Core Vulnerability
Payload CMS, the Node.js-based headless CMS, ships with a serious flaw in its built-in password recovery flow. Versions below 3.79.1 expose auth-enabled collections to unauthenticated attacks. If a user triggers a “forgot password” request, an attacker can intercept and manipulate the recovery endpoint to perform arbitrary actions on that user’s behalf—no login required.
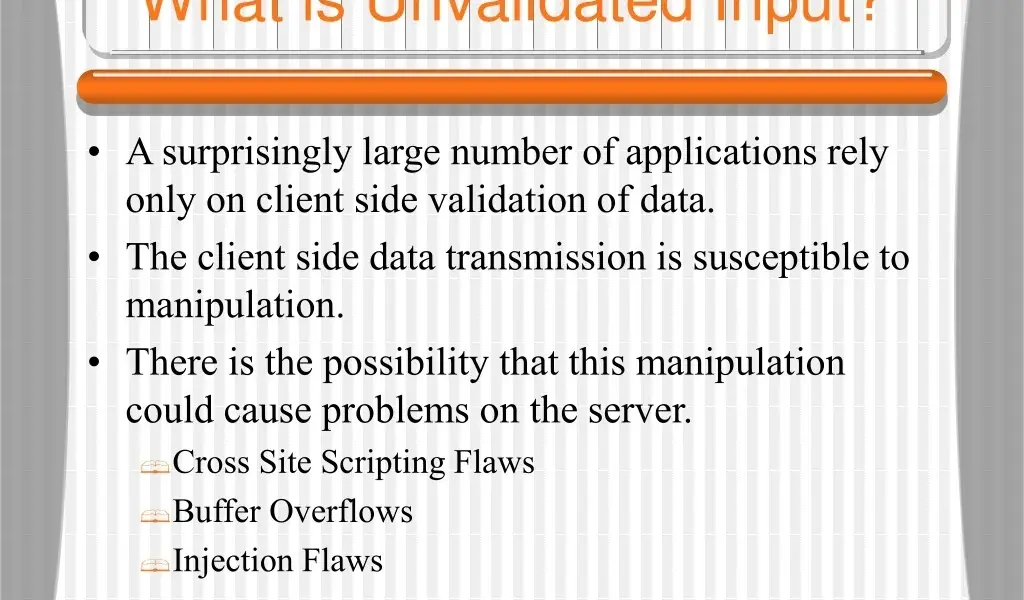
This isn’t theoretical. The issue stems from unvalidated input in the recovery endpoints, specifically around URL construction and token handling in the @payloadcms/graphql module. Attackers exploit it post-reset initiation, potentially updating profiles, changing emails, or worse, depending on collection permissions. Payload disclosed this on their security advisory page, urging immediate upgrades.
Affected Users and Scope
Anyone running Payload < 3.79.1 with auth collections using the default forgot-password feature qualifies as vulnerable. That’s a wide net: Payload powers thousands of sites, from indie projects to enterprise apps, thanks to its GraphQL API and easy auth setup.
Consider the numbers. Payload hit version 3.0 in early 2024, with steady adoption—over 10,000 GitHub stars and active npm downloads exceeding 100,000 weekly pre-patch. If your stack includes auth collections (users, admins, customers), assume exposure. No evidence of widespread exploits yet, but reset flows see heavy traffic; attackers scan for these routinely.
Why target this? Password resets bypass normal auth. A user clicks “forgot password” via phishing email or legit need, generating a token emailed out. Without input sanitization, attackers craft malicious payloads via query params or headers, hijacking the token before the user acts. It’s account takeover lite—limited to reset window, but enough for data theft or pivots.
Patch and Immediate Actions
Payload fixed it in 3.79.1, released swiftly after discovery. They hardened input validation and URL building in the recovery chain. Upgrade now: npm update @payloadcms/graphql or pin to ^3.79.1. Test in staging—Payload’s schema migrations are usually seamless, but auth tweaks demand verification.
No full workarounds exist. Partial mitigations like rate-limiting resets or custom endpoints fall short against unauthenticated access. If pinned to an old version, audit logs for suspicious recovery POSTs to /api/[collection]/forgot-password. Monitor for anomalous GraphQL mutations post-reset.
npm install @payloadcms/graphql@^3.79.1
# Restart server, verify auth flow
curl -X POST http://localhost:3000/api/users/forgot-password \
-H "Content-Type: application/json" \
-d '{"email": "test@example.com"}'
Post-upgrade, regenerate all active reset tokens if paranoid—though Payload doesn’t require it.
Why This Matters: Broader Risks
Password recovery vulns recur because devs prioritize UX over edge-case security. Open redirects, token leaks, and param injection plague similar flows in Supabase, Strapi, and even Firebase Auth historically. Payload’s sin? Assuming GraphQL resolvers sanitized frontend inputs. They didn’t.
Implications hit hard for self-hosted CMS users. Unlike SaaS, you own the exposure. A single compromised admin account cascades: attackers escalate via collection access controls. In finance/crypto apps—Payload’s bread-and-butter— this means wallet drains or API key grabs.
Skeptical take: Payload’s team patched fast, transparently labeling it “critical.” No zero-day reports, and the fix is surgical. But it exposes reliance on “batteries-included” auth. Custom flows or libraries like Lucia/NextAuth might dodge this, at complexity cost. Always validate: fuzz endpoints with tools like ffuf or Burp Suite.
Lesson? Audit third-party auth religiously. Weekly scans via Nuclei templates or Dependabot catch these. For Njalla users: if Payload’s in your stack, patch yesterday. Security isn’t set-it-forget-it—it’s constant triage.