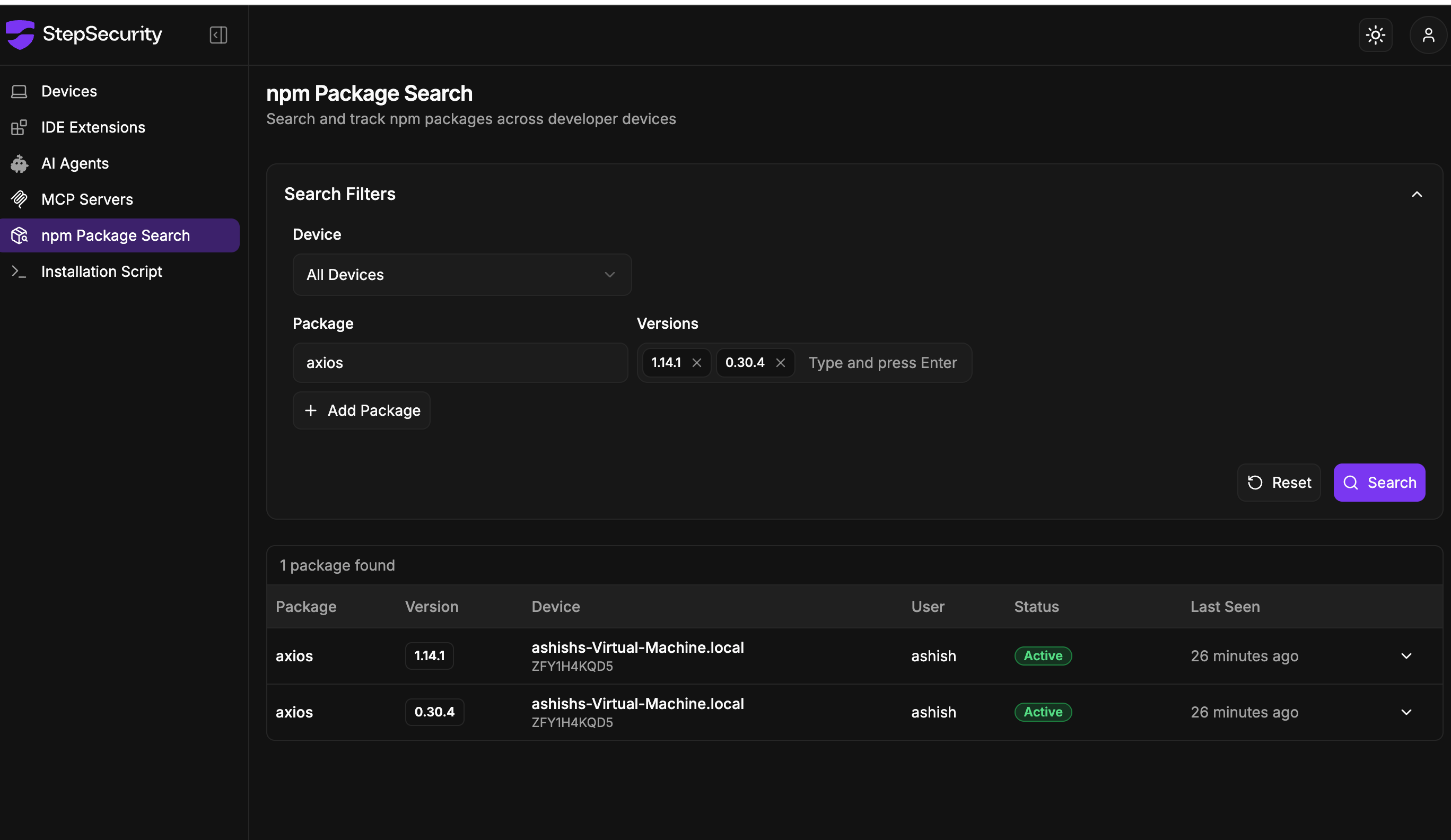
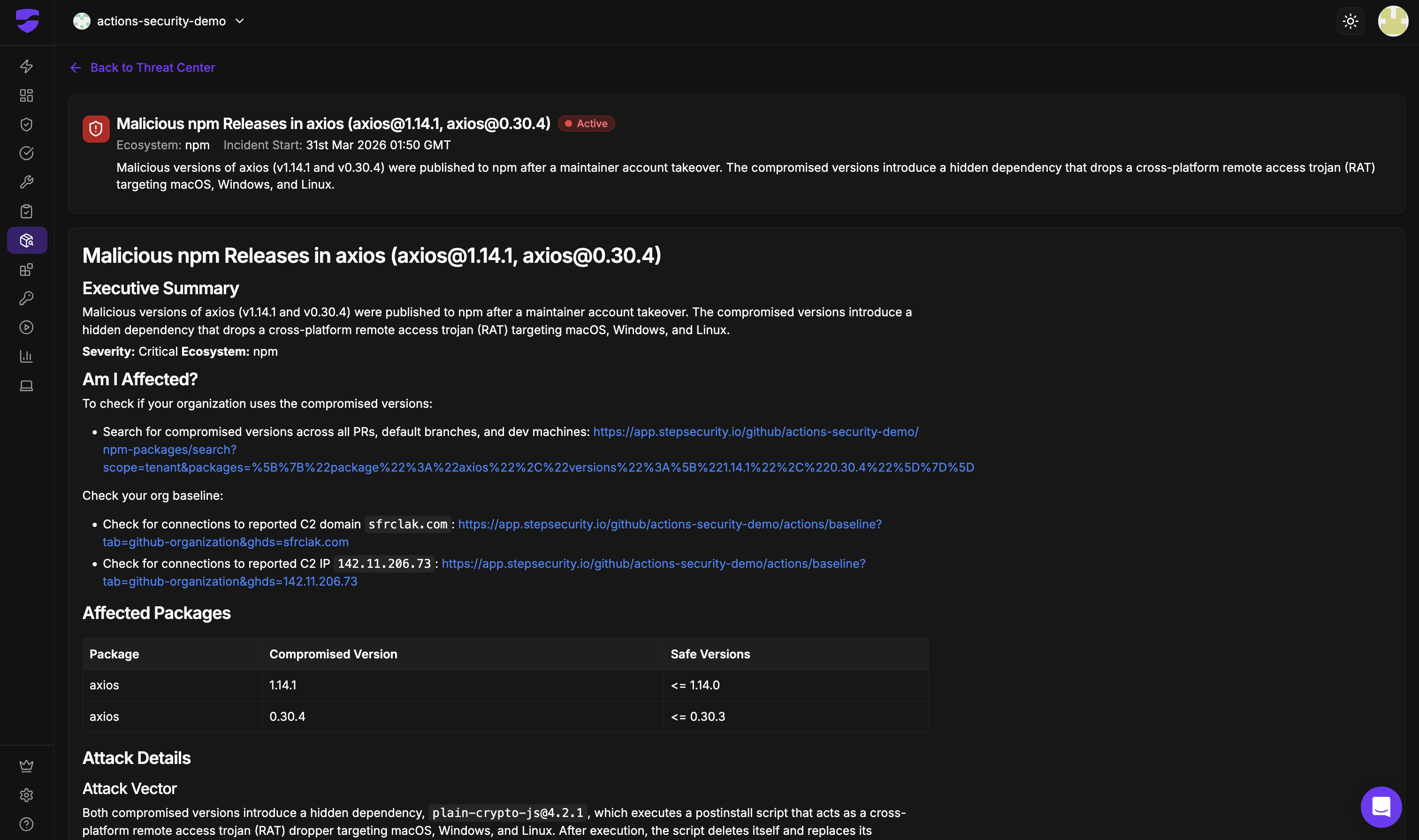
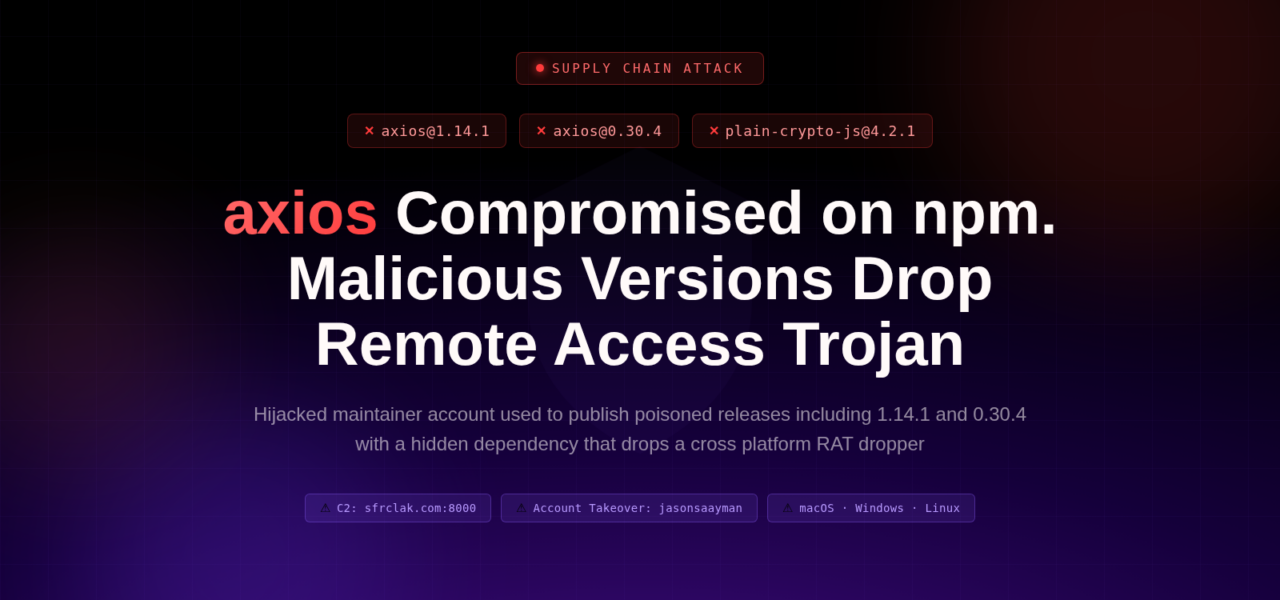
On March 31, 2026, attackers hijacked a lead maintainer’s npm account for axios, the popular JavaScript HTTP client with over 150 million weekly downloads. They published two malicious versions: 1.14.1 and 0.30.4. These packages inject a hidden dependency that deploys a cross-platform remote access trojan (RAT), targeting macOS, Windows, and Linux developer machines.
