Microsoft’s Defender team spotted a phishing campaign that hijacks the OAuth Device Code Authentication flow to steal organizational accounts. Attackers generate fresh device codes on demand, dodging the standard 15-minute expiration window through scripted automation. They pair this with AI-tuned infrastructure for scale, targeting Microsoft Entra ID tenants.
This matters because it neuters multi-factor authentication (MFA) without stealing credentials. Users think they’re verifying their own login, but they hand attackers a live authorization token. Once granted, attackers control the victim’s session indefinitely. Recon starts 10-15 days early: bots probe target emails to confirm active accounts in the tenant. Only live targets get hit.
Step-by-Step Exploitation
Delivery kicks off with emails slipping past gateways. Lures mimic HR docs, e-sign requests, or voicemail alerts. Links or attachments lead to attacker-controlled pages on compromised legit domains or serverless hosts like Azure Functions—stuff that evades URL scanners and sandboxes.
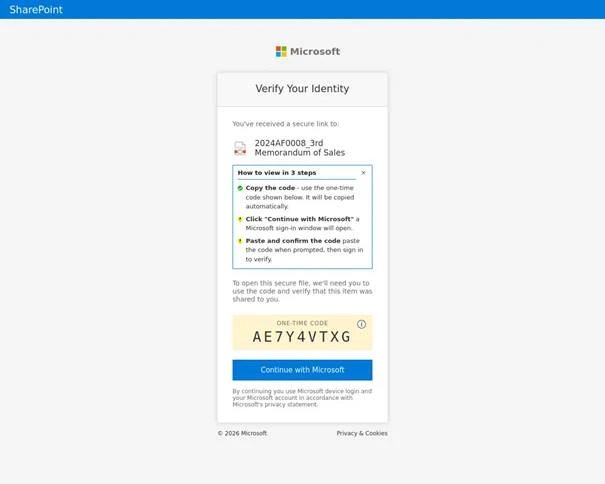
Clicking triggers a “browser-in-the-browser” iframe or blurred doc preview. A “Verify identity” button pops a device code. Behind the scenes, JavaScript hits Microsoft’s identity platform, fetches a valid code valid for 15 minutes, and copies it to your clipboard. You paste it into what looks like the real Microsoft login page.
But it’s the attacker’s tab authenticating. No MFA prompt hits your device because the flow decouples verification from the origin. User grants consent, attacker gets tokens. Campaign rotates payloads: some preload emails for code gen, others use domain shadowing or fake subdomains like “login-microsoft-support[.]com”.
Automation is key. Scripts handle code polling—OAuth device flows let attackers poll for user input every few seconds. If no completion in 15 minutes, it expires, but fresh generation per victim keeps it live. Microsoft notes end-to-end tooling, likely AI for lure crafting or domain selection, though details stay vague.
Why It Scales and Sticks
OAuth 2.0 Device Authorization Grant (RFC 8628) suits smart TVs or IoT: device shows URI/code, user auths elsewhere. Legit, but ripe for abuse since 2022 reports. Attackers scaled it here with recon and evasion. Compromised infra means high rep scores; serverless hides payloads.
Implications hit enterprises hard. Entra ID admins see “legit” device logins from odd user agents. Tokens enable full access: email, SharePoint, Teams. Finance/crypto firms? Direct path to wire transfers or wallet drains if synced. We’ve seen similar in Magecart token thefts, but this automates at org scale.
Skeptical note: “AI-enabled” smells hyped. Microsoft’s report stresses automation; AI likely just optimizes phishing kits, common now via tools like WormGPT. Real edge is the flow abuse, not sci-fi bots.
Hardening Up
Block it. Entra ID Conditional Access: restrict device code flow to trusted IPs/devices. Monitor sign-ins for “device code” auth method—flag anomalies like bulk from one IP. Audit consent prompts; revoke broad scopes.
Endpoint: Train on clipboard tricks—check before pasting. Deploy anti-phishing browser extensions spotting iframes. Email filters: hunt domain shadows via passive DNS. Tools like Microsoft Defender for Office 365 catch some, but test yours.
Broader fix: Push OAuth providers for shorter polls or CAPTCHAs on device codes. Users, verify domains manually. Orgs, segment tenants—limit blast radius. This campaign proves MFA alone fails; layer defenses. Ignore it, and your tenant becomes a token farm.