Kaspersky researchers uncovered CrystalX RAT in March 2026, actively sold as malware-as-a-service (MaaS) on private Telegram channels. This Windows 64-bit trojan combines standard remote access trojan (RAT) functions with data stealers, keyloggers, clipboard hijackers (clippers), spyware, and a suite of prank commands designed to harass victims. Attackers buy access to a web panel with tiered subscriptions, lowering the barrier for low-skill operators to deploy it. Kaspersky detects it as Backdoor.Win64.CrystalX.*, Trojan.Win64.Agent.*, and Trojan.Win32.Agentb.gen.
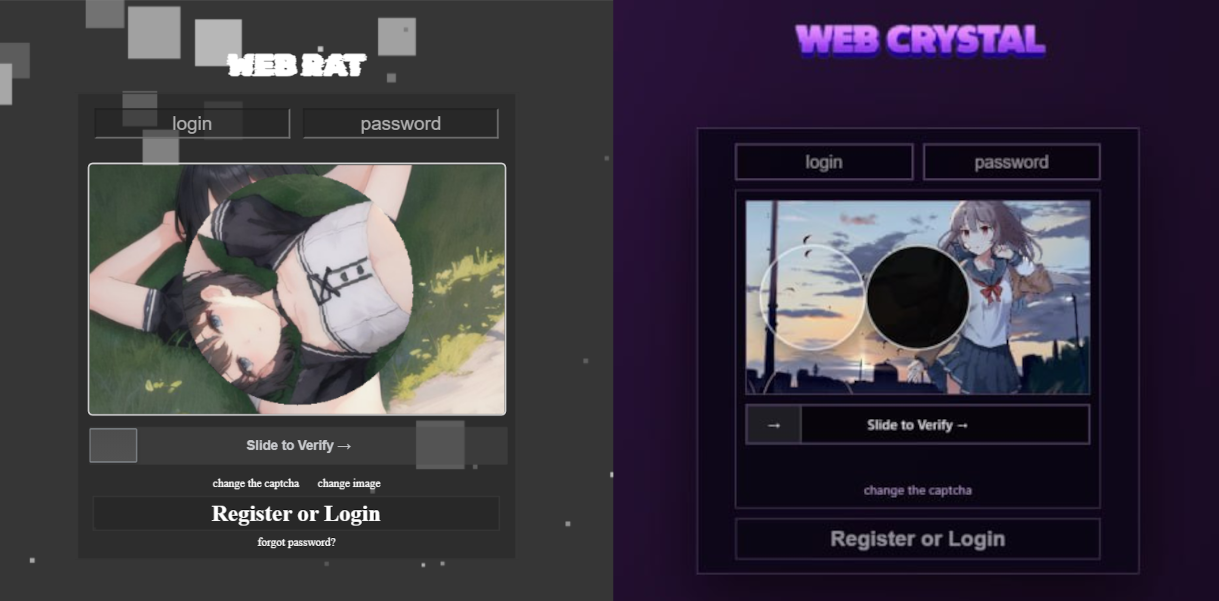
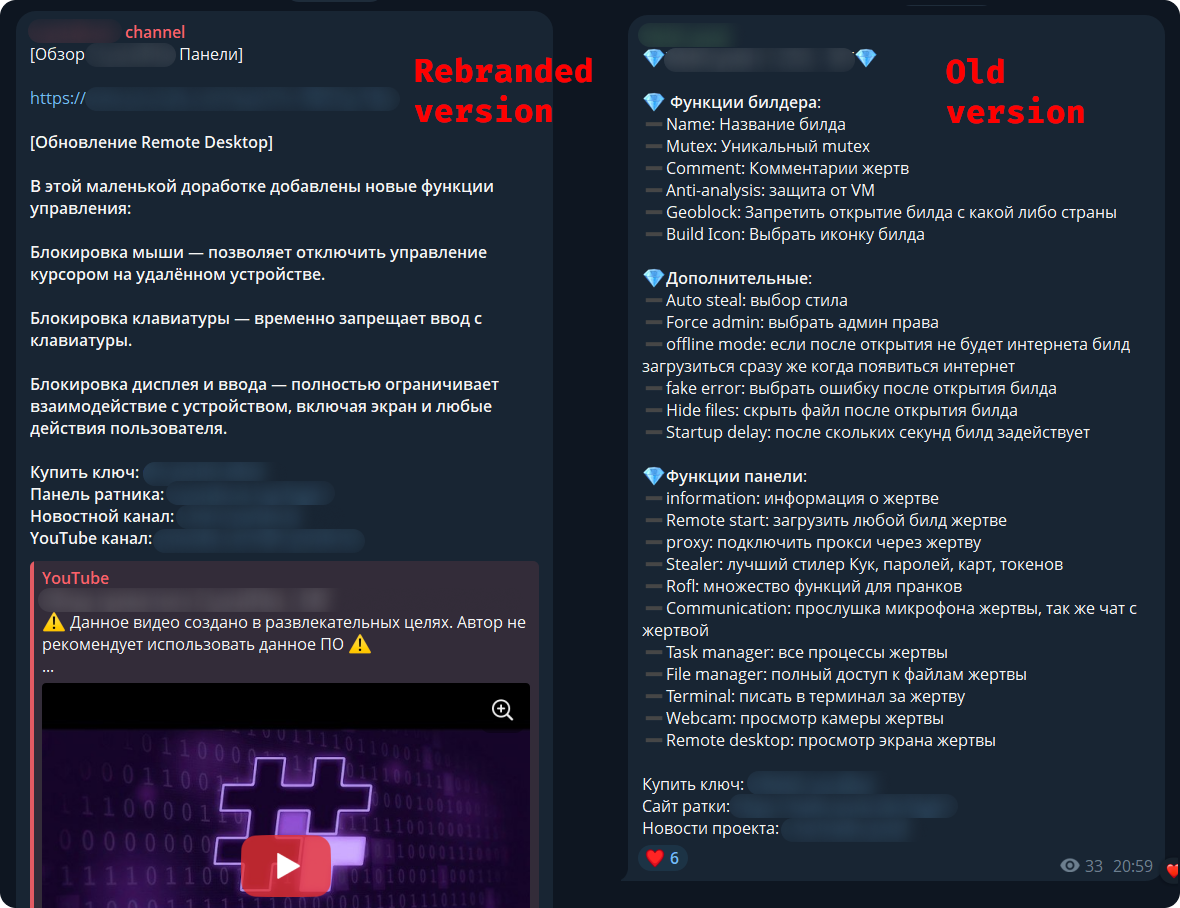
The malware first surfaced in January 2026 under the name Webcrystal RAT in Telegram chats frequented by RAT developers. Its web panel mirrored WebRAT (aka Salat Stealer), another Go-lang RAT, down to bot messages and layout. Skeptics dismissed it as a rip-off. Developers rebranded it CrystalX, shifted to a bustling promo channel with giveaways and polls, and launched a YouTube channel featuring demo videos. This marketing push signals aggressive distribution, potentially drawing in script kiddies beyond elite hackers.
Builder and Evasion Tactics
The control panel offers an auto-builder for customizing implants: geoblock by country, fake icons, and anti-analysis options. Each payload gets zlib compression followed by ChaCha20 encryption using a hardcoded 32-byte key and 12-byte nonce—efficient but not revolutionary, as Go malware often favors such lightweight crypto for cross-platform speed.
Evasion starts basic but stacks effectively. Anti-debug includes an infinite loop scanning for debug flags, ports, hardware breakpoints, and program execution traces. MITM detection probes the registry at HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings for proxy settings, blacklists tools like Fiddler, Burp Suite, and mitmproxy, and hunts for their certificates. VM checks scan running processes, VMware/guest tools, and hardware fingerprints like CPUID leaves. These tricks foil sandboxes and debuggers, letting it persist longer in real environments.