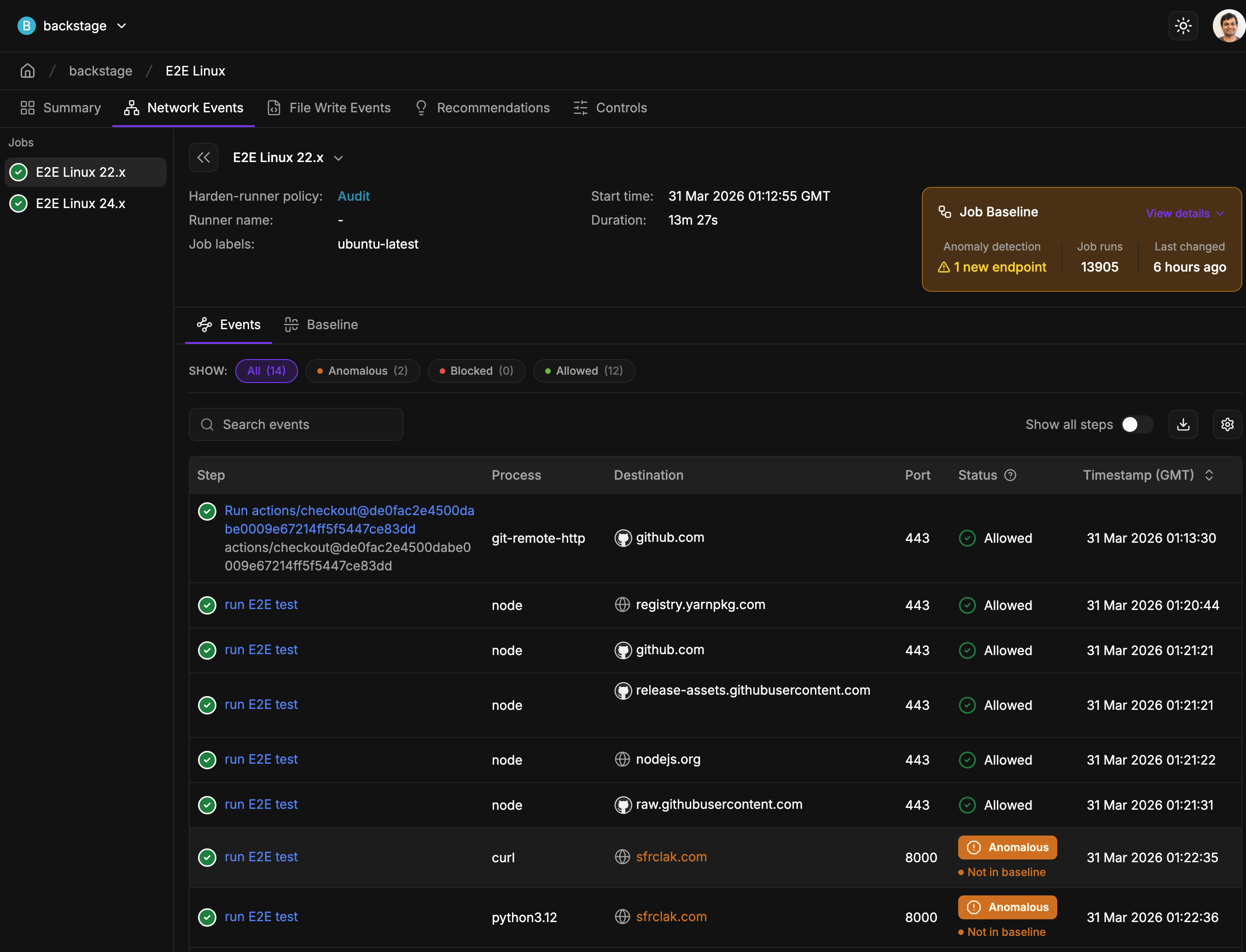
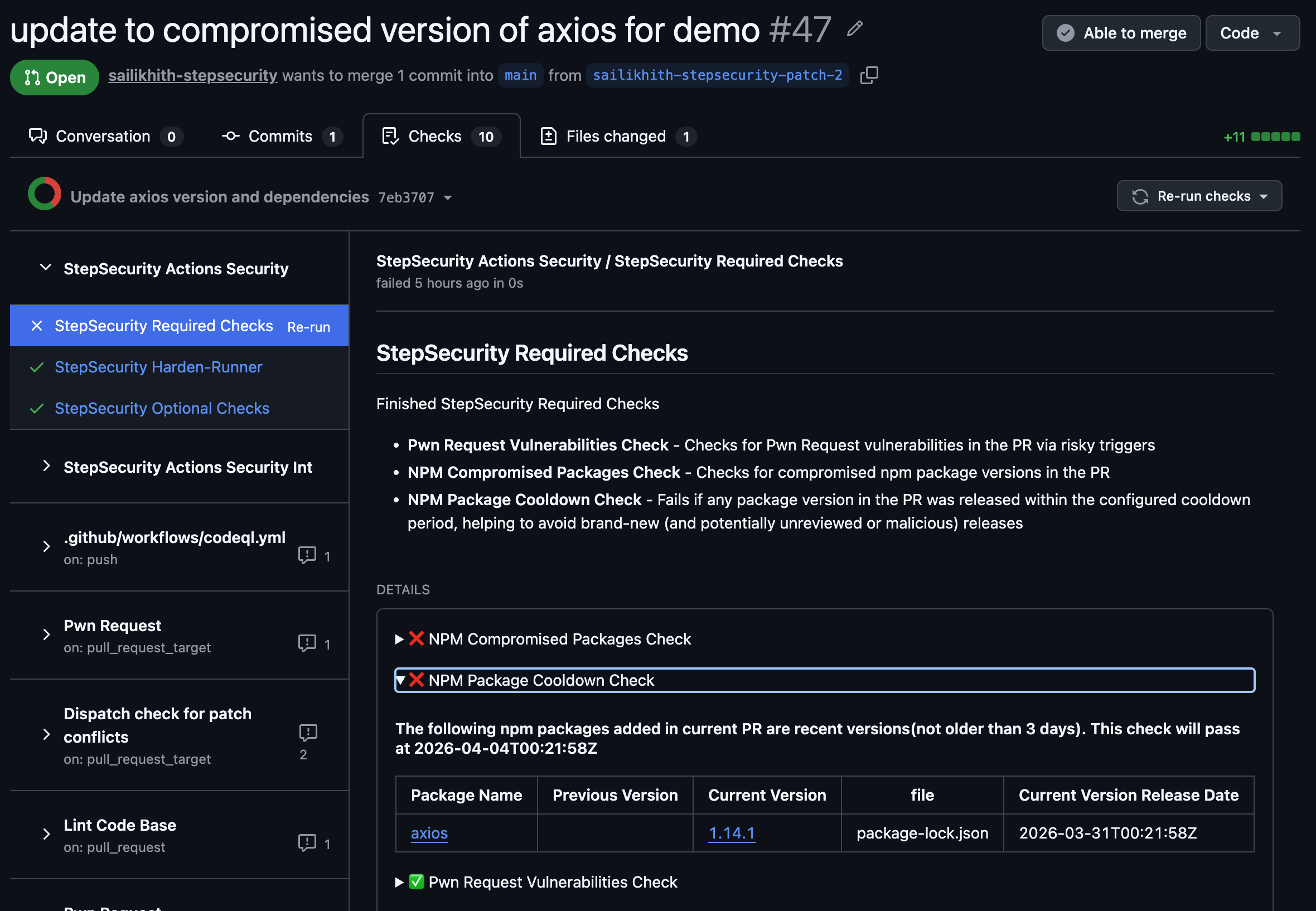
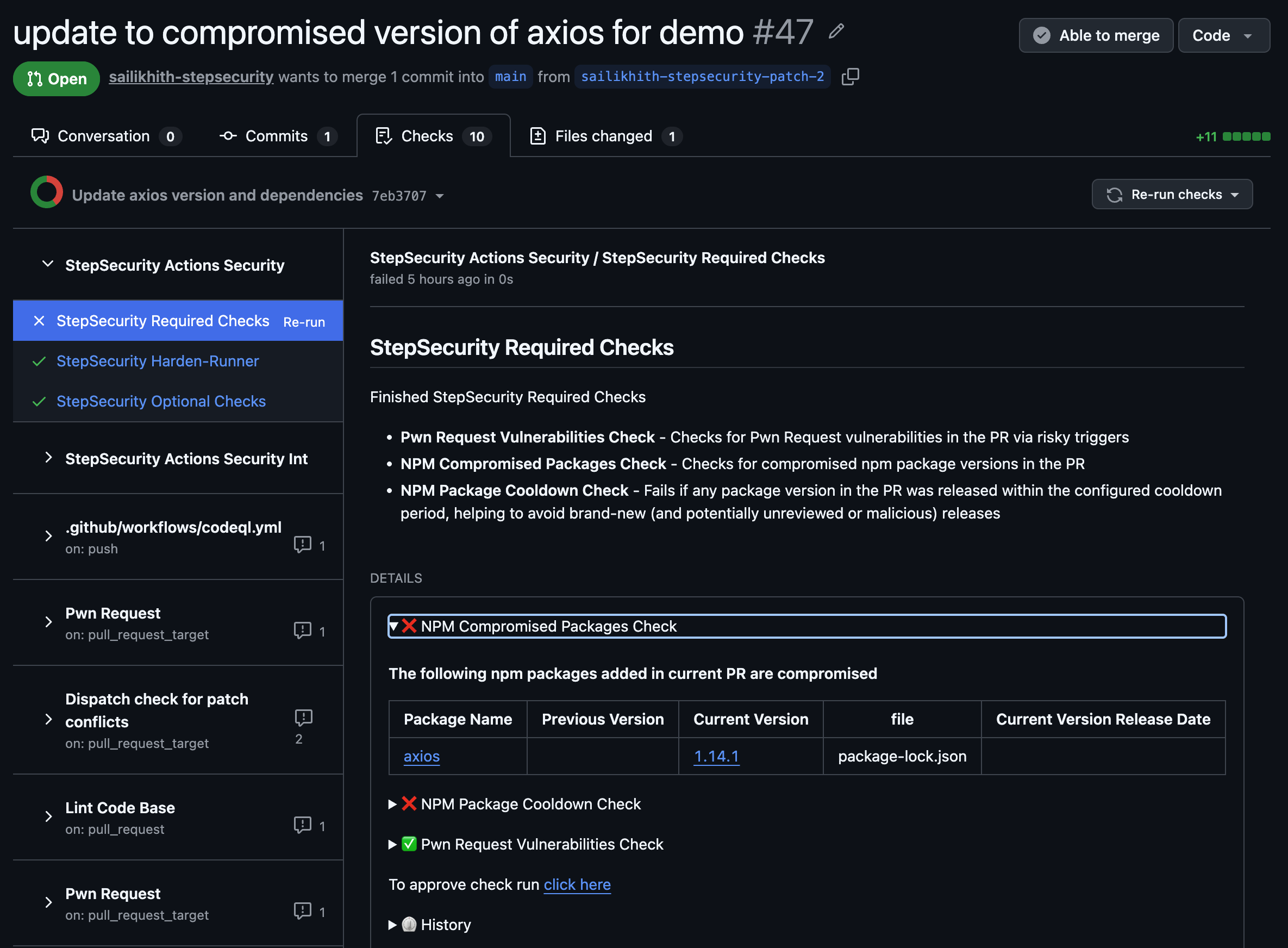
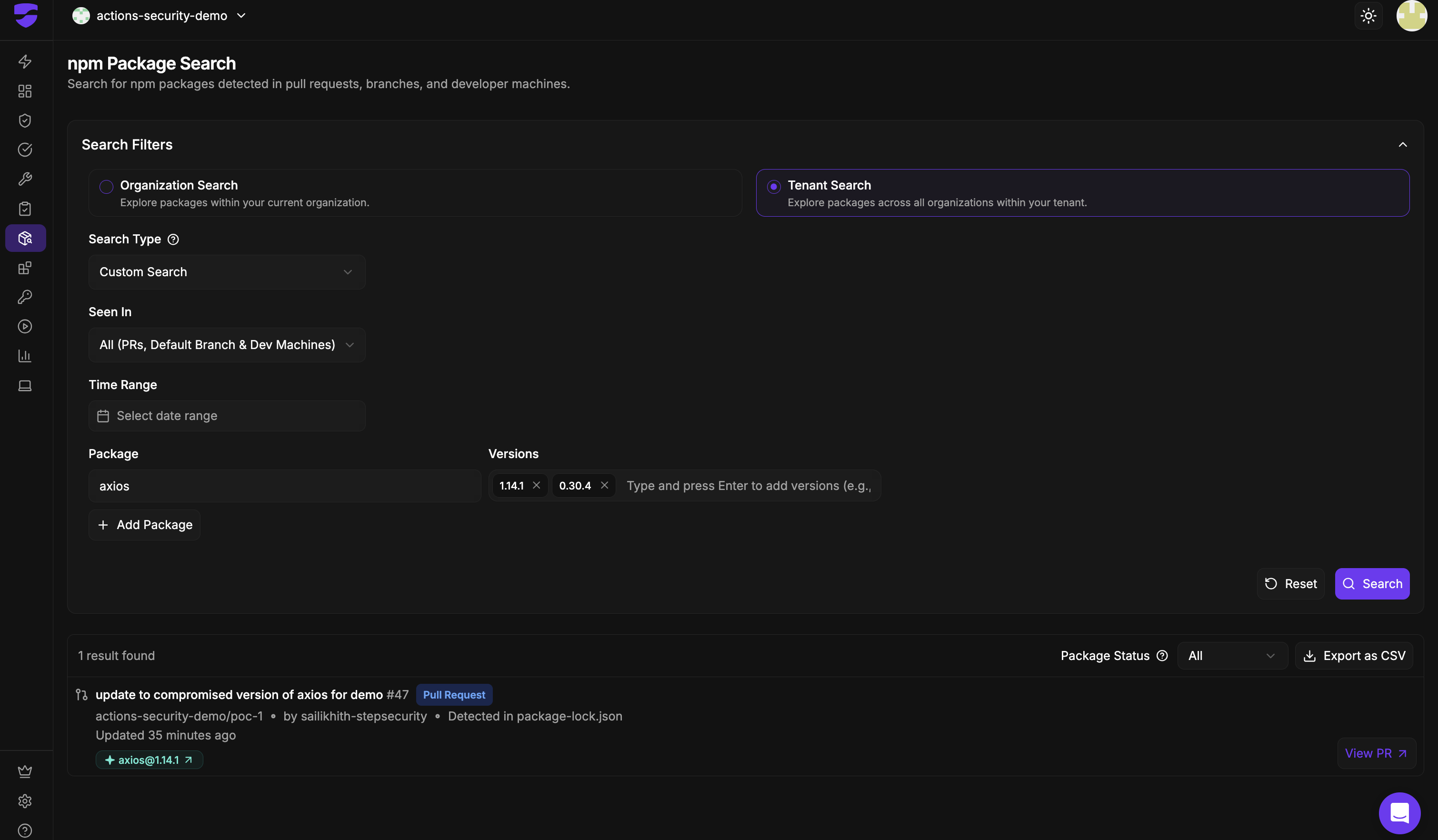
