Attackers exploited a zero-day vulnerability in Adobe Acrobat Reader for at least five months, from November 2025 through March 2026, before researcher Haifei Li uncovered it. Li, co-creator of the EXPMON sandbox for detecting file-based exploits, spotted the issue when someone submitted a PDF named yummy_adobe_exploit_uwu.pdf to EXPMON on March 26, 2026. A variant appeared on VirusTotal as early as November 28, 2025. Adobe knows about it—Li reported it—but hasn’t released a patch as of April 9, 2026.
This matters because Acrobat Reader processes PDFs everywhere: emails, drives, browsers. A single untrusted file can fingerprint your system and pull in worse payloads. Exploitation windows like this—over 150 days—let attackers compromise high-value targets quietly. Enterprises in energy, government, and infrastructure face the highest risk here, based on the decoy content.
Exploit Mechanics
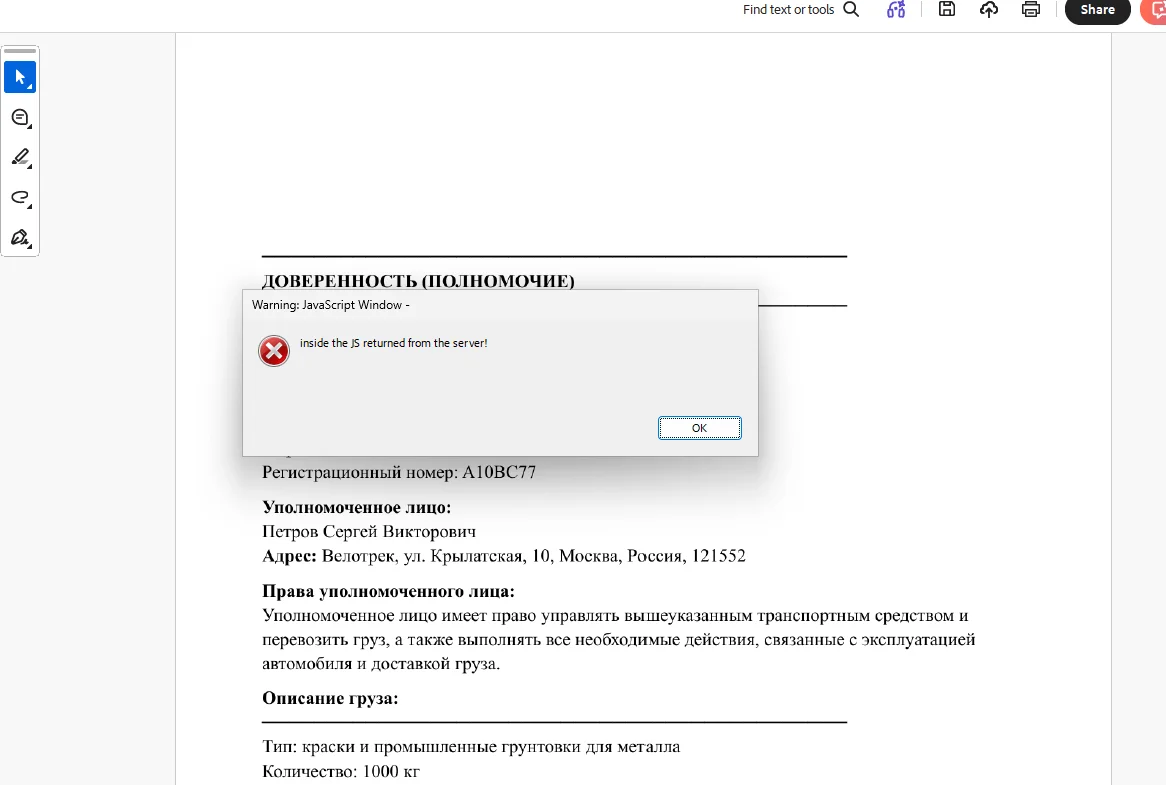
The PDF embeds obfuscated JavaScript that triggers on open. It grabs specifics: OS version, language settings, Acrobat Reader version, and the file’s local path. This data beams to attacker servers at 169.40.2[.]68 and 188.214.34[.]20. The script then fetches and runs additional exploits from those servers, potentially escalating to remote code execution or sandbox escapes.
Li tested it; the servers didn’t deliver payloads to him, likely due to IP blocking or unmet fingerprint checks. Giuseppe Massaro, another researcher, confirmed the PDFs show Russian-language images mimicking gas supply disruption alerts—classic spear-phishing lures for critical infrastructure.
Acrobat Reader’s JavaScript engine has a long history of zero-days. CVEs like CVE-2018-4990 and CVE-2023-26369 prove PDFs remain a prime attack vector. Attackers favor them for cross-platform reach—no downloads needed, just a click. EXPMON caught this via behavioral analysis, detonating the file in a controlled environment to flag anomalies like outbound connections.
Targeting and Geopolitical Angle
The Russian-themed decoys point to speakers in government, energy, or utilities. Content details emergency responses to gas disruptions, suggesting nation-state or cybercrime ops amid Russia’s ongoing conflicts. Think Ukraine war fallout: infrastructure attacks spiked 30% in 2024 per Mandiant reports.
No public attribution yet, but the sophistication—obfuscation, conditional payloads—screams advanced persistent threat (APT). Long dwell time implies targeted delivery, not mass sprays. If you’re in those sectors, assume your PDFs from “official” sources could be weaponized.
This echoes past PDF campaigns, like the 2020 SolarWinds follow-ons using docs for lateral movement. Why it persists: PDFs bypass many email filters; Reader’s ubiquity (500 million+ installs) amplifies reach. Attackers bet on patch delays—Adobe averages 30-60 days for critical fixes, per its advisories.
Mitigations Now
Patch lag forces workarounds. Block those IPs: 169.40.2.68 and 188.214.34.20. Better, filter HTTP/HTTPS traffic with “Adobe Synchronizer” in the User-Agent header—that’s the callback signature.
# Example firewall rule (iptables)
iptables -A OUTPUT -d 169.40.2.68 -j DROP
iptables -A OUTPUT -d 188.214.34.20 -j DROP
Disable JavaScript in Reader: Edit > Preferences > JavaScript > uncheck “Enable Acrobat JavaScript.” Use Protected Mode (enabled by default in Reader DC). Scan PDFs with tools like EXPMON or VirusTotal before opening. Train users: no unsolicited PDFs, period.
For enterprises, deploy endpoint detection that watches Reader processes for unusual network or child processes. Tools like CrowdStrike or Microsoft Defender flag this. Convert PDFs to images or use sandbox viewers like PDF.js in browsers.
Bottom line: Five months of silent exploitation shows why zero-days kill. Adobe’s delay—despite notification—exposes users unnecessarily. Assume compromise if you opened Russian-themed PDFs since November. Inventory systems, hunt for C2 callbacks. Fileless attacks like this evade AV; behavioral defenses win. Stay vigilant—PDFs aren’t safe anymore.