hit hard for finance pros: Legacy PC defenses work, but phones are the weak link. Fraudsters proxy stolen mobile sessions to bypass geo-checks, draining accounts in real-time. Crypto users? Seed phrases stolen via mobile infostealers mean total loss—no reversals.
Infostealers Fuel Dark Web Fraud Machine
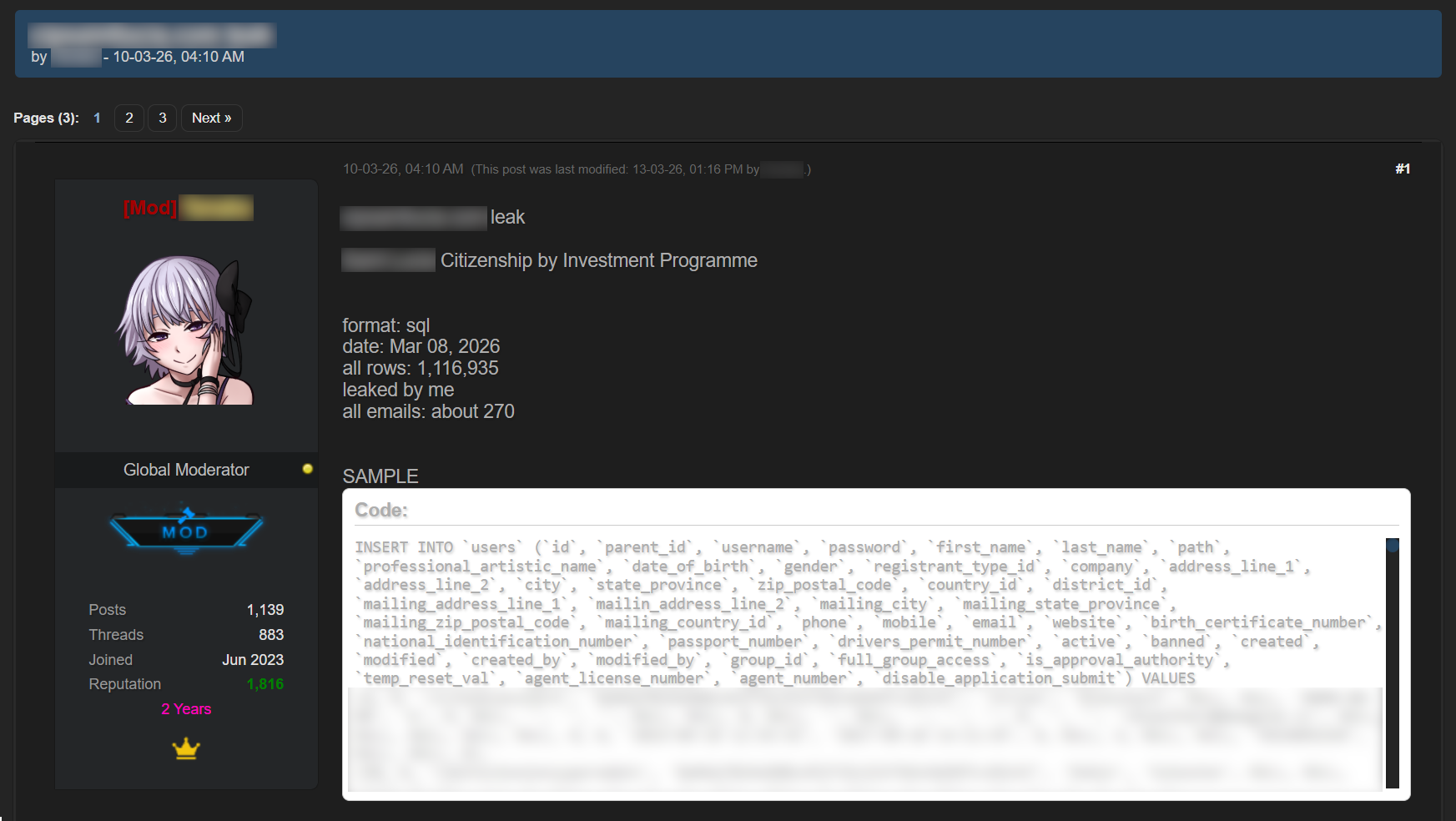
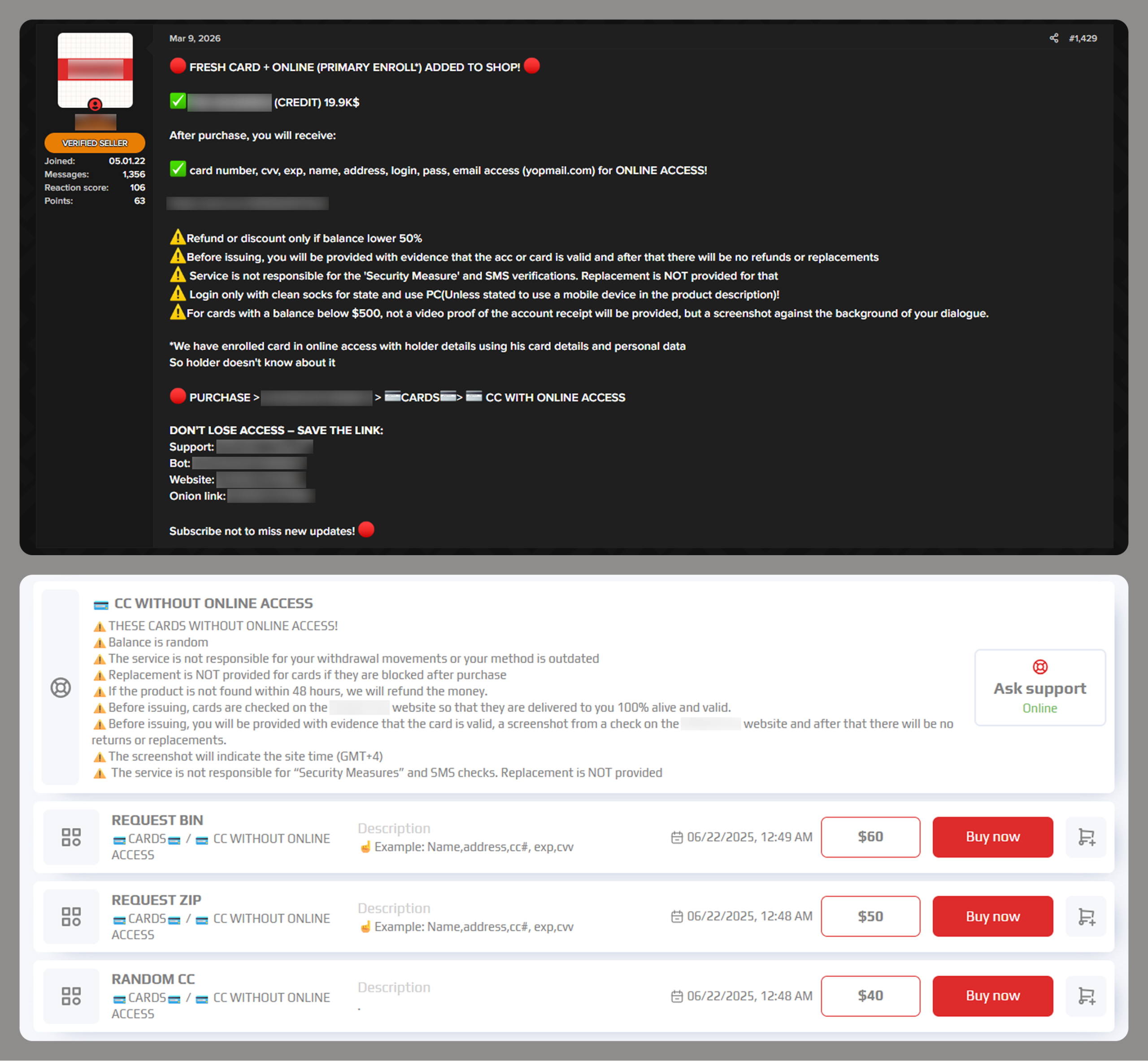
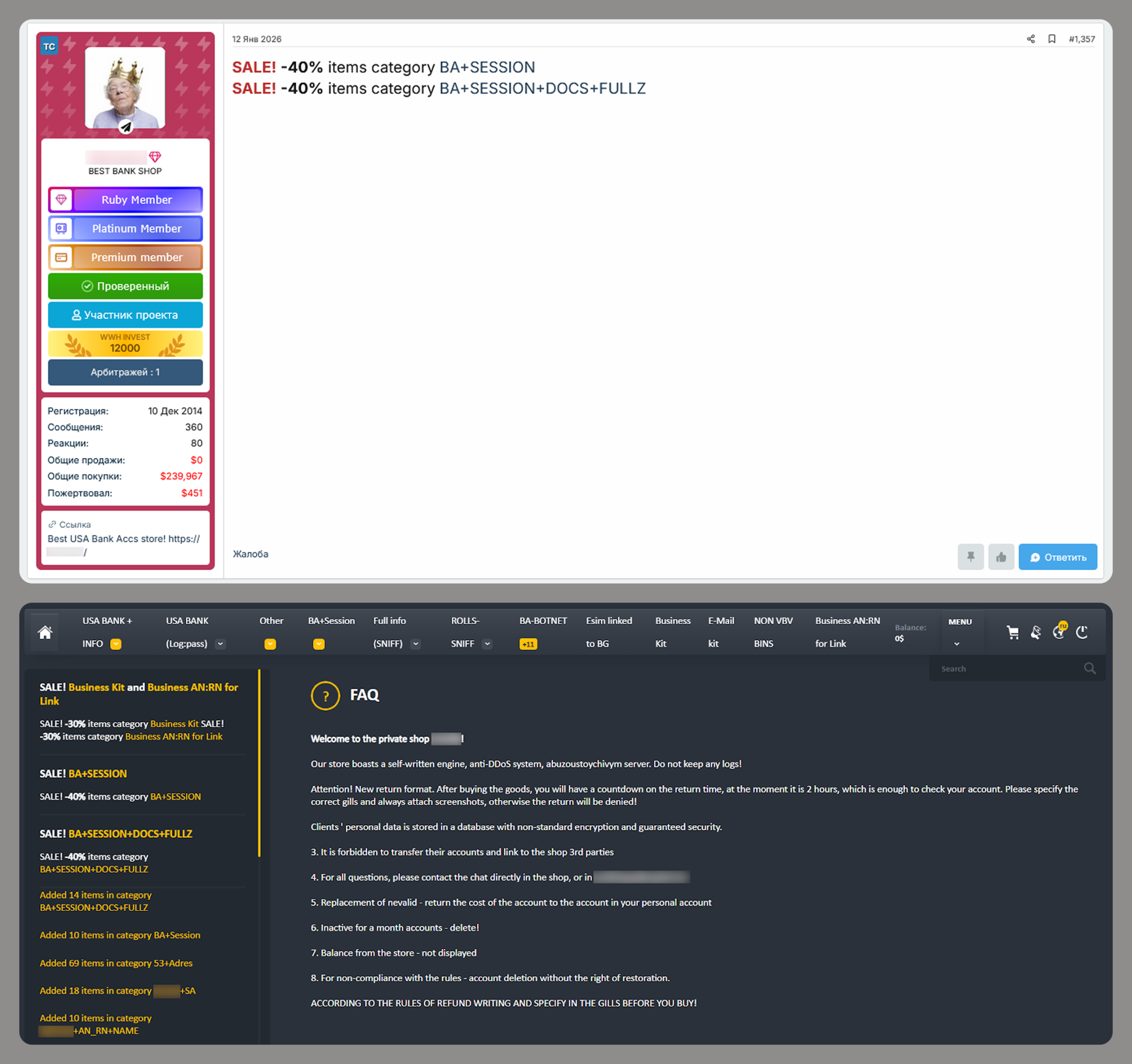
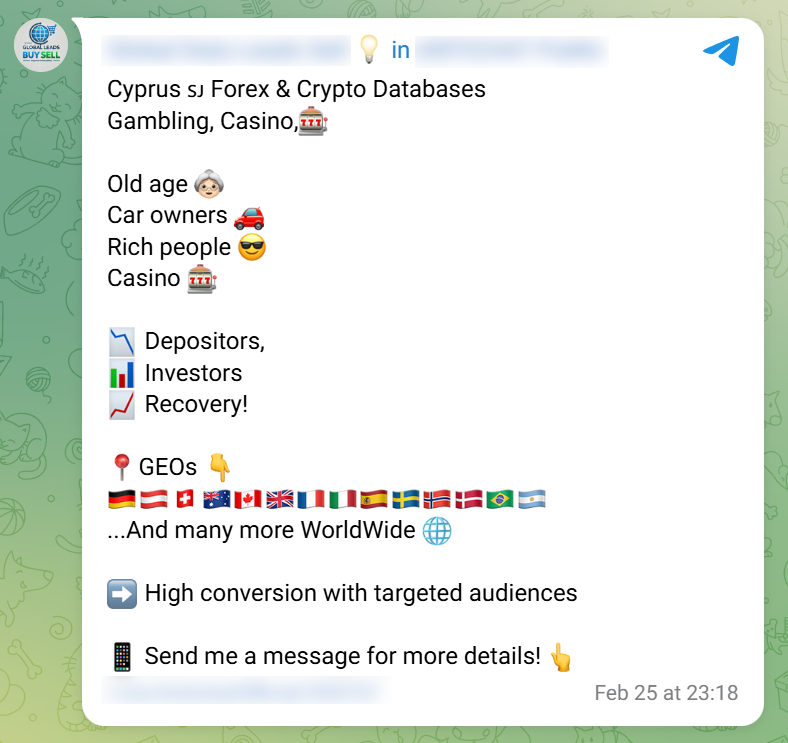
Infostealers stole the show, with RedLine, Raccoon, and Vidar dumping millions of logins yearly. Dark web markets traded 15 million compromised cards in 2025, alongside full profiles—bank logins averaged $50, premium cards $110. Kaspersky tracked 2.3 million financial data listings, up 30% from 2024, including bundled “fullz” (name, SSN, cards) for identity theft rings.
Compiled databases sold cheap—$200 for 100k logins—enable automated checkers that test creds across 1000+ sites. Phishing kits now auto-generate from these dumps, closing the loop. Breached banks like those in recent LatAm hacks fed this beast, with 500k+ accounts listed post-incident.
Outlook for 2026? Expect AI-sharpened phishing (voice clones, deepfake alerts) and mobile-first infostealers targeting passkeys. Dark web prices may dip further on oversupply, but volume rises—projected $10B+ in global fraud losses. Defenses: Hardware 2FA everywhere, unique passphrases via managers, and monitor dark web alerts. Banks must segment accounts; users, ditch SMS codes. Kaspersky’s data proves detection lags creation—proactive hygiene beats reaction every time.
This isn’t hype; it’s the data-driven shift to credential economies. Ignore it, and 2026 drains hit harder.