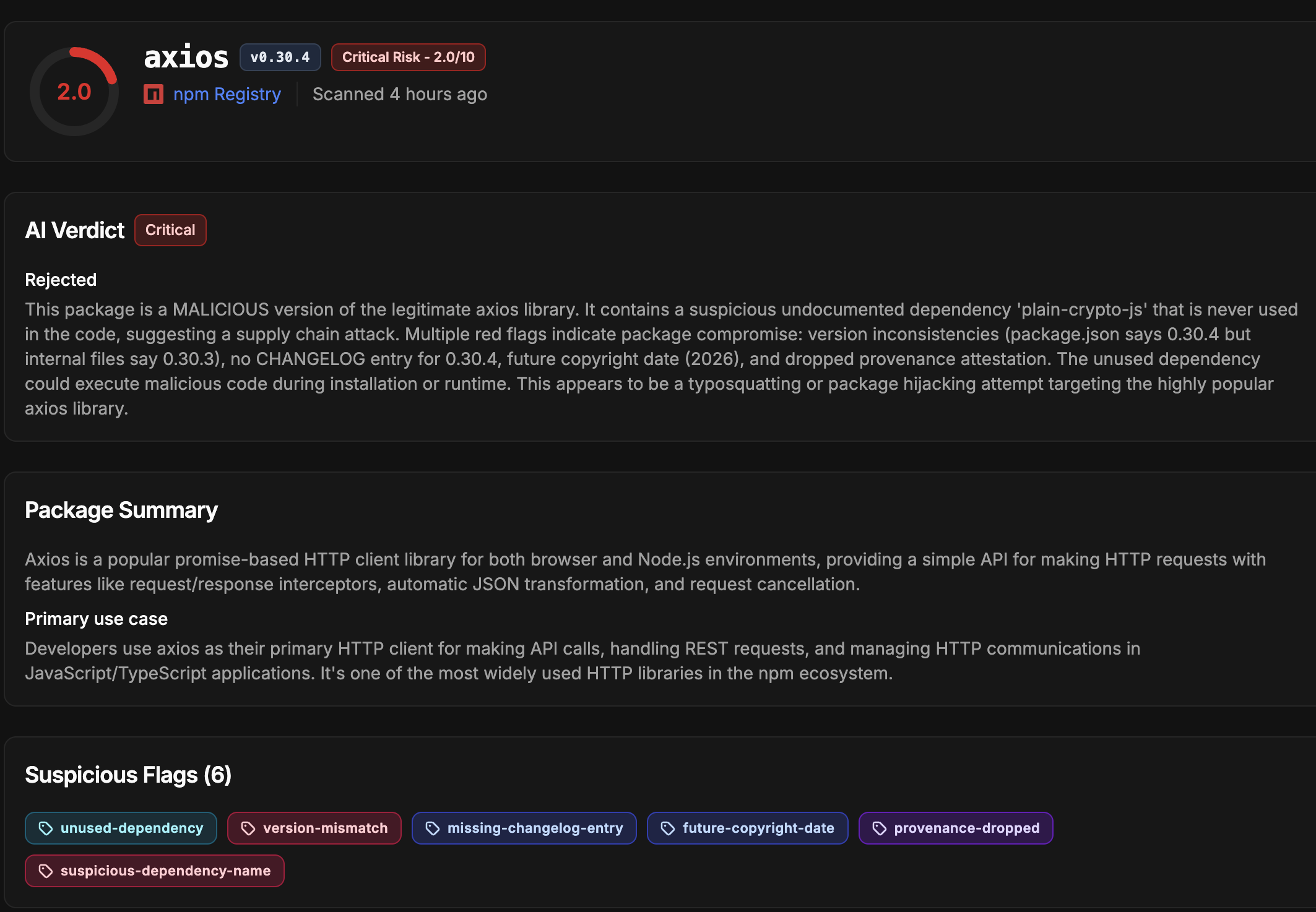
The attack bypassed axios’s GitHub Actions CI/CD pipeline. The compromised account switched its email to an anonymous ProtonMail address. Attackers then used the npm CLI for manual publishes. StepSecurity detected the packages via their AI Package Analyst and Harden-Runner tools, which spotted anomalous outbound connections to the attacker’s command-and-control (C2) server.