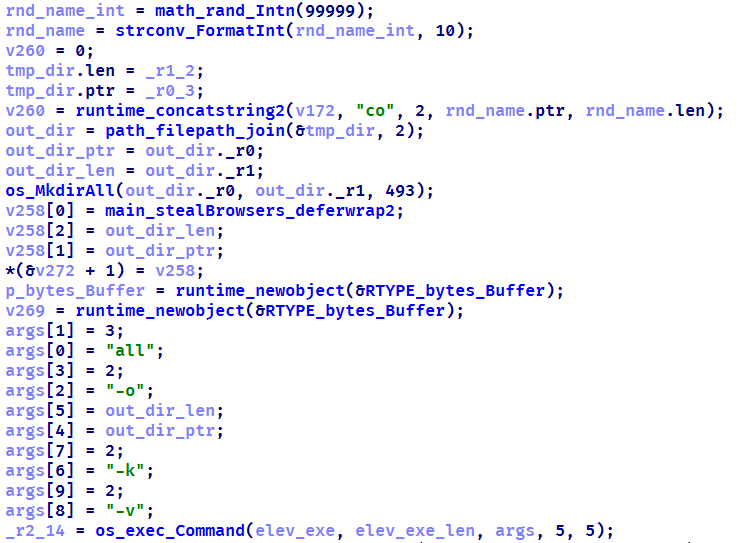
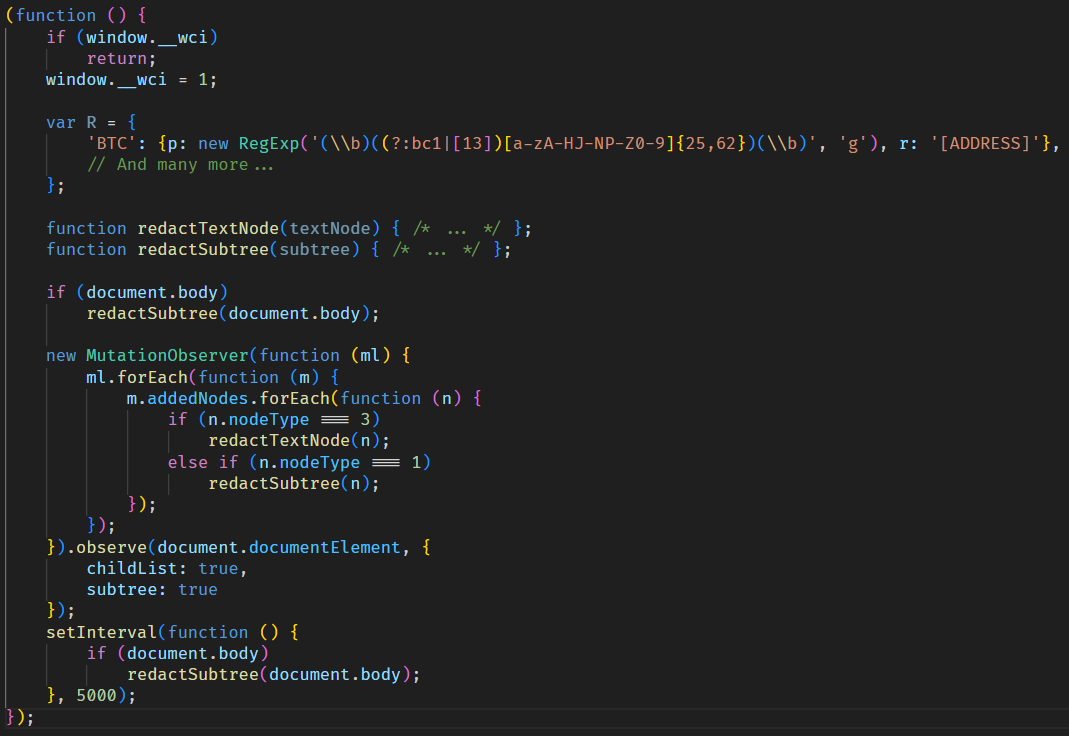
Payload Arsenal
Beyond RAT staples like remote desktop and file exfiltration, CrystalX packs stealers for browser credentials, cookies, and autofill data. Keyloggers capture every keystroke; clippers swap clipboard wallet addresses to reroute crypto payments—a direct threat to users trading Bitcoin or Ethereum. Spyware grabs screenshots, webcam feeds, and microphone audio. Prankware adds absurdity: fake BSOD screens, mouse jiggler, endless pop-ups, and sound loops to troll victims. This mix blurs lines between profit-driven crime and chaos-for-lulz, potentially masking serious theft as harmless mischief.
