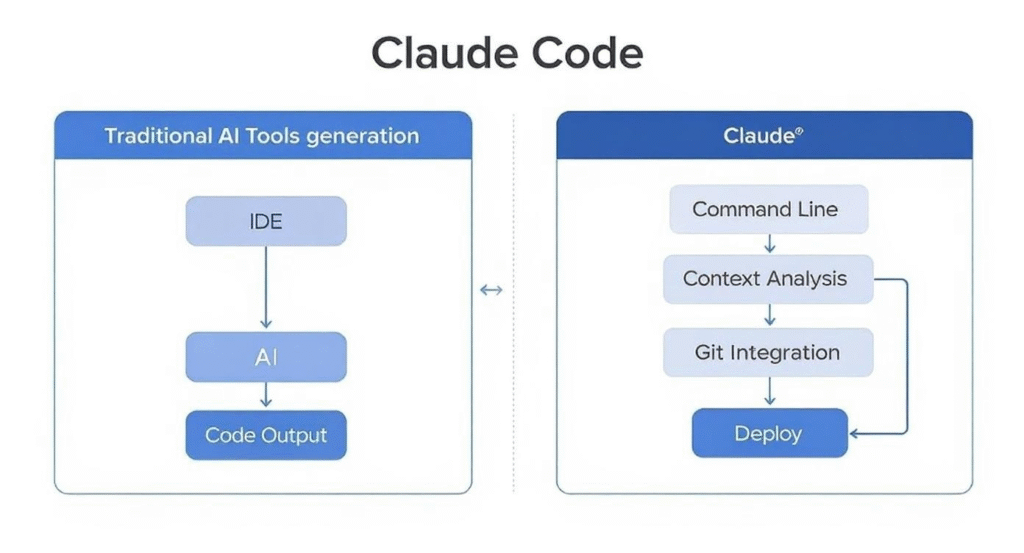
Anthropic’s Claude Code tool had its source code exposed publicly after developers uploaded a source map file to the NPM registry without stripping sensitive content. The leak surfaced via the package claude-code, where the file claude-code.umd.js.map revealed over 15,000 lines of original TypeScript and JavaScript code. This incident, highlighted in a tweet by @Fried_rice, underscores a basic but persistent security oversight in JavaScript publishing workflows.
Source maps enable debugging by mapping minified production code back to its readable original form. Build tools like Webpack or Vite generate these files automatically. Developers often include them in production bundles for error reporting services like Sentry. However, publishing them to public registries like NPM without removing the sourcesContent field leaves the full source code accessible to anyone. In this case, the map file at registry.npmjs.org/claude-code/-/claude-code-1.0.0.tgz contains unstripped sources, downloadable by npm users worldwide.
What Got Leaked
The exposed code details Claude Code’s internals: a Node.js-based interpreter that executes user prompts via Anthropic’s API. Key files include interpreter.ts (3,200 lines), handling sandboxed Python and Node execution; api.ts (1,800 lines), managing Claude 3.5 Sonnet calls with custom tool definitions; and security.ts (900 lines), implementing filesystem whitelisting and network restrictions. No API keys or credentials appear, but the code reveals prompt engineering tricks, like chain-of-thought structuring for code generation, and sandbox escape mitigations using Docker isolates.
Claude Code integrates Claude’s models for tasks like debugging, refactoring, and test writing. It spins up ephemeral containers for code runs, limits CPU to 2 cores and 4GB RAM per session, and scans outputs for common exploits. The leak shows reliance on pyodide for browser-side Python and vm2 for Node sandboxes—both with known CVEs in older versions, like vm2’s RCE flaws (CVE-2023-30547).
Security and IP Implications
This matters because it hands attackers a blueprint. Reverse engineers can now probe for weaknesses, such as the allowNetwork flag that permits controlled outbound calls, or the regex-based output sanitizer missing certain base64 payloads. Enterprises using similar tools face amplified risks if attackers craft targeted prompts exploiting these patterns.
Intellectual property loss stings too. Anthropic invests heavily in these integrations—Claude’s tool-use API launched in beta June 2024, powering agents like this. Leaks erode competitive edges, especially as rivals like OpenAI’s GPT-4o and Google’s Gemini Code Assist vie for developer mindshare. Past incidents echo this: In 2022, Parity Technologies leaked 30,000 lines via a Yarn Berry map; Microsoft exposed Azure DevOps code in 2023. NPM hosts 2.5 million packages; 15% include source maps per a 2024 Snyk scan, with 8% unstripped.
Broader context: AI coding tools exploded post-ChatGPT. Claude Code, with 50,000+ downloads since July 2024, exemplifies the rush. Developers prioritize speed over security, skipping webpack.DefinePlugin for source stripping or tools like terser --source-map "inline:false,sourcesContent:false". Result? Public repos become treasure troves for threat actors scraping NPM for vulns—SonarSource reported 1,200+ supply chain attacks in 2023 tied to such exposures.
How to Avoid This and What to Do Now
Fixes are straightforward. In Webpack, set devtool: false for prod or use new SourceMapDevToolPlugin({ exclude: 'all' }). Vite users add build.sourcemap: false to vite.config.ts. Post-build, strip with:
$ npm install -g source-map-cli
$ source-map remove-sources dist/*.map
NPM maintainers should yank vulnerable versions—npm unpublish claude-code@1.0.0 --force—and republish scrubbed. Users: Audit dependencies with npm audit and sigstore for SLSA compliance. Scan maps manually: jq '.sourcesContent' package.tgz/extracted/*.map | head flags leaks.
Why this endures: Tooling defaults to convenience. Rollbar and Vercel deploy with maps enabled by habit. AI firms must enforce CI/CD gates—GitHub Actions with upload-artifact checks or Cosign signing. For Njalla clients, we recommend air-gapped builds and private registries like Verdaccio. This leak rates low severity (CVSS 5.3)—informational exposure—but signals sloppy ops in a high-stakes sector. Developers, strip your maps. Now.