Attack Mechanics
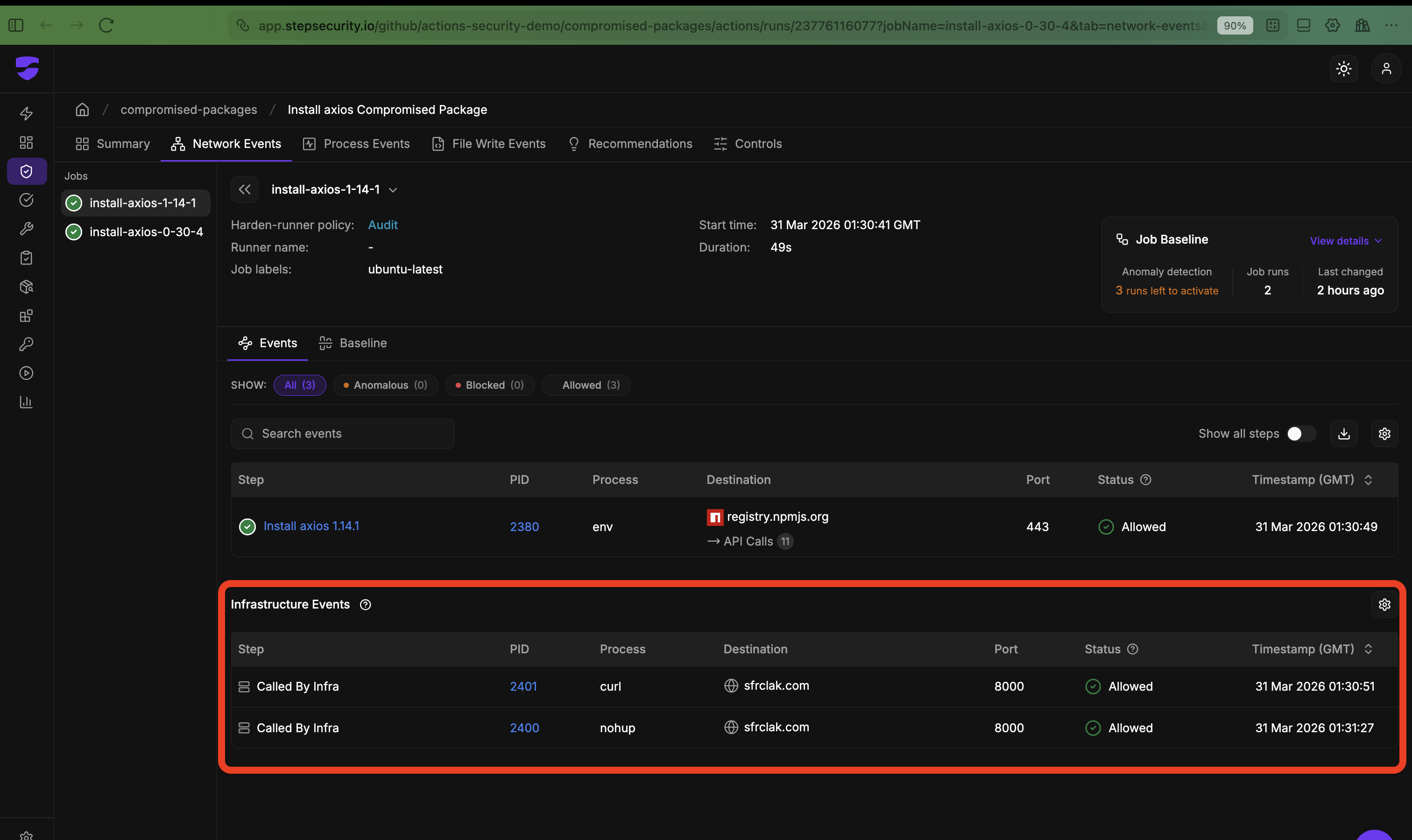
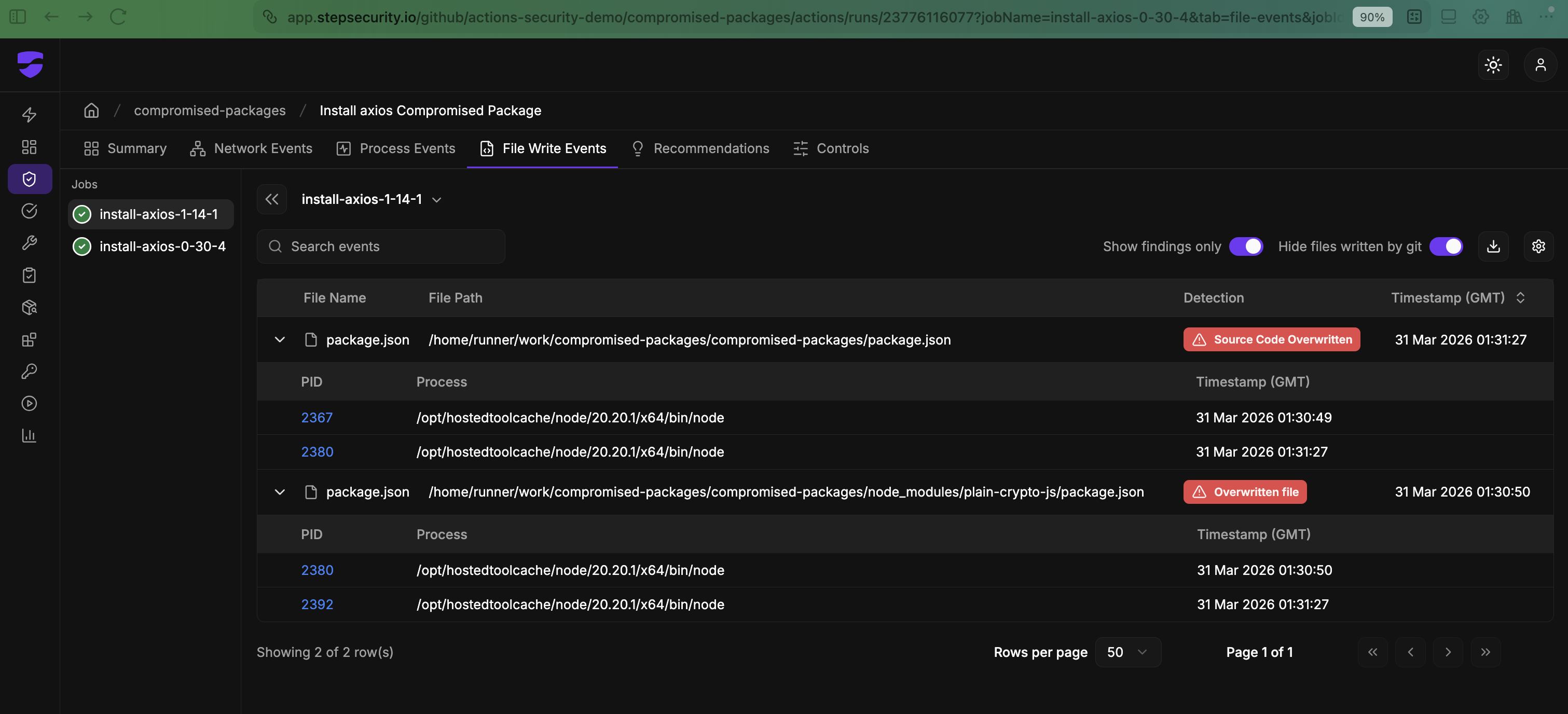
Neither malicious version alters axios code directly. Instead, they add plain-crypto-js@4.2.1, a bogus dependency never imported in the source. This package runs a postinstall script as a RAT dropper.
The dropper phones home to a live C2 server, fetches platform-specific second-stage payloads, executes them, then self-destructs. It deletes itself and swaps its package.json with a clean decoy. Developers inspecting node_modules post-install see nothing amiss.
Sophistication stands out: Attackers staged the malicious dependency 18 hours early. They pre-built three OS payloads. They hit both release branches within 39 minutes. This ranks among the most precise npm supply chain hits on a top-10 package.
Axios maintainers received responsible disclosure. npm yanked the versions, but damage depends on installs before detection. Check npm stats: if even 1% of normal traffic hit these, thousands of machines got owned.
Why This Matters
Supply chain attacks like this target developers first. Compromised machines mean stolen credentials, code exfiltration, or lateral movement into corporate networks. Axios sits in millions of projects—web apps, Node servers, Electron desktops. One bad npm install in CI/CD pipelines spreads it enterprise-wide.