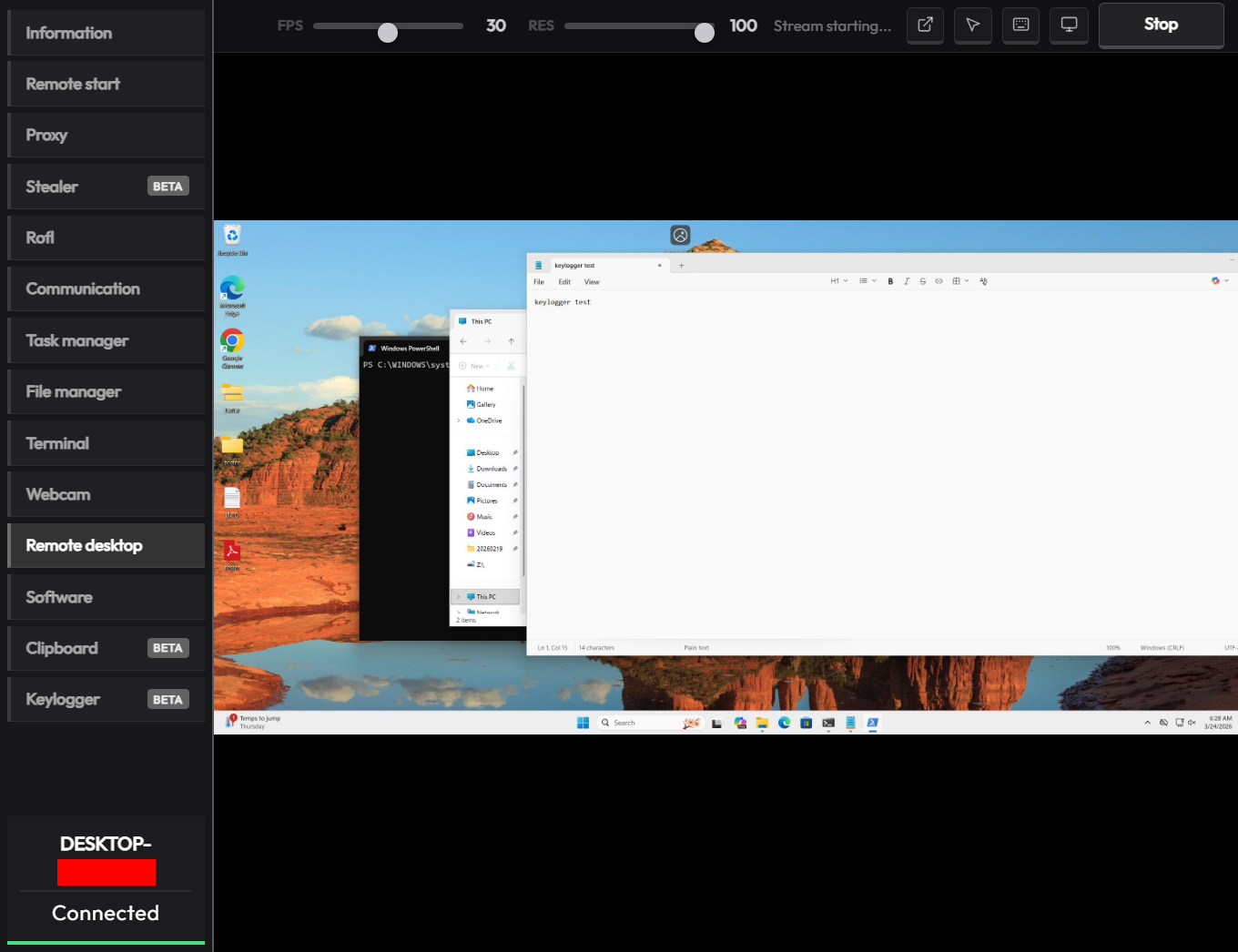
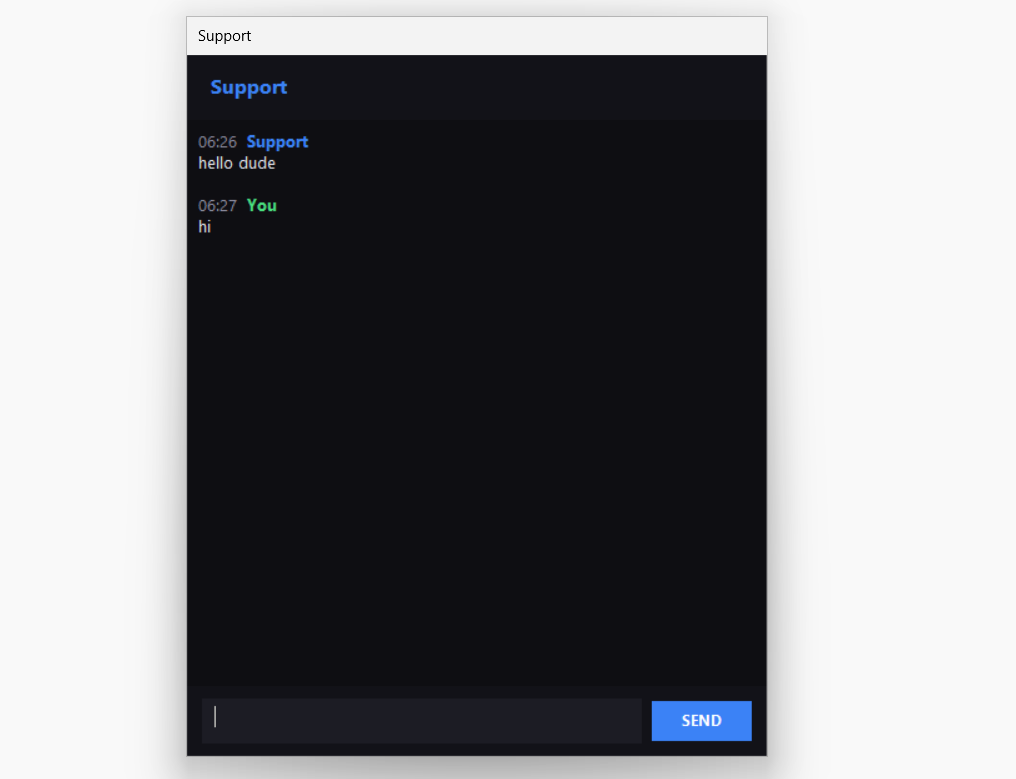
Operators get a polished panel to manage bots, view live streams, and issue commands. Go’s compilation to standalone binaries aids evasion, as seen in prior threats like RustyBuer or Lumma Stealer. CrystalX’s prank focus might encourage social engineering—posing as “fun” pranks in phishing lures—but the stealer core targets high-value data relentlessly.
Implications for Targets and Defenders
This matters because MaaS democratizes advanced threats. Subscriptions make sophisticated tooling cheap—think $50-200/month tiers—amplifying attacks on consumers, crypto holders, and businesses. Clippers alone could siphon thousands in unintended transfers; pair with keyloggers, and 2FA falls fast. Pranks distract victims from spotting real damage, delaying cleanup.
Defenders face a hydra: Go binaries dodge signatures, evasion beats AV heuristics, and Telegram/YouTube promo evades takedowns. Why unique? Few RATs blend enterprise-grade theft with trollware; it appeals to bored affiliates seeking quick wins. Users, enable MFA beyond SMS, watch clipboards during crypto txns, and scan with Kaspersky or EDR like CrowdStrike. Orgs, block Telegram bots and monitor for ChaCha20 artifacts in traffic.
Kaspersky’s report highlights active campaigns—expect variants. IoCs include Telegram channels (track @CrystalX-related), YouTube demos, and panel screenshots matching WebRAT. Full hashes and YARA rules in their post; hunt them now before proliferation.