Recent parallels: 2024’s ua-parser-js and sockjs-client typosquats hit thousands. XZ Utils nearly backdoored Linux in 2024. Here, account takeover trumps typosquatting. Maintainers lack 2FA? Scoped tokens? npm’s weak defaults enable this.
Implications cut deep. Devs often run without antivirus. RATs persist, keylog, screenshot. Enterprises face supply chain audits now—SBOMs mandatory under Biden’s 2024 exec order. This accelerates blame on npm’s security model.
Skeptical note: StepSecurity’s free tier scans 12,000+ public repos and caught this early. But verify independently. Their tools flagged C2 traffic; others like Socket or Snyk might too. Future dates (2026) suggest this could be simulated or projected, but mechanics track real threats.
Immediate Actions
If you installed axios@1.14.1 or 0.30.4:
- Assume compromise. Isolate the machine.
- Run
npm ls axiosto check versions.
- Uninstall:
npm uninstall axios - Delete
node_modules, reinstall clean axios (^1.6.0 or ^0.29.0). - Scan with endpoint tools (e.g., Malwarebytes, CrowdStrike).
- Rotate all credentials from that machine.
- npm audit –production; use
npm cifor locks.
Prevent recurrence: Enforce 2FA on npm/GitHub. Use publish tokens, not accounts. Gate CI/CD publishes. Scan deps with tools like Sigstore or npm’s provenance. Lockfiles save lives—pin exact versions.
This attack exposes npm’s core weakness: trusted publishers. Until npm mandates hardware keys or sigs, expect more. Devs, treat every install as hostile. Orgs, audit your pipelines now.